Portswigger Api Testing Lab 1 Exploiting An Api Endpoint Using Documentation
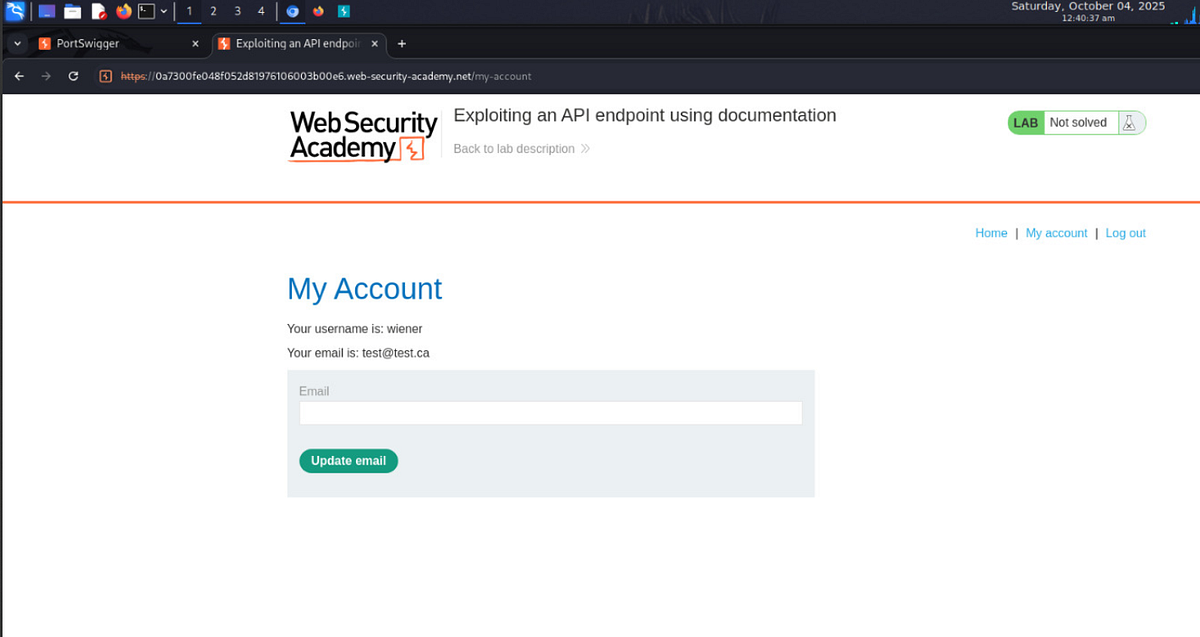
Exploiting An Api Endpoint Using Documentation Lab1 Portswigger Required knowledge to solve this lab, you'll need to know: what api documentation is. how api documentation may be useful to an attacker. how to discover api documentation. these points are covered in our api testing academy topic. This is a brief write up of how i solved the first lab in the api testing learning path on the portswigger web academy, together with some notes i took along the way from their.

Lab Exploiting An Api Endpoint Using Documentation Infosec Writeups These labs covered api documentation exploitation, server side parameter pollution in query strings and rest urls, finding unused api endpoints, and exploiting mass assignment vulnerabilities. Hello hackers, in this video of exploiting an api endpoint using documentation you will see how to exploit, discover and find hidden endpoints and senstive information from burp suite. To begin, you should identify api endpoints. these are locations where an api receives requests about a specific resource on its server. once you have identified the endpoints, you need to determine how to interact with them. this enables you to construct valid http requests to test the api. To start api testing, we first need to find out as much information about the api as possible, to discover its attack surface. to begin, we should identify api endpoints.
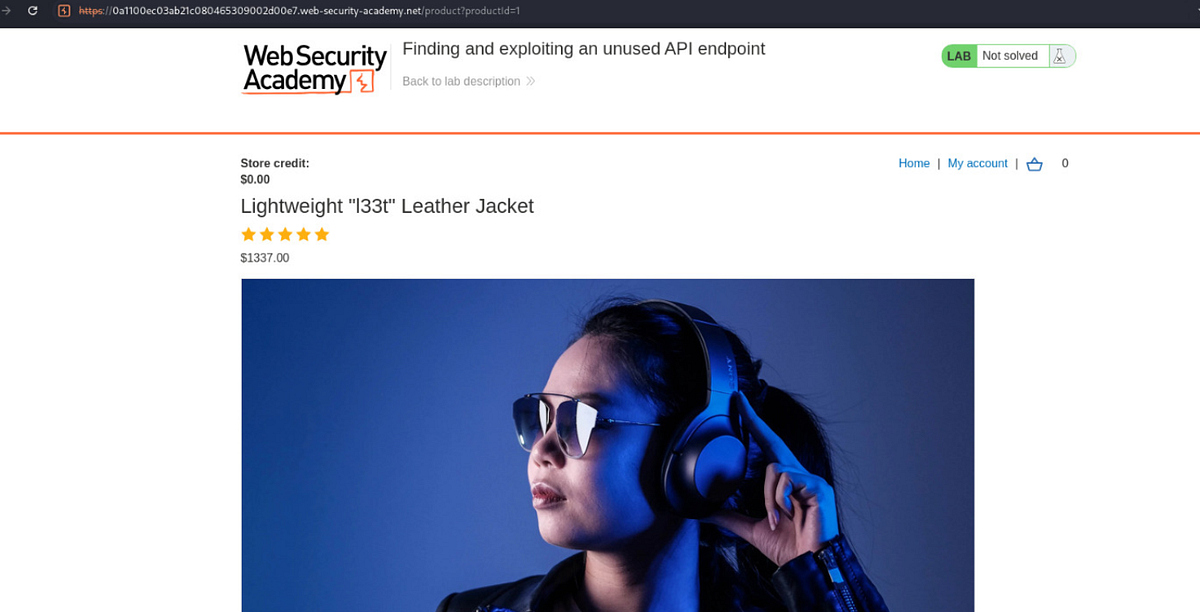
Lab 2 Finding And Exploiting An Unused Api Endpoint Portswigger By To begin, you should identify api endpoints. these are locations where an api receives requests about a specific resource on its server. once you have identified the endpoints, you need to determine how to interact with them. this enables you to construct valid http requests to test the api. To start api testing, we first need to find out as much information about the api as possible, to discover its attack surface. to begin, we should identify api endpoints. A pi testing — lab: exploiting an api endpoint using documentation in this portswigger web security academy lab, the goal is simple:. Learn how to exploit an api endpoint using documentation effectively. whether you're a beginner or an experienced hacker, this tutorial will provide valuable insights and hands on. To start api testing, you first need to find out as much information about the api as possible, to discover its attack surface. to begin, you should identify api endpoints. This article shows readers through practical labs which explore how attacks occur while demonstrating documentation based api endpoint exploitation together with mass assignment vulnerability discovery methods.
Exploiting An Api Endpoint Using Documentation Cyberiumx A pi testing — lab: exploiting an api endpoint using documentation in this portswigger web security academy lab, the goal is simple:. Learn how to exploit an api endpoint using documentation effectively. whether you're a beginner or an experienced hacker, this tutorial will provide valuable insights and hands on. To start api testing, you first need to find out as much information about the api as possible, to discover its attack surface. to begin, you should identify api endpoints. This article shows readers through practical labs which explore how attacks occur while demonstrating documentation based api endpoint exploitation together with mass assignment vulnerability discovery methods.
Comments are closed.