Preventing Ip Spoofing

Unraveling The Secrets Of Ip Address Spoofing Pdf Security Learn how to prevent ip address spoofing and what goes into ip address spoofing attacks. get the best tips on ip address spoofing prevention and more. Attackers use ip spoofing to send malware and bots to your protected network, to execute dos attacks, or to gain unauthorized access. anti spoofing detects if a packet with an ip address that is behind a certain interface, arrives from a different interface.

Ip Spoofing Attack Explanation Protection Gridinsoft Blogs To help prevent ip spoofing, you should use a vpn to hide your ip address. then, monitor your network for suspicious activity with a firewall, which uses a packet filter that inspects ip packet headers. Uncover the hidden world of ip spoofing: learn how cybercriminals mask identities, exploit networks, and what you can do to protect your digital security. Ip spoofing steals the identity of data packets, making it difficult to know the origin of data flows and opening the door to interception attacks. learn how these damaging network security threats work and ways to detect and prevent ip spoofing attacks. Learn effective strategies to prevent ip spoofing attacks, including firewall rules, packet filtering, and network monitoring best practices.
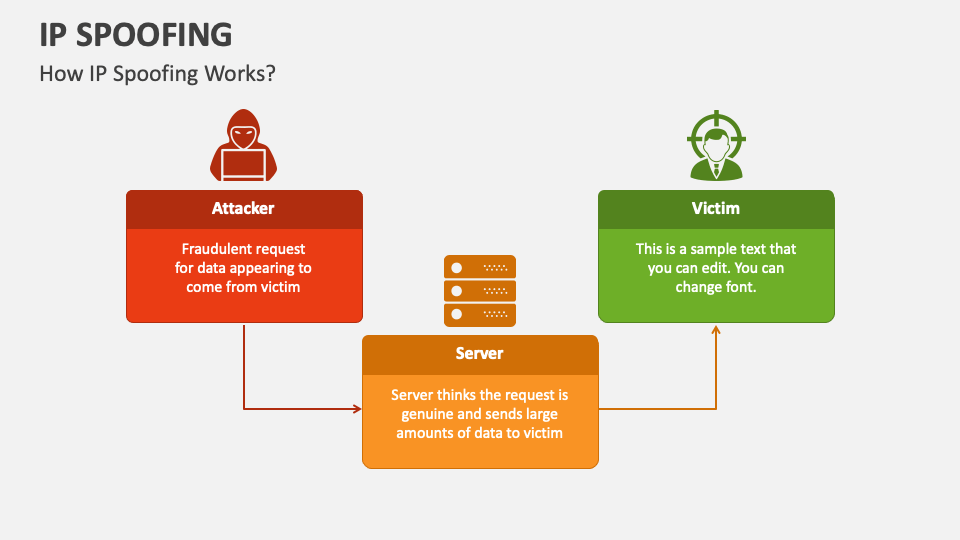
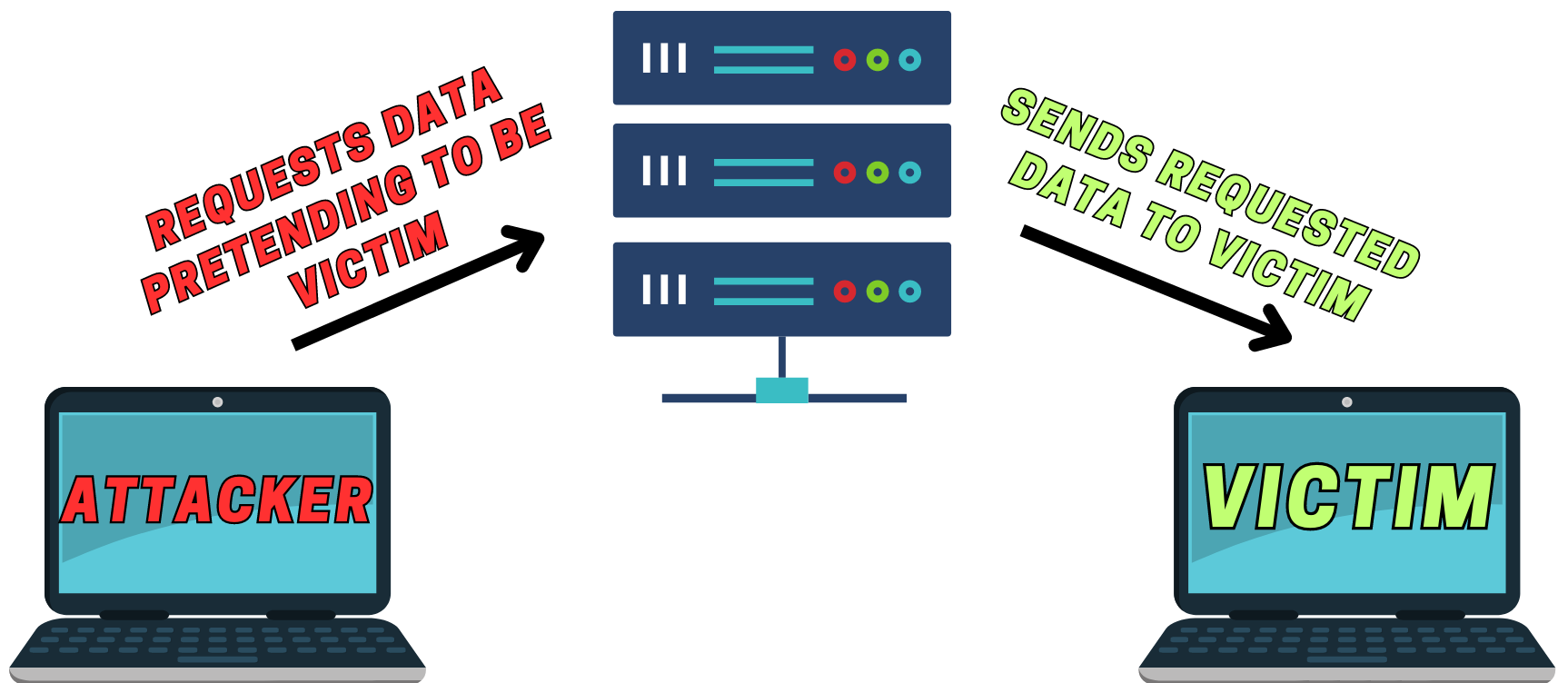
Ip Spoofing Powerpoint And Google Slides Template Ppt Slides Ip spoofing steals the identity of data packets, making it difficult to know the origin of data flows and opening the door to interception attacks. learn how these damaging network security threats work and ways to detect and prevent ip spoofing attacks. Learn effective strategies to prevent ip spoofing attacks, including firewall rules, packet filtering, and network monitoring best practices. Learn about ip spoofing, how it works, how to detect and prevent it, and other types of spoofing attacks to watch out for. Simple ip spoofing prevention methods to secure your network with defenses — learn easy detection techniques to start protecting your systems. Packet filtering, network monitoring, and secure encryption protocols can lower the risk of attacker spoofing. to fight ip spoofing, combining multiple anti spoofing techniques works best. awareness training is also key. it helps users understand the threat and supports technical defenses. Proper network configuration is crucial in preventing ip spoofing attacks. this includes implementing ingress and egress filtering to ensure that incoming and outgoing traffic is legitimate.

How To Prevent Ip Spoofing 7 Steps With Pictures Wikihow Tech Learn about ip spoofing, how it works, how to detect and prevent it, and other types of spoofing attacks to watch out for. Simple ip spoofing prevention methods to secure your network with defenses — learn easy detection techniques to start protecting your systems. Packet filtering, network monitoring, and secure encryption protocols can lower the risk of attacker spoofing. to fight ip spoofing, combining multiple anti spoofing techniques works best. awareness training is also key. it helps users understand the threat and supports technical defenses. Proper network configuration is crucial in preventing ip spoofing attacks. this includes implementing ingress and egress filtering to ensure that incoming and outgoing traffic is legitimate.
Ip Spoofing Tutorial Hackblue Packet filtering, network monitoring, and secure encryption protocols can lower the risk of attacker spoofing. to fight ip spoofing, combining multiple anti spoofing techniques works best. awareness training is also key. it helps users understand the threat and supports technical defenses. Proper network configuration is crucial in preventing ip spoofing attacks. this includes implementing ingress and egress filtering to ensure that incoming and outgoing traffic is legitimate.

How To Prevent Ip Spoofing 7 Steps With Pictures Wikihow Tech
Comments are closed.