Protecting Digital Assets Through Software Development Security

Cybersecurity Protecting Digital Assets Pdf Computer Security Software development security plays a crucial role in protecting digital assets, user data, and overall system integrity. in this blog, we will explore how software development security works and the significant ways it helps safeguard the digital frontier. Explore the vital aspects of software development security to safeguard your digital assets. learn best practices to enhance protection.
Protecting Digital Assets Through Software Development Security Learn the best practices for software development security to protect your applications from threats and reduce risks throughout the development lifecycle. Explore the importance of cybersecurity in software development. learn how it protects against digital threats like malware and phishing to keep data safe. Securing software at the development stage, such as applying “ secure by design ” and other security principles, can prevent avoidable harms implicated in online attacks and data breaches. Explore software development security best practices: secure coding guidelines, cybersecurity in software development, and tips for developers to build safer software.

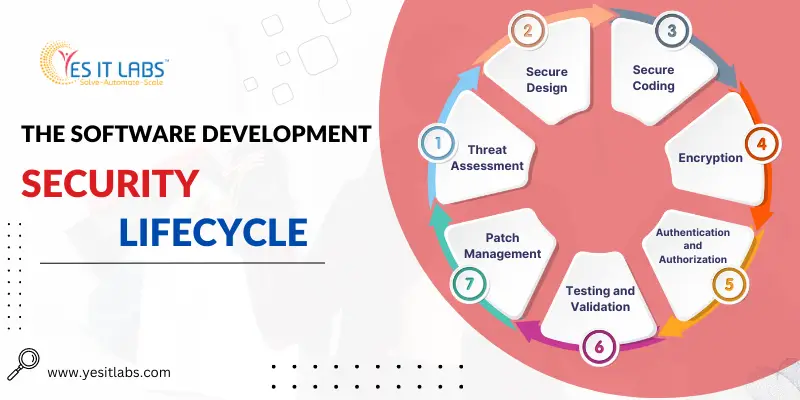
Protecting Digital Assets Through Software Development Security Securing software at the development stage, such as applying “ secure by design ” and other security principles, can prevent avoidable harms implicated in online attacks and data breaches. Explore software development security best practices: secure coding guidelines, cybersecurity in software development, and tips for developers to build safer software. Explore the essential role of cybersecurity in custom software development. learn how proactive security measures, risk assessment, secure coding, and compliance can safeguard your digital assets and enhance trust with your users. So, how do experts secure their software development life cycle (sdlc)? this blog post will list down some security best practices and frameworks that you should follow while developing your software applications. How to secure products? part 1: foundations of secure product design threat modeling during the early stages of development, identifying threats and vulnerabilities ensures the product is designed with security in mind. identifying assets, threats, and attack vectors: assets: determine what needs protection (e.g., sensitive data, apis). Software security involves crafting and designing software that guarantees the integrity, confidentiality, and availability of its code, data, and functionalities. often, in prioritizing.

Protecting Digital Assets Through Software Development Security Explore the essential role of cybersecurity in custom software development. learn how proactive security measures, risk assessment, secure coding, and compliance can safeguard your digital assets and enhance trust with your users. So, how do experts secure their software development life cycle (sdlc)? this blog post will list down some security best practices and frameworks that you should follow while developing your software applications. How to secure products? part 1: foundations of secure product design threat modeling during the early stages of development, identifying threats and vulnerabilities ensures the product is designed with security in mind. identifying assets, threats, and attack vectors: assets: determine what needs protection (e.g., sensitive data, apis). Software security involves crafting and designing software that guarantees the integrity, confidentiality, and availability of its code, data, and functionalities. often, in prioritizing.

Cybersecurity Protecting Digital Assets Premium Ai Generated Image How to secure products? part 1: foundations of secure product design threat modeling during the early stages of development, identifying threats and vulnerabilities ensures the product is designed with security in mind. identifying assets, threats, and attack vectors: assets: determine what needs protection (e.g., sensitive data, apis). Software security involves crafting and designing software that guarantees the integrity, confidentiality, and availability of its code, data, and functionalities. often, in prioritizing.
Comments are closed.