Portswigger Exploiting An Api Endpoint Using Documentation

Christian V Exploiting An Api Endpoint Using Documentation Required knowledge to solve this lab, you'll need to know: what api documentation is. how api documentation may be useful to an attacker. how to discover api documentation. these points are covered in our api testing academy topic. A pi testing — lab: exploiting an api endpoint using documentation in this portswigger web security academy lab, the goal is simple:.
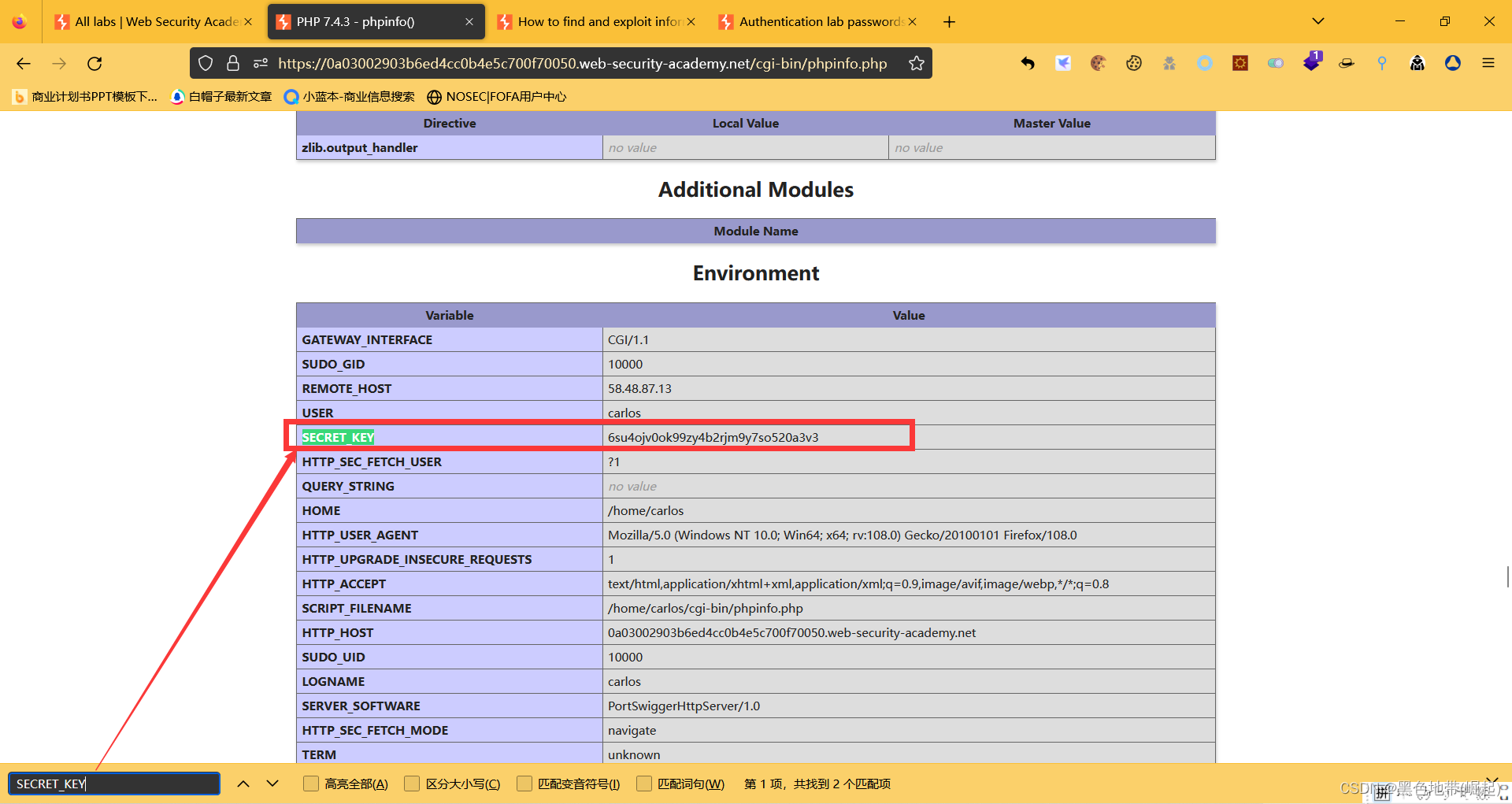
Bp靶场portswigger 服务端6 信息泄露漏洞 5个实验 全 上 阿里云开发者社区 🧠 theory apis often ship with documentation intended for developers — swagger openapi specs, postman collections, or raw json yaml files. when this documentation is left publicly accessible, an attacker can use it to understand the full api surface: all endpoints, http methods, parameters, and authentication requirements. Since the web application uses api (application programming interfaces) to interact with the backend, we can now do some api testing! to start api testing, we first need to find out as much information about the api as possible, to discover its attack surface. Learn how to exploit an api endpoint using documentation effectively. whether you're a beginner or an experienced hacker, this tutorial will provide valuable insights and hands on. To use burp suite community, open chrome and paste the lab's url. put in the credential wiener:peter. change the email address to test@gmail or anything you wish. in proxy > http history, right click the patch api user wiener request and select send to repeater.
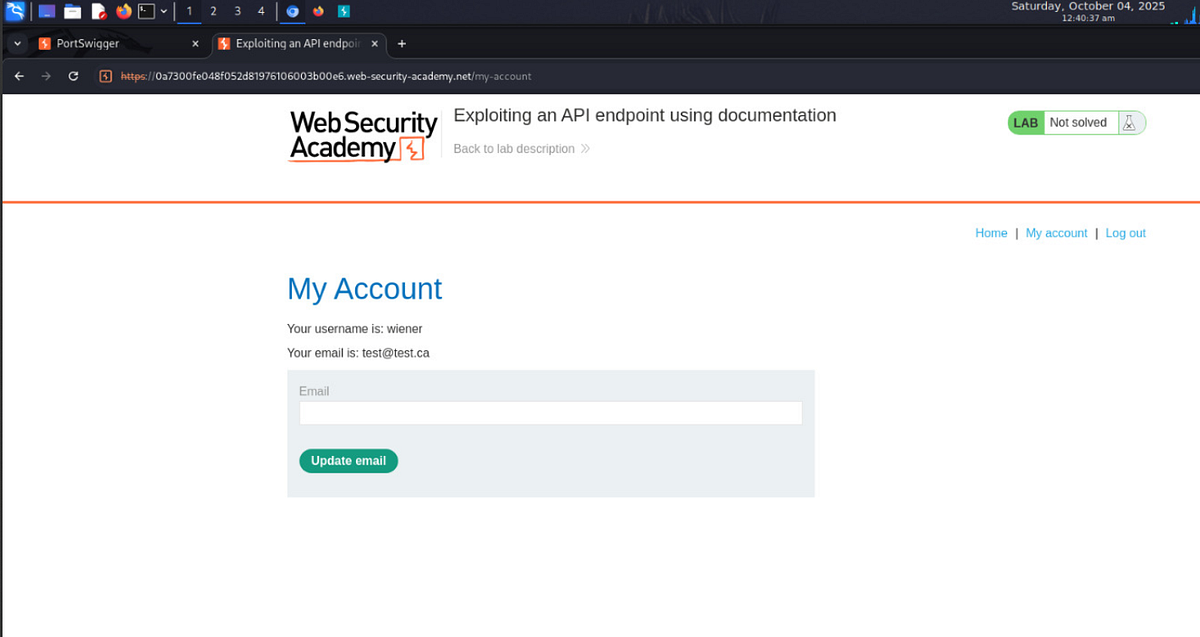
Exploiting An Api Endpoint Using Documentation Lab1 Portswigger Learn how to exploit an api endpoint using documentation effectively. whether you're a beginner or an experienced hacker, this tutorial will provide valuable insights and hands on. To use burp suite community, open chrome and paste the lab's url. put in the credential wiener:peter. change the email address to test@gmail or anything you wish. in proxy > http history, right click the patch api user wiener request and select send to repeater. Exploiting an api endpoint using documentation ¶ portswigger web security learning paths api testing api testing identifying and interacting with api endpoints api testing lab exploiting unused api endpoint. We’re asked to delete the user “carlos” using the api exposed by this web application. we find the documentation for the api via api and see that we can delete a user by sending a delete request to api user username. Api testing is important as vulnerabilities in apis may undermine core aspects of a website’s confidentiality, integrity, and availability. let dive into this lab dummy walkthrough :). This article shows readers through practical labs which explore how attacks occur while demonstrating documentation based api endpoint exploitation together with mass assignment vulnerability discovery methods.
Comments are closed.