Post Quantum Cryptography And Secure Boot

Post Quantum Cryptography And Secure Boot Pqshield Abstract secure boot is a standard feature for ensuring the authentication and integrity of software. for this purpose, secure boot leverages the advantage of public key cryptography (pkc). however, the fast developing quantum computers have posed serious threats to the existing pkc. As quantum computing technology advances, the need for robust post quantum cryptographic solutions becomes ever more critical. the integration of pqc into secure boot processes is a pivotal step in safeguarding digital infrastructures against future threats.
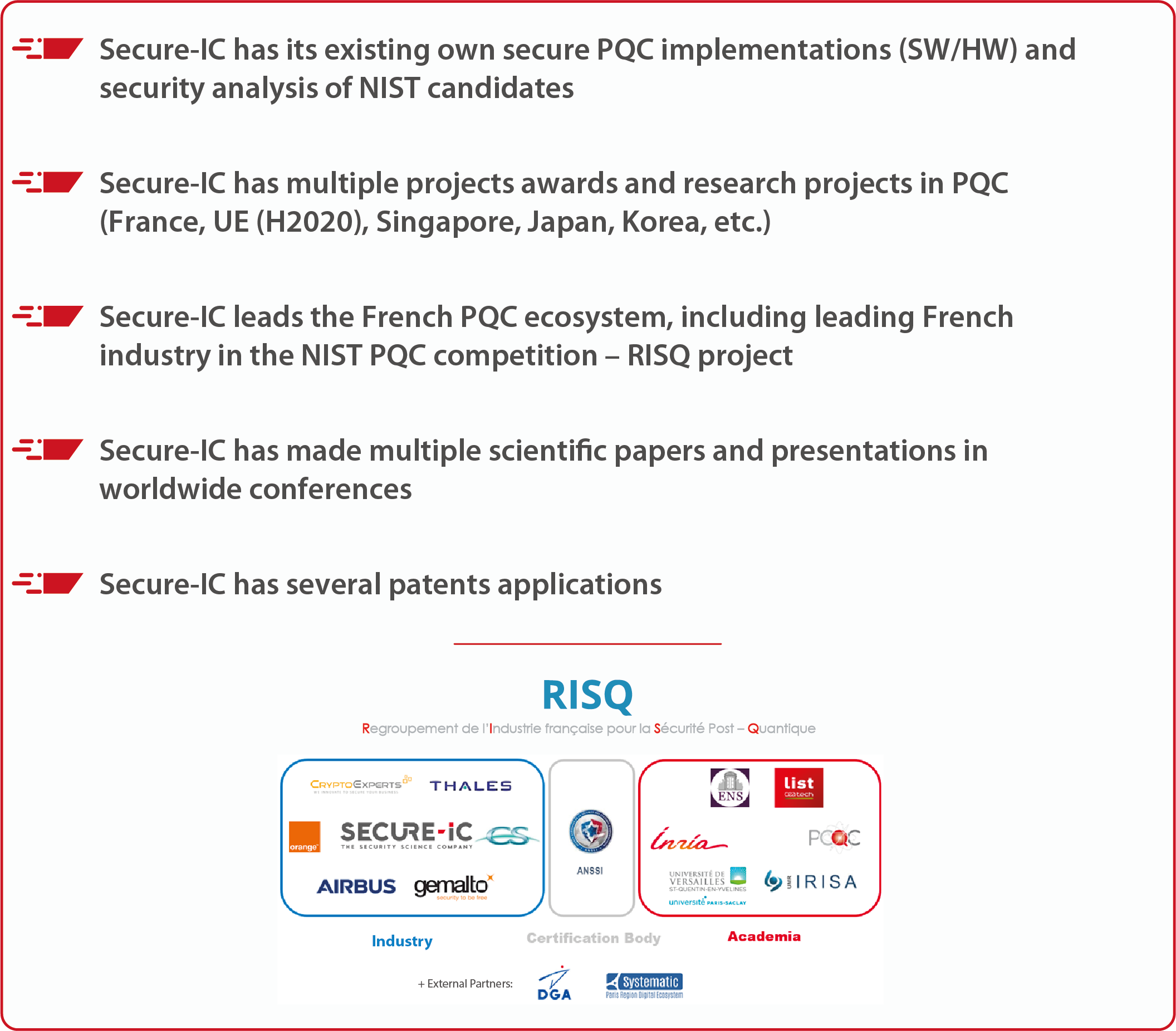
Post Quantum Cryptography Solutions Secure Ic Learn how secure boot, crypto agility, and pqc standards support a post quantum secure approach to next generation device security. A secure boot protocol is fundamental to ensuring the integrity of the trusted computing base of a secure system. the use of digital signature algorithms (dsas). Secure boot is a standard feature for ensuring the authentication and integrity of software. for this purpose, secure boot leverages the advantage of public key cryptography (pkc). however, the fast developing quantum computers have posed serious threats to the existing pkc. Secure boot: full pqc or pq t hybrid? ncsc: transition to full pqc pq t hybrid should be carefully evaluated nsa: transition to full pqc pq t hybrid not recommended.
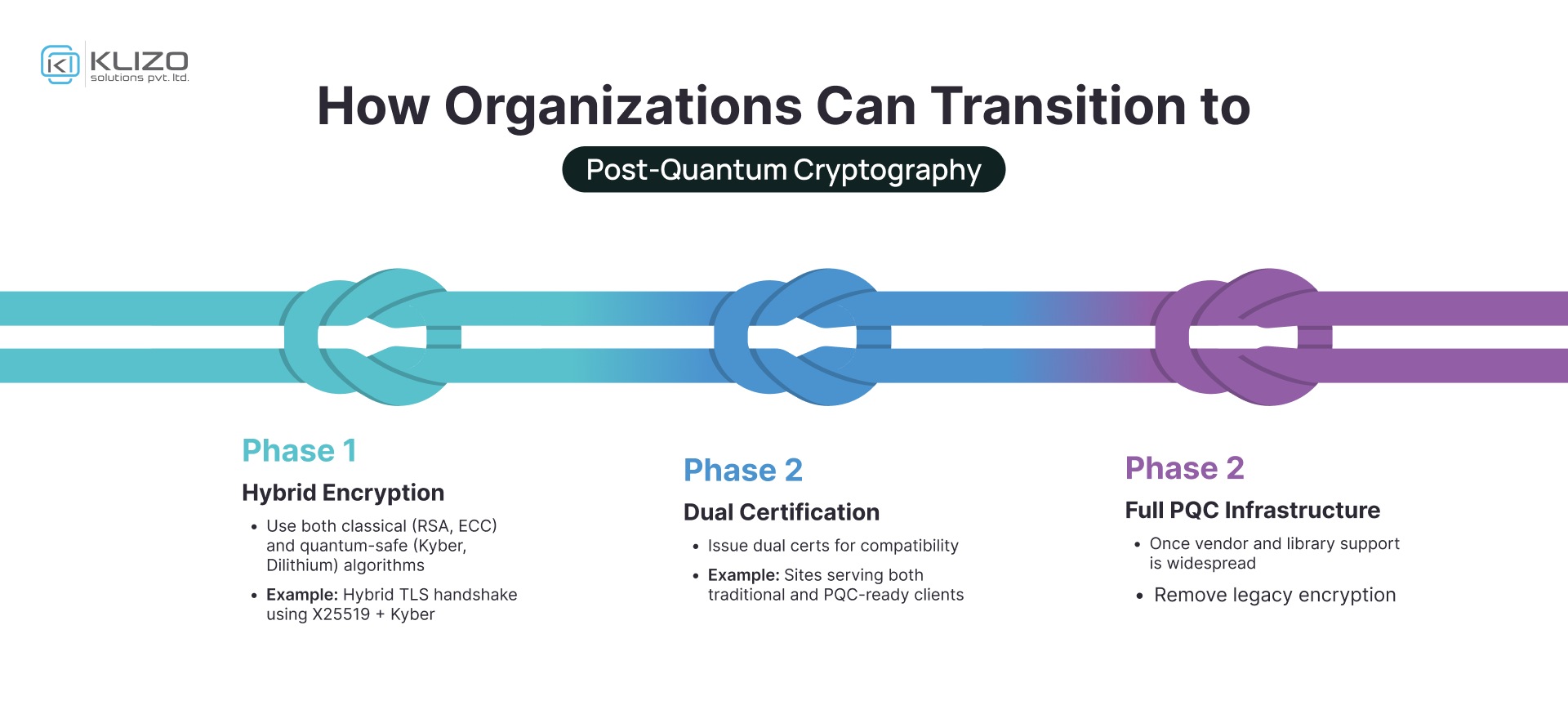
Post Quantum Cryptography The Future Of Secure Computing Klizos Secure boot is a standard feature for ensuring the authentication and integrity of software. for this purpose, secure boot leverages the advantage of public key cryptography (pkc). however, the fast developing quantum computers have posed serious threats to the existing pkc. Secure boot: full pqc or pq t hybrid? ncsc: transition to full pqc pq t hybrid should be carefully evaluated nsa: transition to full pqc pq t hybrid not recommended. Companies like stmicroelectronics, microchip, nxp, and infineon are integrating pqc into firmware, controllers, and hardware roots of trust, focusing on secure boot, firmware verification, and crypto agility for embedded designs. To enable secure boot (a contemporary view) use established cryptographic algorithms. adopt new quantum threat mitigation schemes. deploy hybrid cryptographic protection! use verified, validated implementations of ip cores. go for hardware based solution. This paper presents the design and implementation of a secure bootloader leveraging post quantum cryptographic (pqc) algorithms to ensure the integrity and authenticity of firmware during. Full stack post quantum cryptography (pqc) is the architectural framework introduced with cisco ios xe 26. it is designed to safeguard devices at every layer—securing boot processes, image integrity, network traffic, and management sessions.

Post Quantum Cryptography The Future Of Secure Communication In The Companies like stmicroelectronics, microchip, nxp, and infineon are integrating pqc into firmware, controllers, and hardware roots of trust, focusing on secure boot, firmware verification, and crypto agility for embedded designs. To enable secure boot (a contemporary view) use established cryptographic algorithms. adopt new quantum threat mitigation schemes. deploy hybrid cryptographic protection! use verified, validated implementations of ip cores. go for hardware based solution. This paper presents the design and implementation of a secure bootloader leveraging post quantum cryptographic (pqc) algorithms to ensure the integrity and authenticity of firmware during. Full stack post quantum cryptography (pqc) is the architectural framework introduced with cisco ios xe 26. it is designed to safeguard devices at every layer—securing boot processes, image integrity, network traffic, and management sessions.
Comments are closed.