Practical Api Security Discover Defend And Secure Apis From Code To
Practical Api Security Discover Defend And Secure Apis From Code To This lab explores how to discover, document, and secure both known and shadow apis using the platform's api discovery, schema validation, and security dashboards. Whether you’re a developer, security professional, or architect, this course provides the comprehensive security foundation needed to design, build, and maintain secure api ecosystems in today’s threat landscape.
A Comprehensive Guide To Secure Your Apis This session covers the owasp api security top ten, highlights the most important risks for web applications and apis, and provides practical countermeasures. learn how to identify, prioritize, and defend against vulnerabilities to make your api architecture robust against attacks. In this course, you will learn to: identify, exploit, and protect against a wide variety of api security vulnerabilities. gain a practical understanding of api security and the. Comprehensive api security tutorial for developers and security teams. learn strategies to defend against vulnerabilities and secure your api lifecycle. The api security project focuses on strategies and solutions to understand and mitigate the unique vulnerabilities and security risks of application programming interfaces (apis).
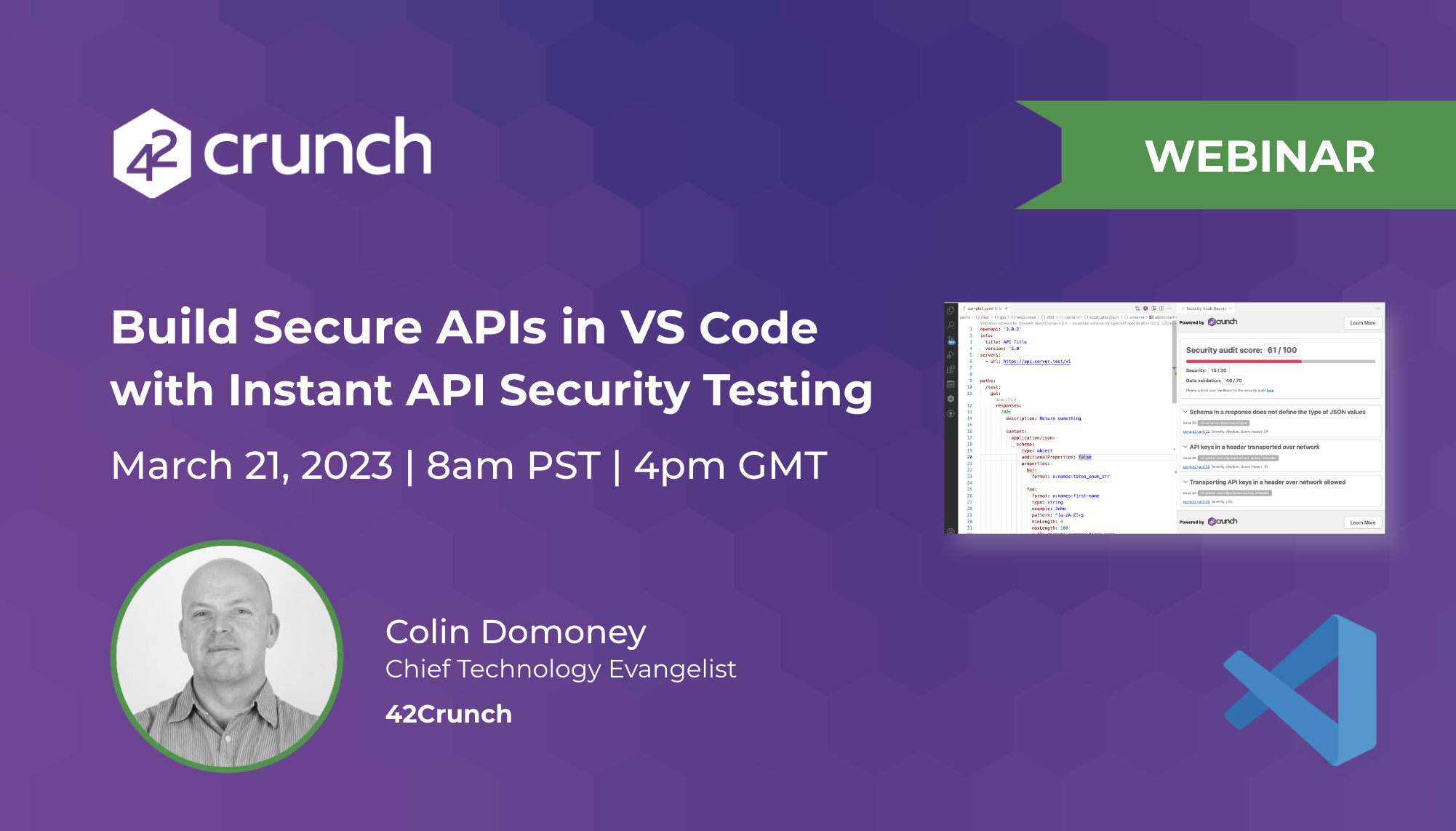
Webinar Build Secure Apis In Vs Code With Instant Api Security Comprehensive api security tutorial for developers and security teams. learn strategies to defend against vulnerabilities and secure your api lifecycle. The api security project focuses on strategies and solutions to understand and mitigate the unique vulnerabilities and security risks of application programming interfaces (apis). This course provides api developers and full stack developers with the necessary knowledge to assess and improve the security of their applications. with a mix of lectures, demos, quizzes, and cheat sheets, participants discover best practices for building secure apis. This blog post is your no fluff, defense first roadmap to securing apis in real world devsecops environments. whether you're building or protecting apis, these tips will help you reduce risk, outsmart bots, and improve your appsec hygiene. Master api security from design to runtime. secure rest, graphql, grpc, and webhooks. map owasp api top 10 to controls and tests, enforce schemas, discover shadow apis, add abuse protections, automate evidence, and measure slos. This 2025 guide explains what api security really means, why it matters so much, the key risks (including the owasp api security top 10), and practical ways to protect, test, and monitor your apis.
Unlock The Power Of Apis With Secure Design Principles Why Api This course provides api developers and full stack developers with the necessary knowledge to assess and improve the security of their applications. with a mix of lectures, demos, quizzes, and cheat sheets, participants discover best practices for building secure apis. This blog post is your no fluff, defense first roadmap to securing apis in real world devsecops environments. whether you're building or protecting apis, these tips will help you reduce risk, outsmart bots, and improve your appsec hygiene. Master api security from design to runtime. secure rest, graphql, grpc, and webhooks. map owasp api top 10 to controls and tests, enforce schemas, discover shadow apis, add abuse protections, automate evidence, and measure slos. This 2025 guide explains what api security really means, why it matters so much, the key risks (including the owasp api security top 10), and practical ways to protect, test, and monitor your apis.
Comments are closed.