Presentation Cloud Computing Models Security Issues
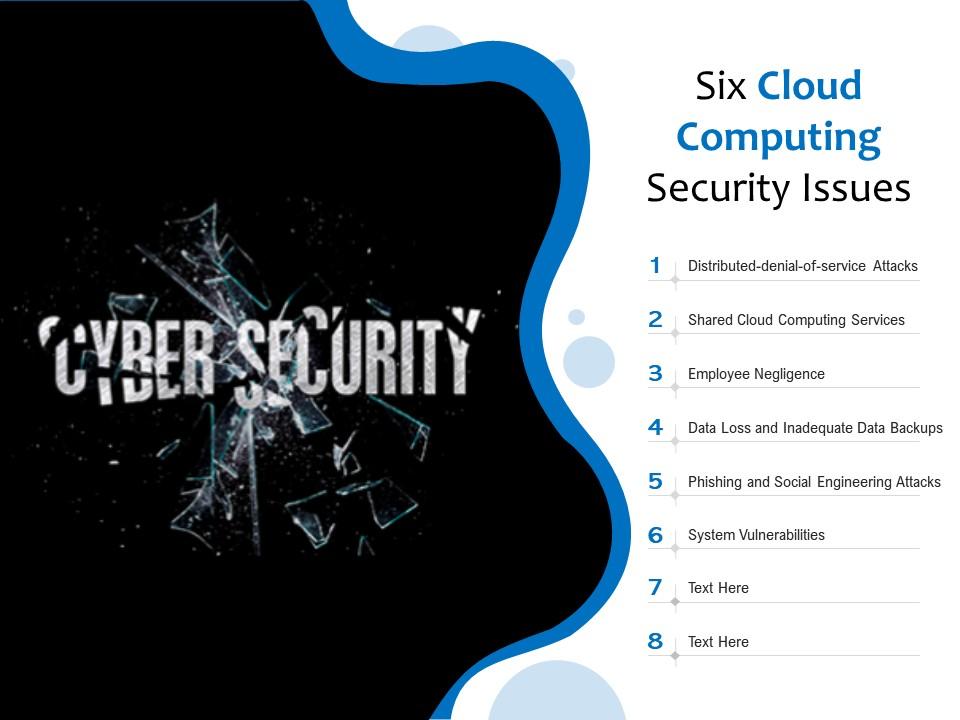
Six Cloud Computing Security Issues Presentation Graphics This document discusses security issues and challenges in cloud computing. it outlines the three main cloud deployment models (private, public, hybrid cloud) and three service delivery models (iaas, paas, saas). The document discusses security issues related to cloud computing. it covers topics such as computer security services including confidentiality, integrity and availability.
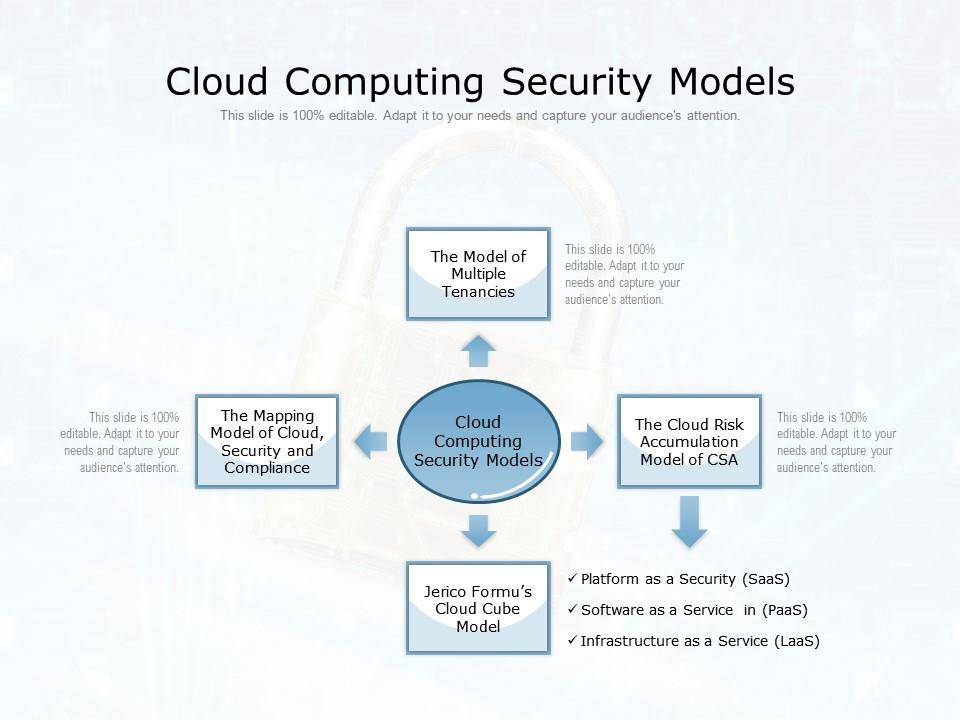
Cloud Computing Security Models Presentation Graphics Powerpoint Explore cloud computing security risks, from data loss to unauthorized access, and learn how to protect sensitive information in the cloud environment. discover the differences between traditional systems security and cloud security measures. Our fully editable and customizable powerpoint presentations on cloud computing security provide a comprehensive overview of the best practices, technologies, and strategies necessary to safeguard cloud environments. In this, we will discuss the overview of cloud computing, its need, and mainly our focus to cover the security issues in cloud computing. let's discuss it one by one. New approaches to mobile cloud computing in which applications lie in the cloud as opposed to on a smart phone, enable more sophisticated security mechanisms. users connect to the cloud from their local host machines.
Cloud Computing Security Issues Ppt Powerpoint Presentation Slides Grid In this, we will discuss the overview of cloud computing, its need, and mainly our focus to cover the security issues in cloud computing. let's discuss it one by one. New approaches to mobile cloud computing in which applications lie in the cloud as opposed to on a smart phone, enable more sophisticated security mechanisms. users connect to the cloud from their local host machines. May be difficult in cloud computing because logging and data for multiple customers may be co located may also be geographically spread across an ever changing set of hosts and data centers. solution get a contractual commitment to support specific forms of investigation, along with evidence that the vendor has already. This helps you give your presentation on security issues in cloud computing in a conference, a school lecture, a business proposal, in a webinar and business and professional representations. If predictive models fail, the cloud provider service can fail for a long period. no policies for resource capping if there is not a flexible and configurable way for the customer and or the cloud provider to set limits on resources, this can be problematic when resource use is unpredictable. Threat model in cloud computing materials and methods. this section explores the security dimensions, distinct security zones, threats, and challenges associated with cloud computing.
Cloud Computing Security Issues Challenges Ppt Powerpoint Presentation May be difficult in cloud computing because logging and data for multiple customers may be co located may also be geographically spread across an ever changing set of hosts and data centers. solution get a contractual commitment to support specific forms of investigation, along with evidence that the vendor has already. This helps you give your presentation on security issues in cloud computing in a conference, a school lecture, a business proposal, in a webinar and business and professional representations. If predictive models fail, the cloud provider service can fail for a long period. no policies for resource capping if there is not a flexible and configurable way for the customer and or the cloud provider to set limits on resources, this can be problematic when resource use is unpredictable. Threat model in cloud computing materials and methods. this section explores the security dimensions, distinct security zones, threats, and challenges associated with cloud computing.
Comments are closed.