Privilege Escalation Techniques 10 Linux Kernel Exploits

Free Video Linux Red Team Privilege Escalation Techniques Kernel This tryhackme room covers privilege escalation techniques on linux systems. in this activity, we focus on exploiting a kernel vulnerability to gain root access. By understanding common techniques—such as kernel exploits, misconfigured services, suid misuse, sudo misconfigurations, and cron job vulnerabilities—you can better secure systems against these threats.
How To Conduct Linux Privilege Escalations Techtarget Privilege escalation is a critical phase in penetration testing where an attacker attempts to gain higher level permissions than initially obtained. this guide covers advanced techniques for escalating privileges on linux systems. Privilege escalation techniques series | kernel exploits now we are beginning with little bit complex thing: kernel! for who don’t know what kernel is, it’s simply a software which runs. It consolidates various techniques and methods to identify and exploit potential paths for privilege escalation, helping users quickly assess and enhance the security of linux systems. Gtfoargs: argument injection exploitation vector list | gtfoargs is a curated list of unix binaries whose arguments can be exploited for argument injection, enabling shell escapes, privilege escalation, file read write, and other post exploitation techniques.

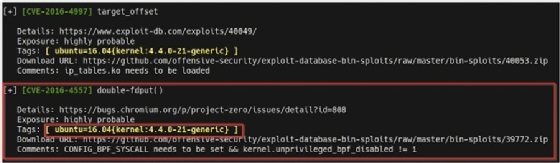
ёэрдёэрлёэрлёэриёэроёэру Linux Privilege Escalation Exploit Misconfigurations Elevate It consolidates various techniques and methods to identify and exploit potential paths for privilege escalation, helping users quickly assess and enhance the security of linux systems. Gtfoargs: argument injection exploitation vector list | gtfoargs is a curated list of unix binaries whose arguments can be exploited for argument injection, enabling shell escapes, privilege escalation, file read write, and other post exploitation techniques. A practical guide to linux privilege escalation techniques using kernel exploits, misconfigurations, and automated tools like linpeas and linenum. Linux security & privilege escalation relevant source files this section documents the methodologies, vectors, and technical implementations for assessing linux security and achieving privilege escalation. it covers system enumeration, kernel exploitation, service specific vulnerabilities (grafana, logstash, ipsec), and post exploitation. Gtfobins is a collection of scripts that can be used to bypass local security restrictions in various applications and services. these scripts leverage various features or misconfigurations in these applications to allow an attacker to run arbitrary commands with escalated privileges. view the contents of the other cron job script:. In this post we will be exploring various kernel exploits that can be used for linux privilege escalation from standard user to root. we will start by using various commands to find the kernel version on the victim host.

Linux Privilege Escalation Kernel Exploits Steflan S Security Blog A practical guide to linux privilege escalation techniques using kernel exploits, misconfigurations, and automated tools like linpeas and linenum. Linux security & privilege escalation relevant source files this section documents the methodologies, vectors, and technical implementations for assessing linux security and achieving privilege escalation. it covers system enumeration, kernel exploitation, service specific vulnerabilities (grafana, logstash, ipsec), and post exploitation. Gtfobins is a collection of scripts that can be used to bypass local security restrictions in various applications and services. these scripts leverage various features or misconfigurations in these applications to allow an attacker to run arbitrary commands with escalated privileges. view the contents of the other cron job script:. In this post we will be exploring various kernel exploits that can be used for linux privilege escalation from standard user to root. we will start by using various commands to find the kernel version on the victim host.
Linux Privilege Escalation With Kernel Exploits Zsecurity Gtfobins is a collection of scripts that can be used to bypass local security restrictions in various applications and services. these scripts leverage various features or misconfigurations in these applications to allow an attacker to run arbitrary commands with escalated privileges. view the contents of the other cron job script:. In this post we will be exploring various kernel exploits that can be used for linux privilege escalation from standard user to root. we will start by using various commands to find the kernel version on the victim host.
Github Jlsakuya Linux Privilege Escalation Exploits Linux Privilege
Comments are closed.