Ppt Exercises Basic Cryptography Key Exchange Protocols Powerpoint
Ppt Key Exchange Protocols Powerpoint Presentation Free Download Exercises: basic cryptography & key exchange protocols. exercise 1. alice and bob want to verify that they possess a common key k , using a public one way function h . they use the following protocol: alice sends to bob: h (h (k)) bob verifies that the received value is correct. The document outlines key concepts of computer security and cryptography, emphasizing the importance of secure communication, which includes secrecy, authentication, and message integrity.
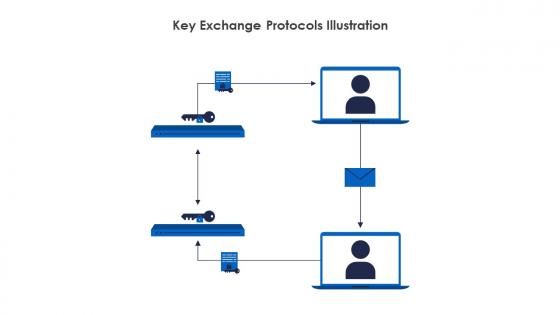
Key Exchange Protocols Powerpoint Presentation And Slides Slideteam This document provides an introduction to cryptography. it discusses symmetric and asymmetric cryptographic methods. symmetric cryptography uses the same secret key for encryption and decryption, while asymmetric cryptography uses separate public and private keys. Two parties (often called a sender and a receiver) share some secret information called a key. Basic cryptography how cryptography works symmetric cryptography public key cryptography online resources. About this presentation transcript and presenter's notes title: key exchange protocols 1 key exchange protocols cs 259 2008.
Ppt Exercises Basic Cryptography Key Exchange Protocols Powerpoint Basic cryptography how cryptography works symmetric cryptography public key cryptography online resources. About this presentation transcript and presenter's notes title: key exchange protocols 1 key exchange protocols cs 259 2008. Ipsec includes: 1) the ip security protocol itself, which defines the information to add to an ip packet, as well as how to encrypt packet data; and 2) the internet key exchange, which uses asymmetric based key exchange and negotiates the security associations. Use the shift cipher with key = 15 to encrypt the message “hello.” solution we encrypt one character at a time. each character is shifted 15 characters “down”. letter h is encrypted to w. letter e is encrypted to t. the first l is encrypted to a. the second l is also encrypted to a. and o is encrypted to d. the cipher text is wtaad. Grab the ingenious ppt collections of key exchange protocols presentation templates and google slides. Asymmetric ciphers use two keys, private and public. asymmetric is much slower. both symmetric and asymmetric can be used if need to be. think: if you want to send a secret symmetric key, you can use asymmetric. protocols ipsec (internet security protocol) operates in the network layer. used in vpn.
Comments are closed.