Ppt Network Packet Reconstruction Technology For Computer Forensics
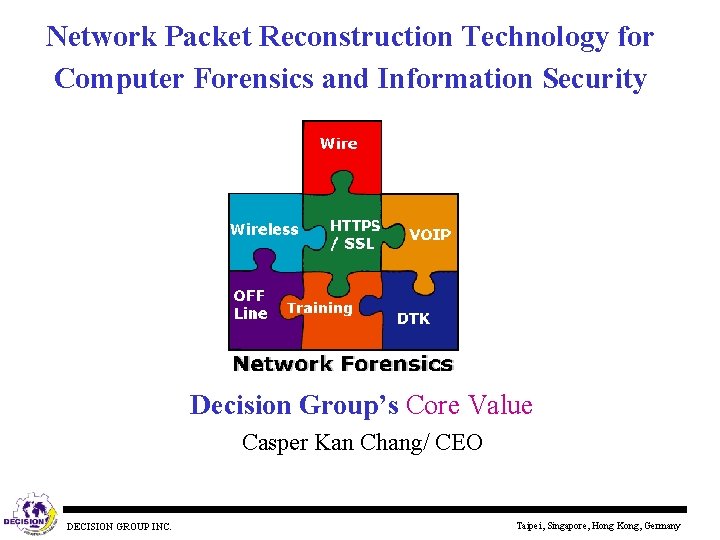
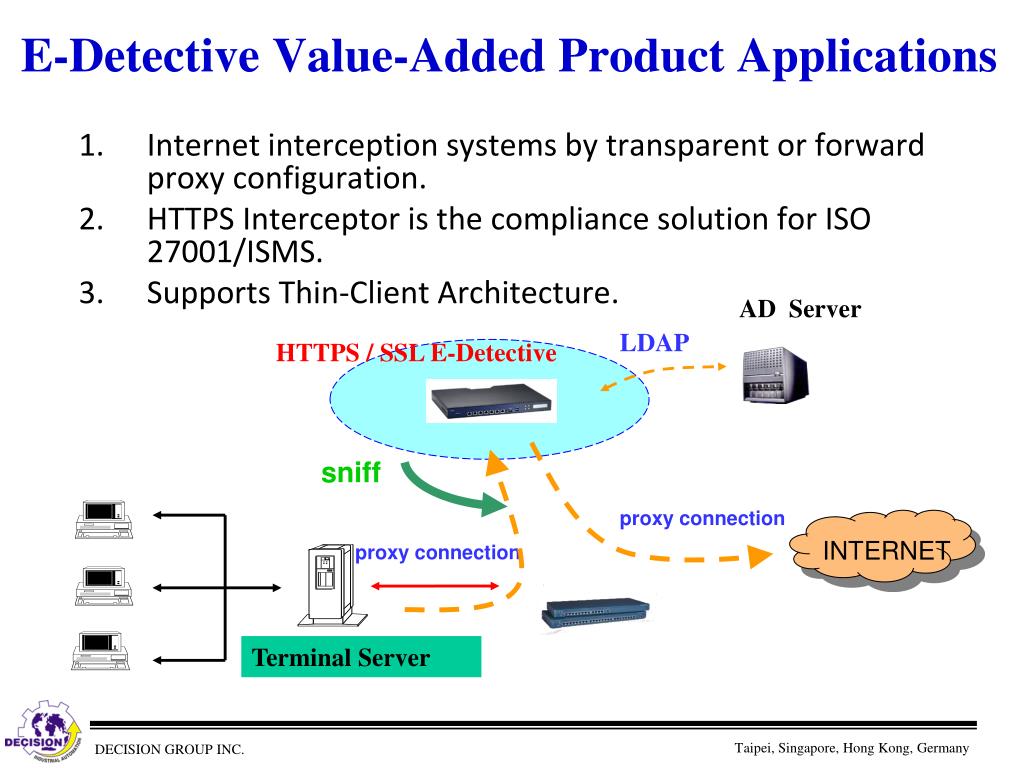
Network Packet Reconstruction Technology For Computer Forensics And Core values of e detective product series the most complete product series and solutions for network packet reconstruction in the world. supports network forensics and information security auditing standards. The document discusses network packet reconstruction technology for computer forensics and information security. it summarizes decision group's product offerings which allow capturing, organizing, and replaying network packets for analysis.
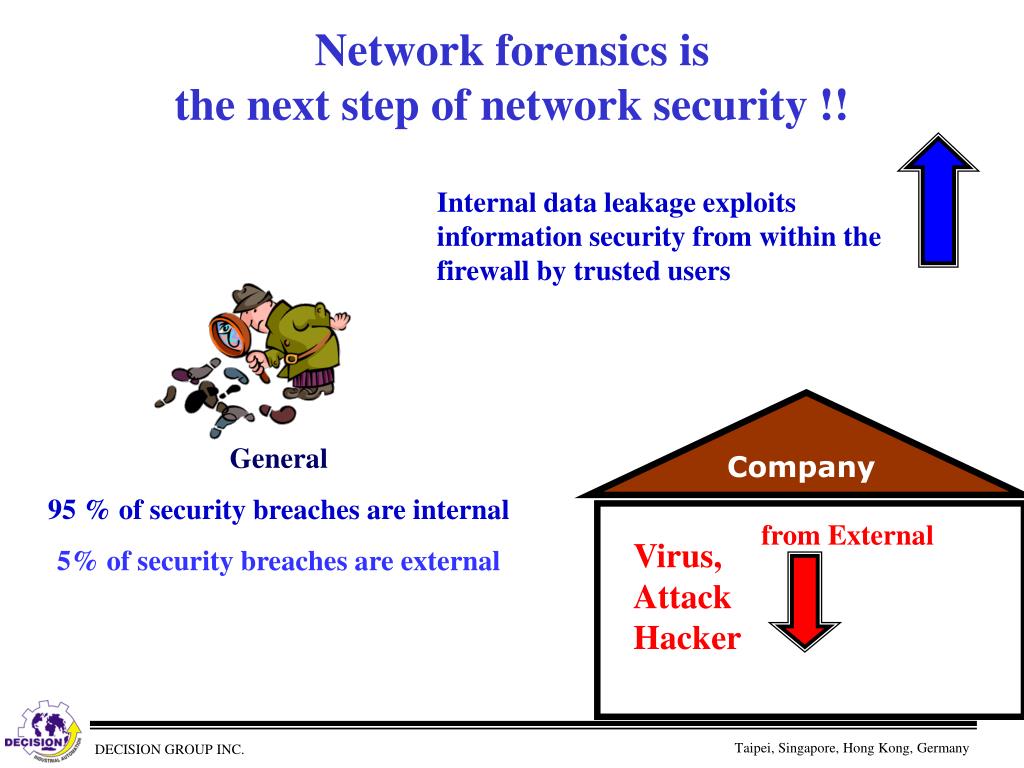
Ppt Network Packet Reconstruction Technology For Computer Forensics Network forensics is a specialized branch of digital forensics concerned with the monitoring, capture, analysis, and interpretation of network traffic to investigate cyber incidents, security breaches, and criminal activities conducted over computer networks. This powerpoint slide deck delivers actionable disk, network, and mobile forensics processes with real pros cons analyses, cross platform forensic tool comparisons, and evidence collection protocols. This document provides an overview of network monitoring and forensics. it discusses different types of forensic data like packet capture (pcap) files, flow data, and log alert data. Virtual machine forensics, live acquisitions, and network forensics.
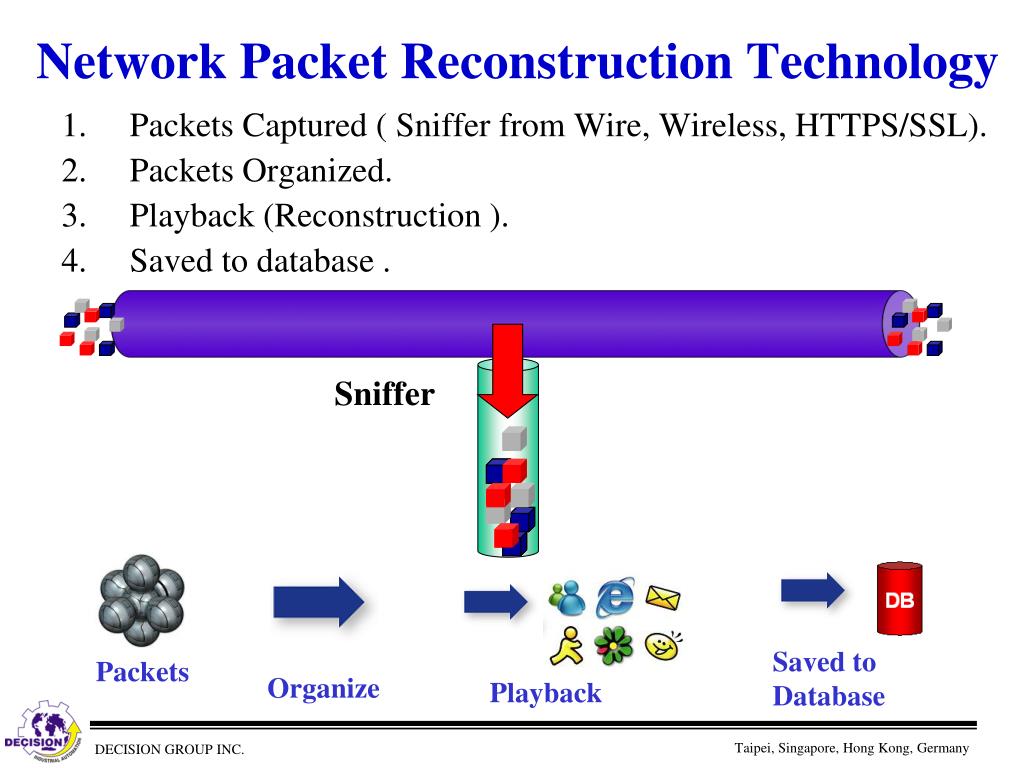
Ppt Network Packet Reconstruction Technology For Computer Forensics This document provides an overview of network monitoring and forensics. it discusses different types of forensic data like packet capture (pcap) files, flow data, and log alert data. Virtual machine forensics, live acquisitions, and network forensics. Full packet capture tools: store complete network data without missing any packets, allowing detailed inspection of all transmitted information. log analysis tools: help analyze records generated by network devices to identify patterns, errors, or suspicious activities quickly. Network forensics = digital evidence is coming from traffic of a computer network. digital evidence can be collected through combinations of software or hardware tools. you will usually be working with pcap files. goals of network forensics. answer important questions such as: when did the incident happen? what is the timeline?. About this presentation transcript and presenter's notes title: computer forensics tools 1 computer forensics tools. Ÿ ¨ *look at all your hosts, especially serversó Ÿ ¨ forensics: backtracking Ÿ   nowadays hackers are increasingly sophisticated about hiding tracks the ones that are good, you won t catch the ones that you can catch aren t worth catching very few good tools for backtracking are available¡ 6dz 3dz3ó j e Ÿ Â.

Ppt Network Packet Reconstruction Technology For Computer Forensics Full packet capture tools: store complete network data without missing any packets, allowing detailed inspection of all transmitted information. log analysis tools: help analyze records generated by network devices to identify patterns, errors, or suspicious activities quickly. Network forensics = digital evidence is coming from traffic of a computer network. digital evidence can be collected through combinations of software or hardware tools. you will usually be working with pcap files. goals of network forensics. answer important questions such as: when did the incident happen? what is the timeline?. About this presentation transcript and presenter's notes title: computer forensics tools 1 computer forensics tools. Ÿ ¨ *look at all your hosts, especially serversó Ÿ ¨ forensics: backtracking Ÿ   nowadays hackers are increasingly sophisticated about hiding tracks the ones that are good, you won t catch the ones that you can catch aren t worth catching very few good tools for backtracking are available¡ 6dz 3dz3ó j e Ÿ Â.
Ppt Network Packet Reconstruction Technology For Computer Forensics About this presentation transcript and presenter's notes title: computer forensics tools 1 computer forensics tools. Ÿ ¨ *look at all your hosts, especially serversó Ÿ ¨ forensics: backtracking Ÿ   nowadays hackers are increasingly sophisticated about hiding tracks the ones that are good, you won t catch the ones that you can catch aren t worth catching very few good tools for backtracking are available¡ 6dz 3dz3ó j e Ÿ Â.
Comments are closed.