Ppt Authentication Protocols Ii Powerpoint Presentation Free
Ppt Authentication Protocols Powerpoint Presentation Free Download It provides details on how dsa uses public private key pairs to generate and verify digital signatures for authenticating messages and senders. download as a ppt, pdf or view online for free. Download presentation by click this link. while downloading, if for some reason you are not able to download a presentation, the publisher may have deleted the file from their server.
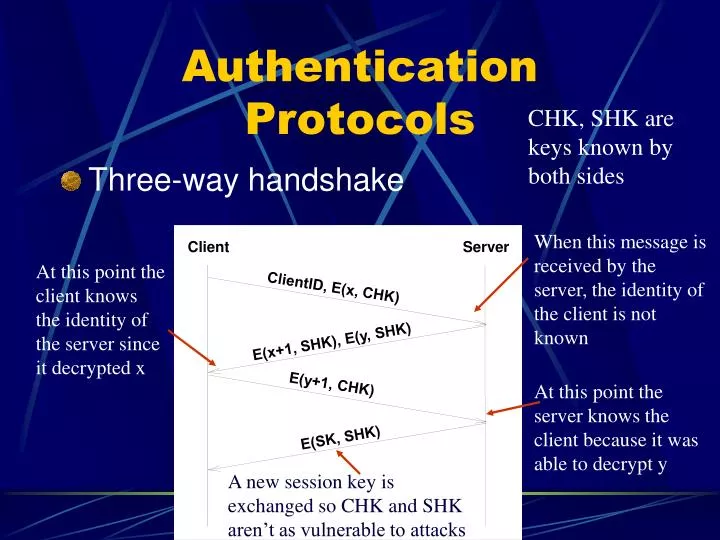
Ppt Authentication Protocols Powerpoint Presentation Free Download We begin this chapter with an overview of digital signatures, authentication protocol and digital signature standard (dss) 2 contents. Ns unit4 dss free download as powerpoint presentation (.ppt), pdf file (.pdf), text file (.txt) or view presentation slides online. the document discusses digital signatures and authentication protocols. Digital signatures and authentication protocols adv. topics in data and net. sec. prof. dr. ayman abdel hamid * there is a critical flaw in the protocol, as shown. this emphasises the need to be extremely careful in codifying assumptions, and tracking the timeliness of the flow of info in protocols. Authentication and authorization mechanisms are crucial components of any secure software system. this powerpoint presentation provides a comprehensive overview of the different mechanisms used to authenticate and authorize users within a system.
Ppt Authentication Powerpoint Presentation Free Download Id 4596494 Digital signatures and authentication protocols adv. topics in data and net. sec. prof. dr. ayman abdel hamid * there is a critical flaw in the protocol, as shown. this emphasises the need to be extremely careful in codifying assumptions, and tracking the timeliness of the flow of info in protocols. Authentication and authorization mechanisms are crucial components of any secure software system. this powerpoint presentation provides a comprehensive overview of the different mechanisms used to authenticate and authorize users within a system. Ace up your presentation with fully customizable authentication protocol presentation templates and google slides. If you know a secret, then you are linked to an “identity” the secret needs to be associated with the identity beforehand (authentication state) authentication protocol is the process of proving that one knows the secret, a.k.a “credential.”. Authentication based cyber threat prevention techniques download pdf slide 1 of 9. • data origin authentication the ipsec receiver can authenticate the source of the ipsec packets sent. this service is dependent upon the data integrity service.
Ppt Lecture 6 2 Protocols Authentication And Key Exchange Ii Ace up your presentation with fully customizable authentication protocol presentation templates and google slides. If you know a secret, then you are linked to an “identity” the secret needs to be associated with the identity beforehand (authentication state) authentication protocol is the process of proving that one knows the secret, a.k.a “credential.”. Authentication based cyber threat prevention techniques download pdf slide 1 of 9. • data origin authentication the ipsec receiver can authenticate the source of the ipsec packets sent. this service is dependent upon the data integrity service.
Two Factor Authentication Ppt Powerpoint Presentation Slides Diagrams Cpb Authentication based cyber threat prevention techniques download pdf slide 1 of 9. • data origin authentication the ipsec receiver can authenticate the source of the ipsec packets sent. this service is dependent upon the data integrity service.
Ppt Secure Authentication Mechanisms In Computer Systems Powerpoint
Comments are closed.