Post Quantum Cryptography Technical Overview Pdf Computing

High Speed Design Of Post Quantum Cryptography With Optimized Hashing It spans foundational concepts in classical and post quantum cryptography, the current state of quantum computing, the core principles of post quantum cryptography (pqc), and the status of global standardization efforts. Post quantum cryptography is the study of new cryptosystems which cannot be cracked by both quan tum and classical computers. the cryptosystems are divided into several families based on the underlying problem upon which the security is established.

Post Quantum Cryptography Pdf Dirzon This white paper explains the urgency of the quantum threat, explores the emerging field of post quantum cryptography (pqc), and provides guidance on how organizations can prepare. This timeline (fig. 1) presents a historical overview of cryptographic standards development, alongside projections for quantum computing capabilities. several key phases and initiatives are highlighted. The guide includes: a clear explanation of the quantum threat and its impact on today’s cryptography. timelines and milestones from standards bodies, regulators, and governments. a practical playbook for building a pqc migration strategy, from inventory to pilots to enterprise wide execution. The paper provides an in depth overview of cryptography in the quantum era, including a detailed examination of various post quantum cryptographic approaches such as lattice based,.
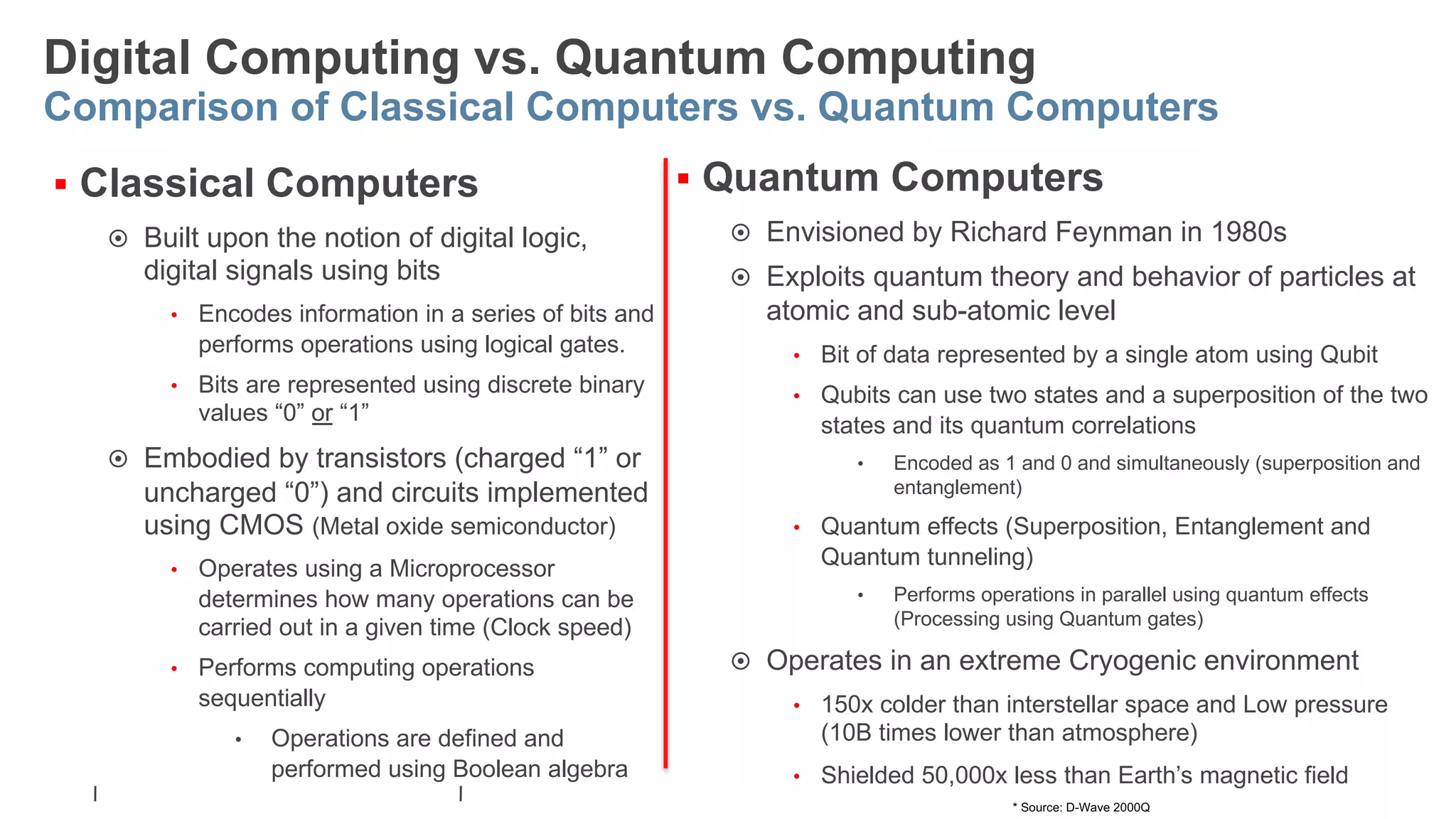
Post Quantum Cryptography Technical Overview Pdf The guide includes: a clear explanation of the quantum threat and its impact on today’s cryptography. timelines and milestones from standards bodies, regulators, and governments. a practical playbook for building a pqc migration strategy, from inventory to pilots to enterprise wide execution. The paper provides an in depth overview of cryptography in the quantum era, including a detailed examination of various post quantum cryptographic approaches such as lattice based,. This report evaluates the impending challenges posed by quantum computers to existing cryptographic mechanisms and explores the advent of post quan tum cryptography as a solution. Post quantum cryptography for engineers: technical overview the future cryptography conference 13.05.2024, tallinn petr muzikant information security research institute @ cybernetica as, estonia [this presentation includes clickable links]. Vpn protocols should ideally combine classical and post quantum cryptography for resilience, while remaining crypto agile to accommodate future cryptographic updates. The document provides a comprehensive overview of post quantum cryptography, comparing classical and quantum computing, and highlighting the vulnerabilities traditional encryption faces against quantum algorithms like shor's and grover's.
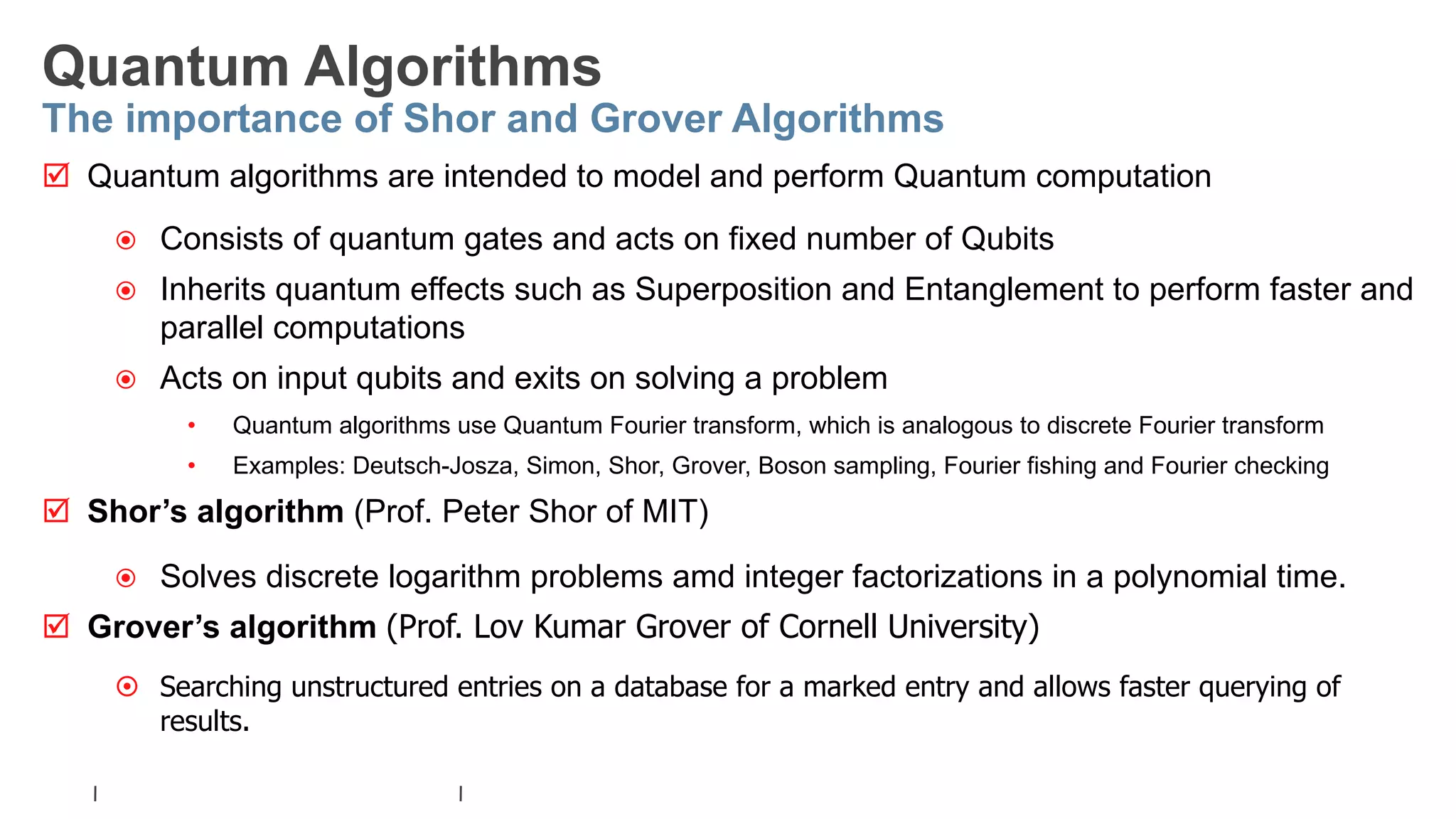
Post Quantum Cryptography Technical Overview Pdf This report evaluates the impending challenges posed by quantum computers to existing cryptographic mechanisms and explores the advent of post quan tum cryptography as a solution. Post quantum cryptography for engineers: technical overview the future cryptography conference 13.05.2024, tallinn petr muzikant information security research institute @ cybernetica as, estonia [this presentation includes clickable links]. Vpn protocols should ideally combine classical and post quantum cryptography for resilience, while remaining crypto agile to accommodate future cryptographic updates. The document provides a comprehensive overview of post quantum cryptography, comparing classical and quantum computing, and highlighting the vulnerabilities traditional encryption faces against quantum algorithms like shor's and grover's.
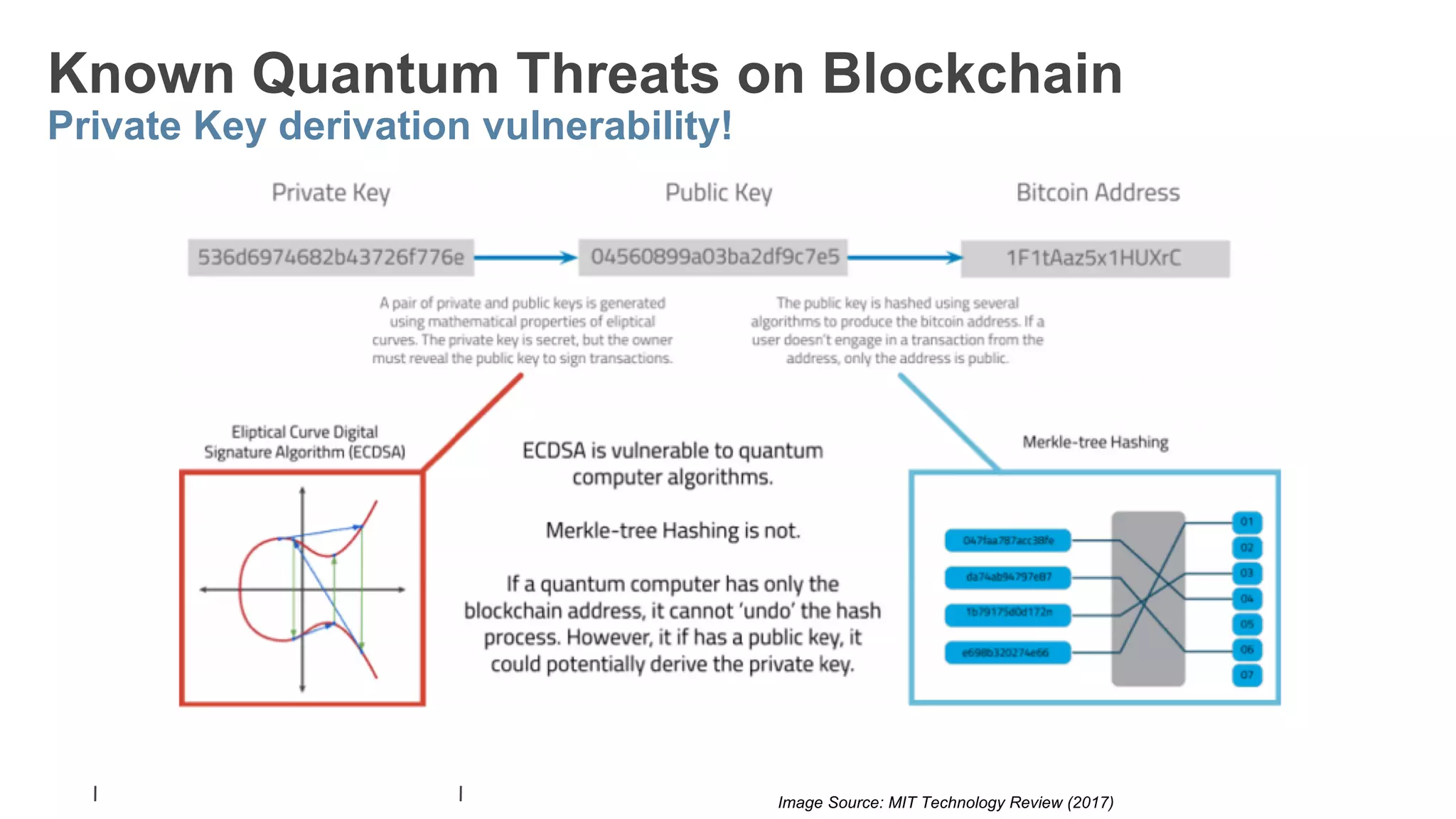
Post Quantum Cryptography Technical Overview Pdf Vpn protocols should ideally combine classical and post quantum cryptography for resilience, while remaining crypto agile to accommodate future cryptographic updates. The document provides a comprehensive overview of post quantum cryptography, comparing classical and quantum computing, and highlighting the vulnerabilities traditional encryption faces against quantum algorithms like shor's and grover's.
Comments are closed.