Practical Malware Analysis Ch 5 Ida Pro Pptx Programming
Practical Malware Analysis Ch 5 Ida Pro Pptx Functions can be analyzed by examining parameters, calls, and cross references. the disassembly can be enhanced through renaming locations, adding comments, and using named constants. ida supports plugins for extended functionality. download as a pptx, pdf or view online for free. Using named constants • makes windows api arguments clearer extending ida with plug ins • idc (ida's scripting language) and python scripts available (link ch 6a).
Practical Malware Analysis Ch 5 Ida Pro Pptx Practical malware analysis practical malware analysis ch 5: ida pro ida pro versions full featured pay version old free version both support x86 pay version supports x64…. The goal of this lab is to give you hands on experience with ida pro. if you’ve already worked with ida pro, you may choose to ignore these questions and focus on reverse engineering the malware. Chapter 5 of 'practical malware analysis' focuses on the use of ida pro, detailing its features such as graph and text modes, code signatures, and window management for effective malware analysis. This details reverse engineering activities and answers for labs contained in the book ‘practical malware analysis’ by michael sikorski and andrew honig, which is published by no starch press.
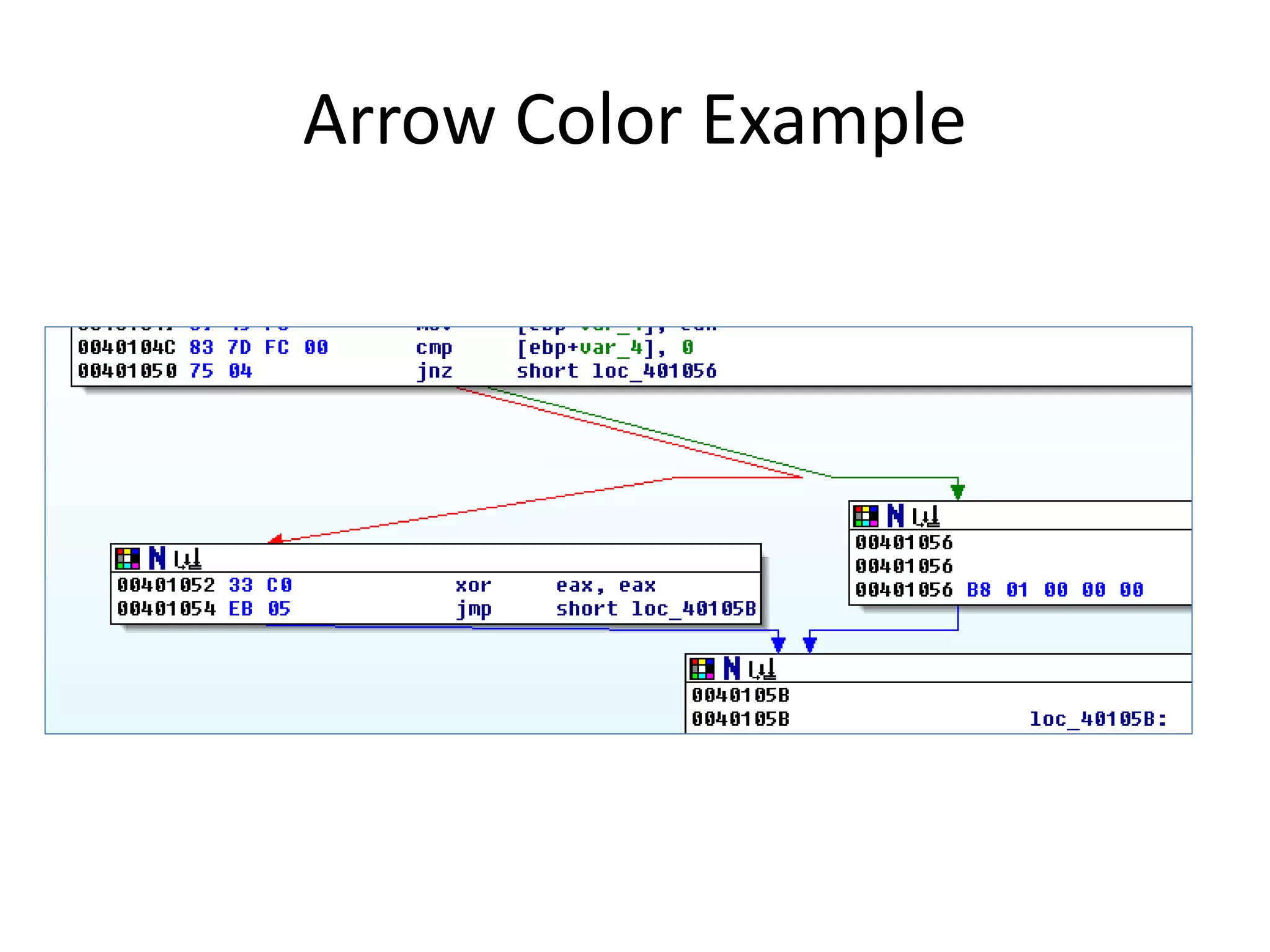
Practical Malware Analysis Ch 5 Ida Pro Pptx Chapter 5 of 'practical malware analysis' focuses on the use of ida pro, detailing its features such as graph and text modes, code signatures, and window management for effective malware analysis. This details reverse engineering activities and answers for labs contained in the book ‘practical malware analysis’ by michael sikorski and andrew honig, which is published by no starch press. The malware might try to detect, using this function, how much time has elapsed since its execution. this can be an anti analysis tactic that tries to prevent the debugging of the malware. Solutions for lab 5 within practical malware analysis. ida pro, an interactive disassembler, is a disassembler for computer programs that generates assembly language source code from an. Practical malware analysis: ch 5: ida pro free download as pdf file (.pdf), text file (.txt) or view presentation slides online. The third chapter to contain lab assignments is chapter 5: “ida pro”. as the name suggests, this chapter discusses the use of the interactive disassembler tool. ida’s true power comes from its interactive ability, and the book gives tips and tricks to assist in performing analysis with ida.
Comments are closed.