Practical Cryptographic Systems 18 Sep 2017

Quantum Cryptographic Systems Pdf Quantum Computing Cryptography Please submit the completed assignment via blackboard. problem 1: warm up: implement a cryptographic specification (30 points). implement the following specification for encrypting and decrypting messages. you must implement your project in the go language. We set out to design a system that will be used for 30 years, and the data must be kept secure for 20 years after it was first processed. the symmetric key size must be chosen large enough to protect the data up to 50 years from now.
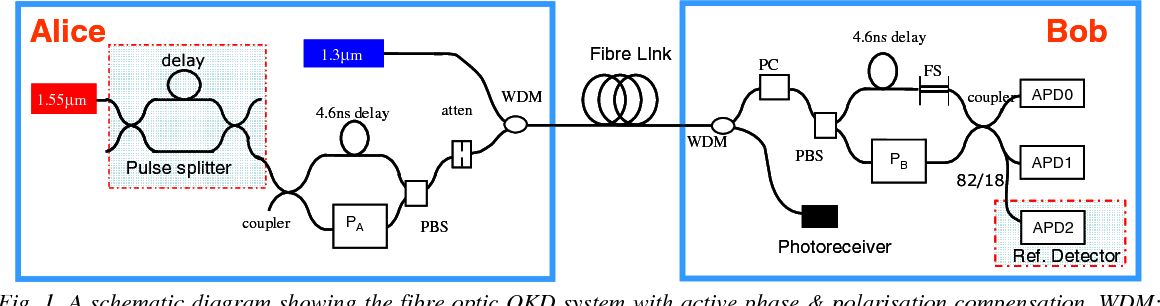
Figure 1 From Practical One Way Quantum Cryptographic System For Security is the number one concern for businesses worldwide. the gold standard for attaining security is cryptography because it provides the most reliable tools for storing or transmitting digital information. The dramatic increase of information transmitted electronically has led to an increased reliance on cryptography. this book discusses the theories and concepts behind modern cryptography and demonstrates how to develop and implement cryptographic algorithms using c programming language. Programming assignments for the practical cryptographic systems course taught by dr. matthew green. This book emphasizes practical application, omitting exhaustive mathematical de scriptions of the underlying algorithms, except in part iii (post quantum cryptography).
Exercise Cryptographic Basics Blockchain Based Systems Engineering Programming assignments for the practical cryptographic systems course taught by dr. matthew green. This book emphasizes practical application, omitting exhaustive mathematical de scriptions of the underlying algorithms, except in part iii (post quantum cryptography). They delve into various cryptographic algorithms and techniques, including encryption, authentication, and digital signatures, and provide guidance on how to make choices that are secure, efficient, and suitable for the specific context. We describe common mistakes to avoid as well as attacks on real world systems that illustrate the importance of rigor in cryptography. we end every chapter with a fun application that applies the ideas in the chapter in some unexpected way. One of the asymmetric algorithm types, elliptic curve cryptography, or ecc, appears to be secure with shorter keys than those needed by other asymmetric key algorithms. The following two chapters explain public key cryptographic systems; un fortunately, this requires quite a bit of mathematics. it is always tempting to dispense with the understanding and only present the formulas and equa tions, but we feel very strongly that this is a dangerous thing to do.

Exploring Cryptographic Algorithms Protocols A Practical Course Hero They delve into various cryptographic algorithms and techniques, including encryption, authentication, and digital signatures, and provide guidance on how to make choices that are secure, efficient, and suitable for the specific context. We describe common mistakes to avoid as well as attacks on real world systems that illustrate the importance of rigor in cryptography. we end every chapter with a fun application that applies the ideas in the chapter in some unexpected way. One of the asymmetric algorithm types, elliptic curve cryptography, or ecc, appears to be secure with shorter keys than those needed by other asymmetric key algorithms. The following two chapters explain public key cryptographic systems; un fortunately, this requires quite a bit of mathematics. it is always tempting to dispense with the understanding and only present the formulas and equa tions, but we feel very strongly that this is a dangerous thing to do.
Comments are closed.