Post Quantum Cryptography Vs Symmetric Cryptography In Technology
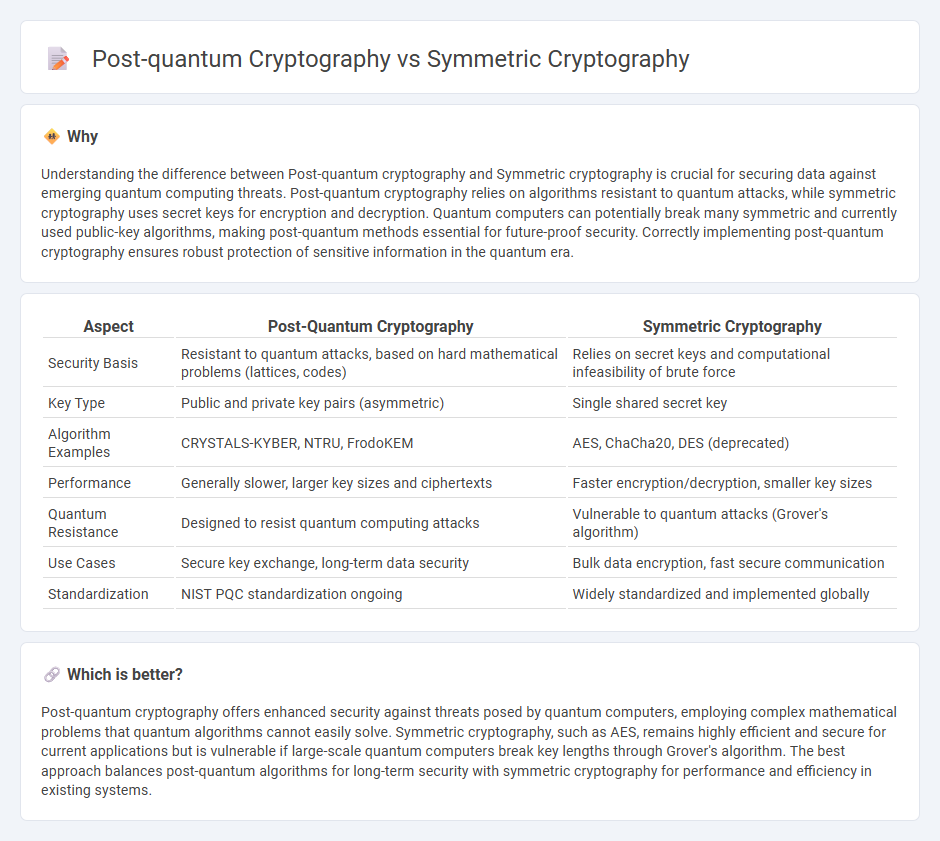
Post Quantum Cryptography Vs Symmetric Cryptography In Technology Post quantum cryptography focuses on developing encryption algorithms resistant to attacks by quantum computers, whereas symmetric cryptography relies on shared secret keys for secure communication. The transition from classical public key cryptography to post quantum cryptography (pqc) is considered a long term, multi phase process due to the widespread deployment of cryptographic infrastructure across digital systems.
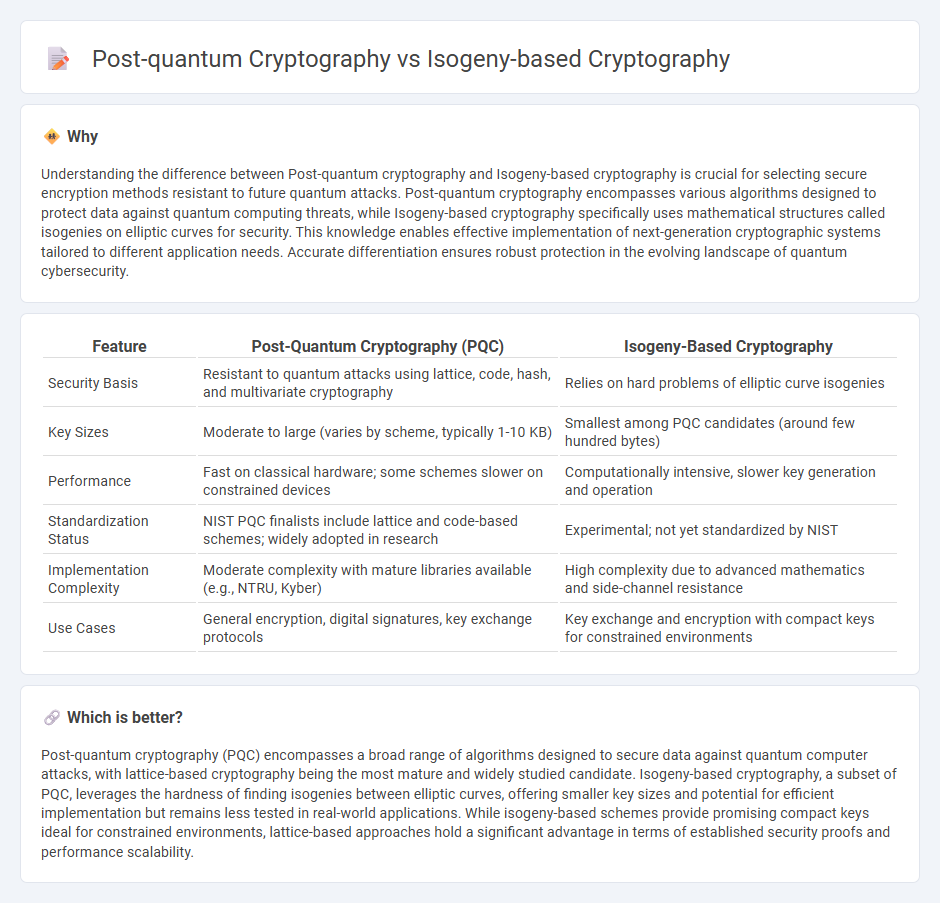
Post Quantum Cryptography Vs Isogeny Based Cryptography In Technology This study offers a detailed comparison between classical and post quantum cryptographic algorithms, examining their relative resilience to quantum attacks, differences in key and signature sizes, and the complexity involved in implementation. Explore the differences between quantum and post quantum cryptography and how synopsys' pqc solutions can secure your data against future quantum threats. Learn more about the differences between classical cryptography, post quantum cryptography, and quantum cryptography. Nist’s post quantum cryptography (pqc) project leads the national and global effort to secure electronic information against the future threat of quantum computers—machines that may be years or decades away but could eventually break many of today’s widely used cryptographic systems.

Quantum Cryptography Vs Post Quantum Cryptography Synopsys Learn more about the differences between classical cryptography, post quantum cryptography, and quantum cryptography. Nist’s post quantum cryptography (pqc) project leads the national and global effort to secure electronic information against the future threat of quantum computers—machines that may be years or decades away but could eventually break many of today’s widely used cryptographic systems. The technical challenges and limitations of current quantum resistant algorithms are examined, along with insights from recent research and discussions on emerging trends in post quantum. We introduce an independent research project on symmetric cryptography with a focus on foreseeable industrial needs and higher post quantum security compared to currently used symmetric algorithms. For me, this adds up to saying that before we dive headfirst into the world of new, asymmetric key algorithms, maybe we should see just how far we can take the parts of cryptography that we aren’t worried about. symmetric key algorithms are not particularly subject to any good quantum attacks. This paper will explore technical and operational challenges in implementing quantum and post quantum cryptography technologies and propose a roadmap to guide this transition.

Quantum Cryptography Vs Post Quantum Cryptography Major Difference The technical challenges and limitations of current quantum resistant algorithms are examined, along with insights from recent research and discussions on emerging trends in post quantum. We introduce an independent research project on symmetric cryptography with a focus on foreseeable industrial needs and higher post quantum security compared to currently used symmetric algorithms. For me, this adds up to saying that before we dive headfirst into the world of new, asymmetric key algorithms, maybe we should see just how far we can take the parts of cryptography that we aren’t worried about. symmetric key algorithms are not particularly subject to any good quantum attacks. This paper will explore technical and operational challenges in implementing quantum and post quantum cryptography technologies and propose a roadmap to guide this transition.
Comments are closed.