Practice Exercises Cryptography 23 Self Practice Exercises

Practice Activity Cryptography Pdf On studocu you find all the lecture notes, summaries and study guides you need to pass your exams with better grades. Exercise 12: your opponent has invented a new stream cipher mode of operation for 128 bit key aes. he thinks that ofb could be improved by feeding back into the key port rather than the data port of the aes chip.

Exercises Meeting 9 14 Pdf Cryptography Encryption The document contains 26 exercises related to cryptography and cipher techniques: exercise 1 asks to compute the gcd of two numbers using euclid's and extended euclid's algorithms. exercises 2 4 involve encrypting decrypting messages using vigenere and simple substitution ciphers. Second, we observe that if the oracle o of d′ is the function f described in the exercise then, for all k, we have that pr(d′fk(·)(1n) = 1) = 1 because k ∨ 1n is always equal to 1n. Classical ciphers: simple algorithms (military, ordinary citizen, ). modern ciphers: computer cryptography. yesterday: exclusive domain of the militaries, governments, today: state of the art cryptography accessible to all. Explore practice exercises in security and cryptography, covering key management, rsa, and cryptographic protocols to enhance learning outcomes.
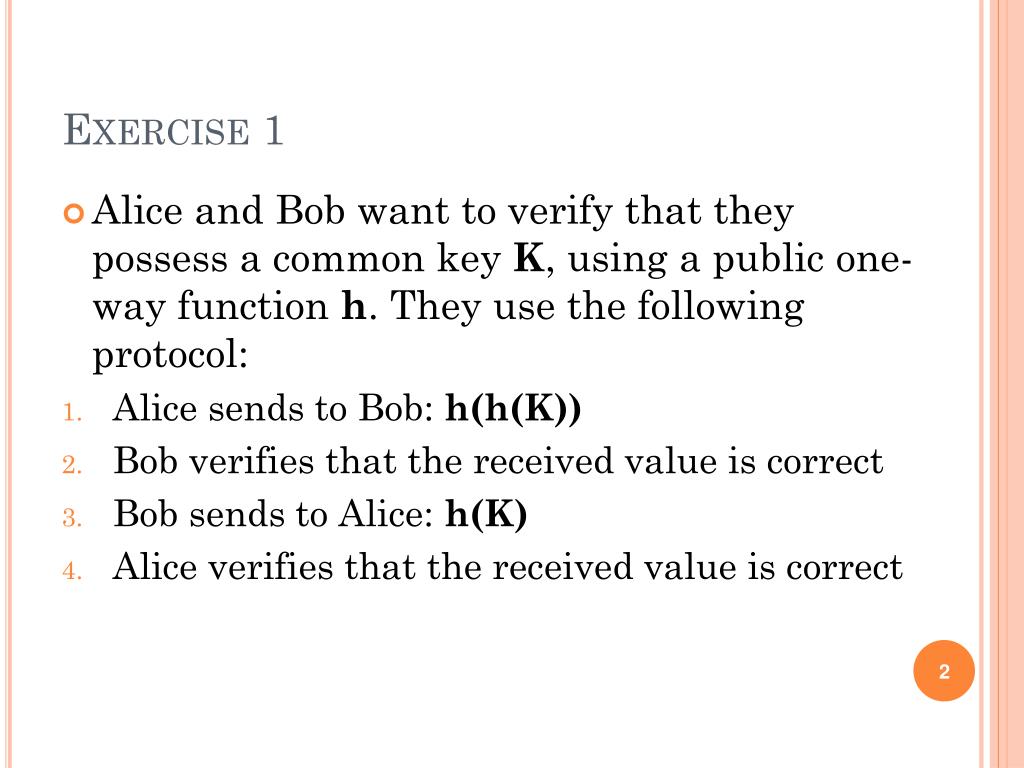
Ppt Exercises Basic Cryptography Key Exchange Protocols Powerpoint Classical ciphers: simple algorithms (military, ordinary citizen, ). modern ciphers: computer cryptography. yesterday: exclusive domain of the militaries, governments, today: state of the art cryptography accessible to all. Explore practice exercises in security and cryptography, covering key management, rsa, and cryptographic protocols to enhance learning outcomes. Master caesar cipher with 25 hands on practice problems, step by step solutions, and programming examples. from basic encryption to advanced frequency analysis and brute force decryption techniques. Learning outcomes in this module, you will complete the following exercises: exercise 1 knowing the cryptographic concepts exercise 2 implementing cryptography exercise 3 using steganography after completing this module, you should be able to: encrypt data using cryptodemo decrypt data using cryptodemo key values perform hashing use. Exercise 1 (shift cipher). a secret message m is encrypted with the shift cipher using a secret key k. Cryptography worksheet people have always been interested in writing secret messages. in ancient times, people had to write secret messages to keep messengers and interceptors from reading their private information.

Solution Cryptography 101 From Theory To Practice Studypool Master caesar cipher with 25 hands on practice problems, step by step solutions, and programming examples. from basic encryption to advanced frequency analysis and brute force decryption techniques. Learning outcomes in this module, you will complete the following exercises: exercise 1 knowing the cryptographic concepts exercise 2 implementing cryptography exercise 3 using steganography after completing this module, you should be able to: encrypt data using cryptodemo decrypt data using cryptodemo key values perform hashing use. Exercise 1 (shift cipher). a secret message m is encrypted with the shift cipher using a secret key k. Cryptography worksheet people have always been interested in writing secret messages. in ancient times, people had to write secret messages to keep messengers and interceptors from reading their private information.

Cryptography Exercises Docx Official Open Cryptography Exercises 1 Exercise 1 (shift cipher). a secret message m is encrypted with the shift cipher using a secret key k. Cryptography worksheet people have always been interested in writing secret messages. in ancient times, people had to write secret messages to keep messengers and interceptors from reading their private information.

Yc 23 Self Practice Guide Pdf Asana Ashtanga Vinyasa Yoga
Comments are closed.