Portswigger Lab Ssti Basic Server Side Template Injection Code Context

Portswigger Mystery Lab Write Up Server Side Template Injection Ssti This lab is vulnerable to server side template injection due to the unsafe construction of an erb template. to solve the lab, review the erb documentation to find out how to execute arbitrary code, then delete the morale.txt file from carlos's home directory. Completed all 7 server side template injection (ssti) labs from portswigger. ssti is one of the most impactful web vulnerabilities—when template engines process user input without sanitization, attackers can inject template expressions that execute arbitrary code on the server.

Ssti Basic Server Side Template Injection Code Context Scott This lab is vulnerable to server side template injection due to the way it unsafely uses a tornado template. to solve the lab, review the tornado documentation to discover how to execute arbitrary code, then delete the morale.txt file from carlos's home directory. This write up for the lab basic server side template injection (code context) is part of my walk through series for portswigger's web security academy. learning path: advanced topics → server side template injection. as usual, the first step is to analyze the functionality of the lab application. Ssti is a powerful and dangerous vulnerability that allows attackers to execute arbitrary code on a server by injecting malicious templates. in this guide, we’ll demonstrate how to identify. In this lab, we explored a blog application vulnerable to server side template injection (ssti). by manipulating the author’s display name, we successfully injected a payload that led to code execution.

Ssti Basic Server Side Template Injection Scott Murray Ssti is a powerful and dangerous vulnerability that allows attackers to execute arbitrary code on a server by injecting malicious templates. in this guide, we’ll demonstrate how to identify. In this lab, we explored a blog application vulnerable to server side template injection (ssti). by manipulating the author’s display name, we successfully injected a payload that led to code execution. Join me as i solve the portswigger cross site scripting lab "basic server side template injection (code context)" perfect for enhancing your web security skills. more. This lab is vulnerable to server side template injection due to the way it unsafely uses a tornado template. to solve the lab, review the tornado documentation to discover how to execute arbitrary code, then delete the morale.txt file from carlos's home directory. In this post we will walk step by step through how to solve basic server side template injection (code context) on portswigger. this lab’s difficulty is practitioner and it is the second lab in the server side template injection labs on portswigger. We are starting this combined black box with white box testing guide that examines server side template injection (ssti) vulnerabilities across two application frameworks.
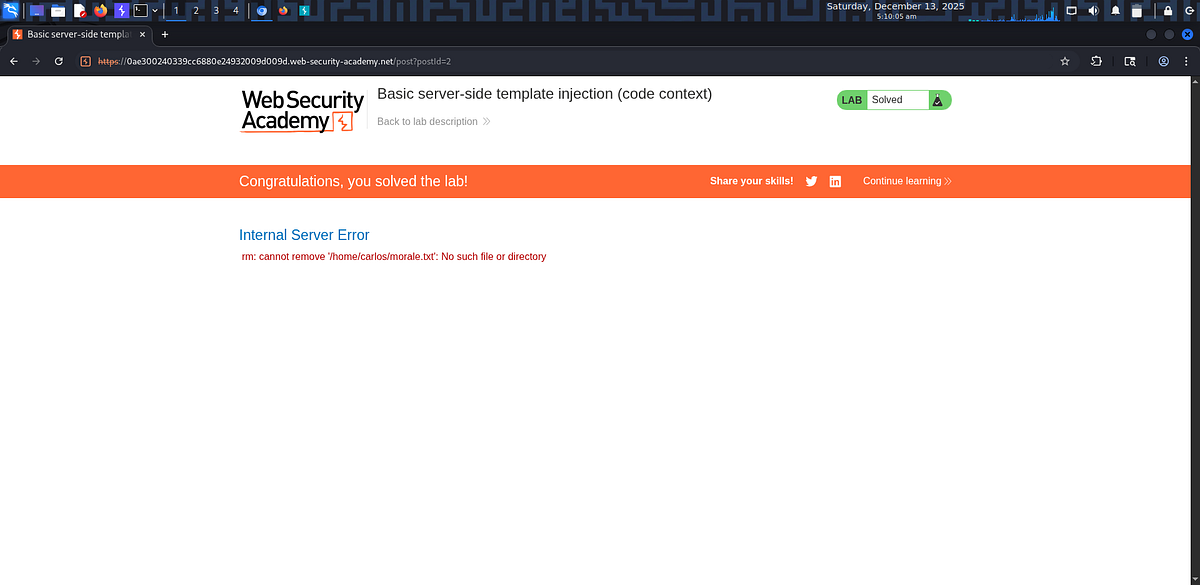
Lab Basic Server Side Template Injection Code Context Portswigger Join me as i solve the portswigger cross site scripting lab "basic server side template injection (code context)" perfect for enhancing your web security skills. more. This lab is vulnerable to server side template injection due to the way it unsafely uses a tornado template. to solve the lab, review the tornado documentation to discover how to execute arbitrary code, then delete the morale.txt file from carlos's home directory. In this post we will walk step by step through how to solve basic server side template injection (code context) on portswigger. this lab’s difficulty is practitioner and it is the second lab in the server side template injection labs on portswigger. We are starting this combined black box with white box testing guide that examines server side template injection (ssti) vulnerabilities across two application frameworks.
Comments are closed.