Post Quantum Cryptography Vs Classical Cryptography In Technology
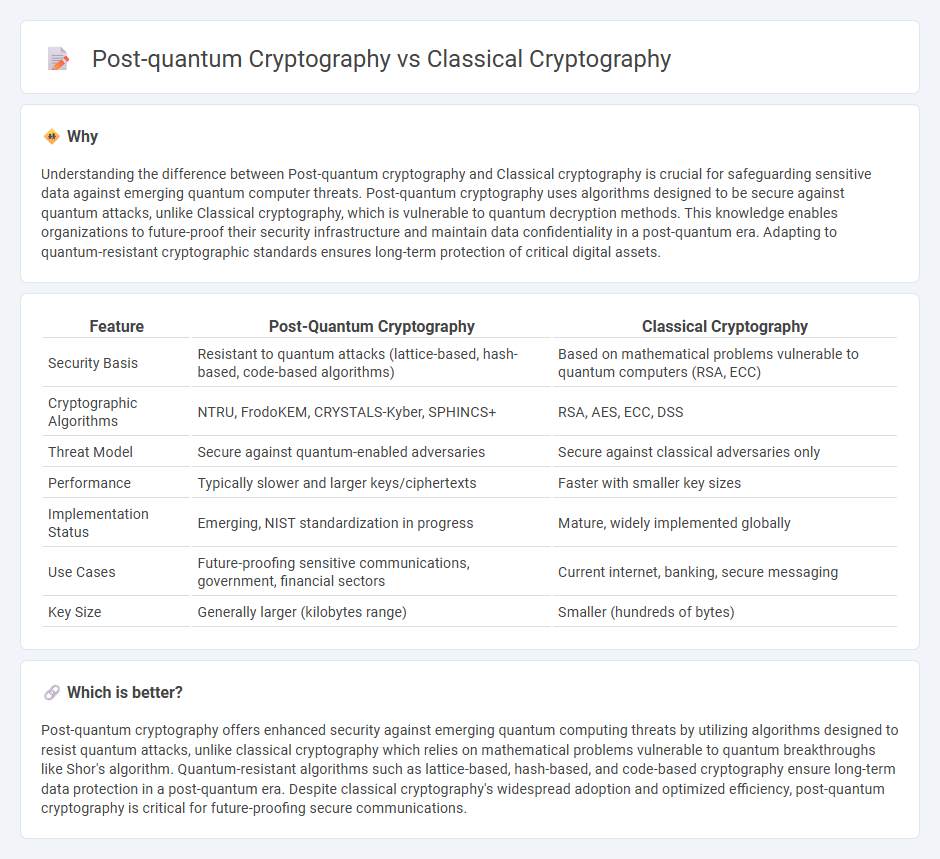
Post Quantum Cryptography Vs Classical Cryptography In Technology To provide a unified overview of the cryptographic landscape under the lens of quantum computing, we present a comparative analysis between widely deployed classical algorithms and emerging post quantum candidates. Classical cryptography uses difficult mathematical problems to protect data from non quantum threats. post quantum cryptography also relies on mathematical problems, but they’re much more difficult than in classical cryptography and can withstand quantum attacks.
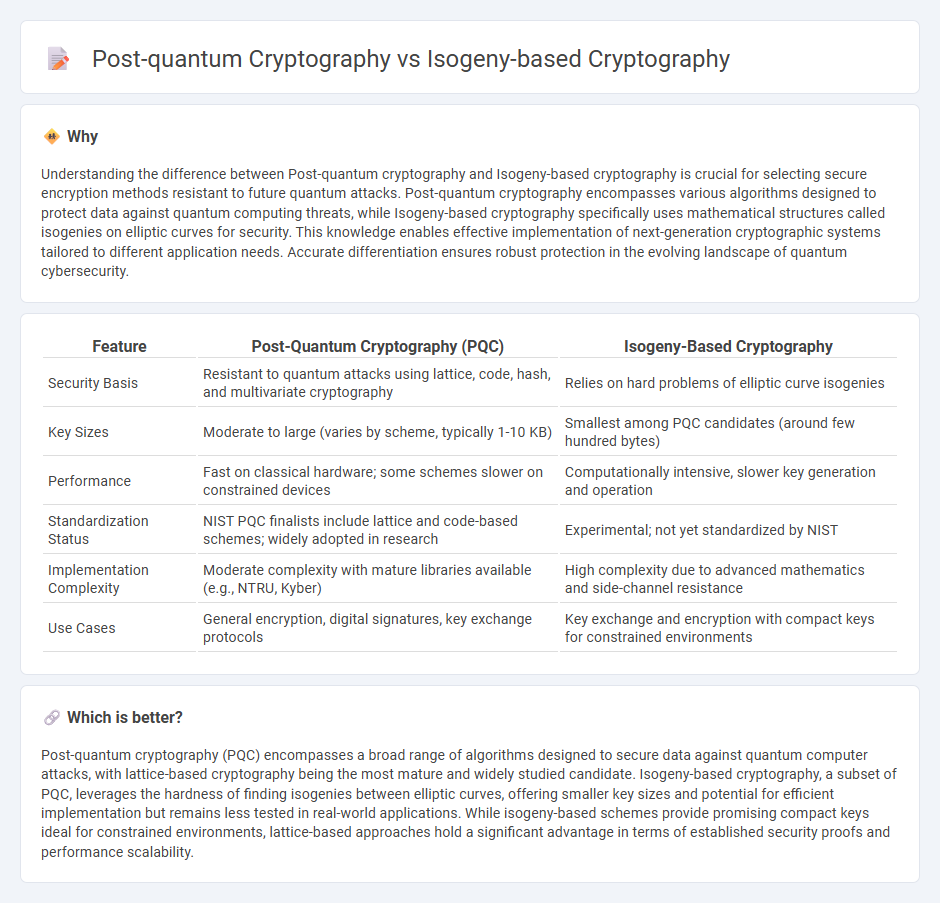
Post Quantum Cryptography Vs Isogeny Based Cryptography In Technology Classical cryptography and quantum cryptography this article describes classical cryptography, focusing on its mathematical basis and use of keys for encryption, as well as its limitations and differences from quantum cryptography. The research demonstrates that pqc mitigates the weaknesses of conventional cryptographic systems while providing a scalable and pragmatic solution for secure communication in the quantum age. By understanding the mathematics of both classical and post quantum algorithms, and by aggressively testing new protocols in the field, society can navigate the quantum transition. This study examines a range of post quantum cryptography (pqc) schemes designed to withstand quantum attacks, including lattice based, isogeny based, hash based, code based, and multivariate approaches.

Quantum Cryptography Vs Post Quantum Cryptography Synopsys By understanding the mathematics of both classical and post quantum algorithms, and by aggressively testing new protocols in the field, society can navigate the quantum transition. This study examines a range of post quantum cryptography (pqc) schemes designed to withstand quantum attacks, including lattice based, isogeny based, hash based, code based, and multivariate approaches. Post quantum cryptography aims to develop cryptographic algorithms that are secure against both classical and quantum computers, in response to potential weaknesses in classical cryptographic algorithms from advances in computing power and quantum computers. We analyze the quantum vulnerability of classical cryptography, including rsa and elliptic curve systems, and explore leading pqc alternatives including lattice based cryptography (crystals kyber and dilithium), multivariate cryptography (rainbow and gemss), and isogeny based approaches. Explore key differences between quantum computing and classical cryptography, their impact on cybersecurity, and future proof post quantum solutions. This article explores the evolution of cryptographic techniques, from classical encryption methods to modern public key cryptography and emerging post quantum cryptographic solutions.

Quantum Cryptography Vs Classical Cryptography Ppt Graphics At Post quantum cryptography aims to develop cryptographic algorithms that are secure against both classical and quantum computers, in response to potential weaknesses in classical cryptographic algorithms from advances in computing power and quantum computers. We analyze the quantum vulnerability of classical cryptography, including rsa and elliptic curve systems, and explore leading pqc alternatives including lattice based cryptography (crystals kyber and dilithium), multivariate cryptography (rainbow and gemss), and isogeny based approaches. Explore key differences between quantum computing and classical cryptography, their impact on cybersecurity, and future proof post quantum solutions. This article explores the evolution of cryptographic techniques, from classical encryption methods to modern public key cryptography and emerging post quantum cryptographic solutions.
Comments are closed.