Ppt Dacc Distributed Access Control In Clouds Powerpoint

Ppt Dacc Distributed Access Control In Clouds Powerpoint Dacc: distributed access control in clouds. 2011 ieee trustcom 11 sushmita ruj amiya nayak and ivan stojmenovic. 2013.04.29 regular seminar tae hoon kim. contents. 1. introduction 2. related work 3. background a. model and assumptions b. formats of access policies. It describes common access control models like discretionary access control (dac), mandatory access control (mac), and role based access control (rbac). it also discusses access control terminology, technical processes, and best practices for implementing access controls.
Ppt Dacc Distributed Access Control In Clouds Powerpoint Ppt decentralized access control with anonymous authentication of data stored in clouds (1) free download as powerpoint presentation (.ppt .pptx), pdf file (.pdf), text file (.txt) or view presentation slides online. aaa. We propose a new model for data storage and access in clouds. our scheme avoids storing multiple encrypted copies of same data. in our framework for secure data. Why mac is needed? 1996, 38 47. Access control (authorisation) in distributed systems recall lecture 9 introduction to ds: slides 21 to 27 for access control within the overall system architecture: as an individual e.g. from home.
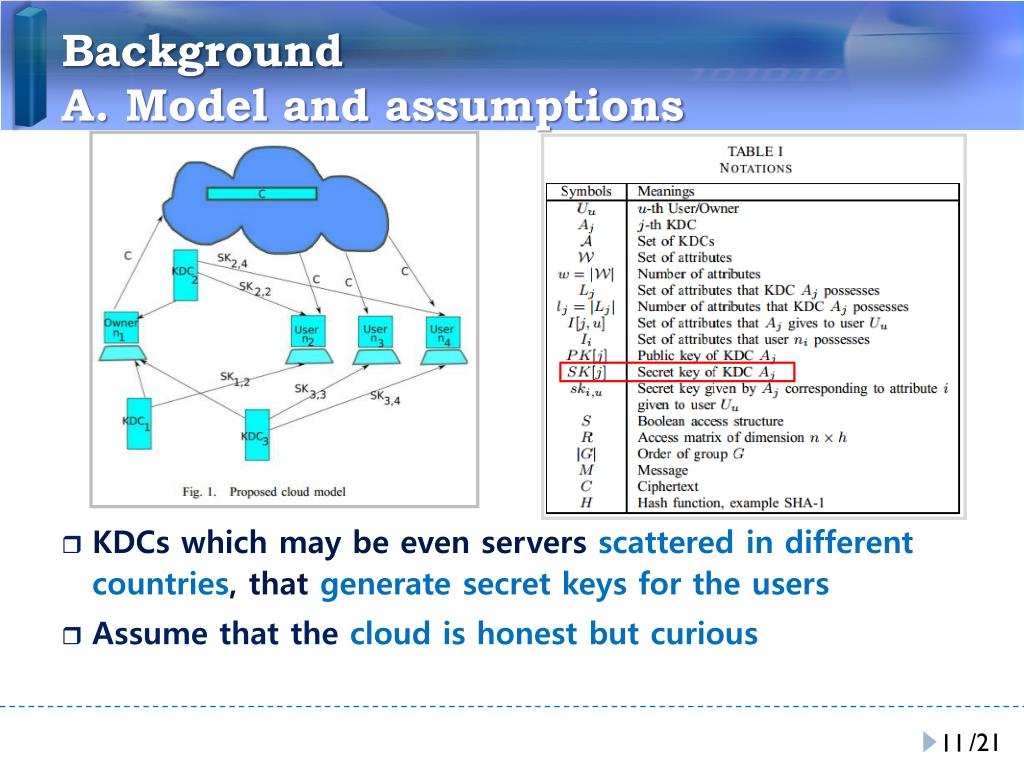
Ppt Dacc Distributed Access Control In Clouds Powerpoint Why mac is needed? 1996, 38 47. Access control (authorisation) in distributed systems recall lecture 9 introduction to ds: slides 21 to 27 for access control within the overall system architecture: as an individual e.g. from home. Slideteam's globalization templates are ready made frameworks of how distribution works. these content ready slides handle the structure while you focus on the specifics. We propose dacc (distributed access control in clouds) algorithm, where one or more kdcs distribute keys to data owners and users. kdc may provide access to particular fields in all records. We propose dacc (distributed access control in clouds) algorithm, where one or more kdcs distribute keys to data owners and users. kdc may provide access to particular fields in all records. #3 this chapter deals with a narrower, more specific concept of access control which implements a security policy that specifies who or what may have access to each specific system resource and the type of access that is permitted in each instance.

Ppt Dacc Distributed Access Control In Clouds Powerpoint Slideteam's globalization templates are ready made frameworks of how distribution works. these content ready slides handle the structure while you focus on the specifics. We propose dacc (distributed access control in clouds) algorithm, where one or more kdcs distribute keys to data owners and users. kdc may provide access to particular fields in all records. We propose dacc (distributed access control in clouds) algorithm, where one or more kdcs distribute keys to data owners and users. kdc may provide access to particular fields in all records. #3 this chapter deals with a narrower, more specific concept of access control which implements a security policy that specifies who or what may have access to each specific system resource and the type of access that is permitted in each instance.

Ppt Dacc Distributed Access Control In Clouds Powerpoint We propose dacc (distributed access control in clouds) algorithm, where one or more kdcs distribute keys to data owners and users. kdc may provide access to particular fields in all records. #3 this chapter deals with a narrower, more specific concept of access control which implements a security policy that specifies who or what may have access to each specific system resource and the type of access that is permitted in each instance.
Comments are closed.