Playbook 1 Third Session Pdf

Playbook 1 Third Session Pdf Playbook 1 third session free download as pdf file (.pdf), text file (.txt) or read online for free. My purpose in writing this book is to create a straightforward and practical approach to penetration testing. there are many security books that discuss every type of tool and every type of vulnerability, where only small portions of the attacks seem to be relevant to the average penetration tester.

Playbook Basic Format Pdf Loading…. This is the third iteration of the hacker playbook (thp) series. below is an overview of all the new vulnerabilities and attacks that will be discussed. in addition to the new content, some attacks and techniques from the prior books (which are still relevant today) are included to eliminate the need to refer back to the prior books. so, what. It covers a wide array of topics, including network scanning, web application testing, social engineering, and post exploitation tactics, structured in a format reminiscent of a football playbook. Please download files in this item to interact with them on your computer.
Free Pdf Midnight Playbook Protocol Etsy Canada It covers a wide array of topics, including network scanning, web application testing, social engineering, and post exploitation tactics, structured in a format reminiscent of a football playbook. Please download files in this item to interact with them on your computer. Loading…. Its purpose is two fold: (1) you may create long running bots that simulate virtual red team members, hacking side by side with you, (2) you may also use it to extend and modify the cobalt strike client to your needs [ cobaltstrike aggressor script index ]. Playbook 1 free download as pdf file (.pdf), text file (.txt) or read online for free. This playbook describes the process fceb agencies should follow for confirmed malicious cyber activity for which a major incident has been declared or not yet been reasonably ruled out.
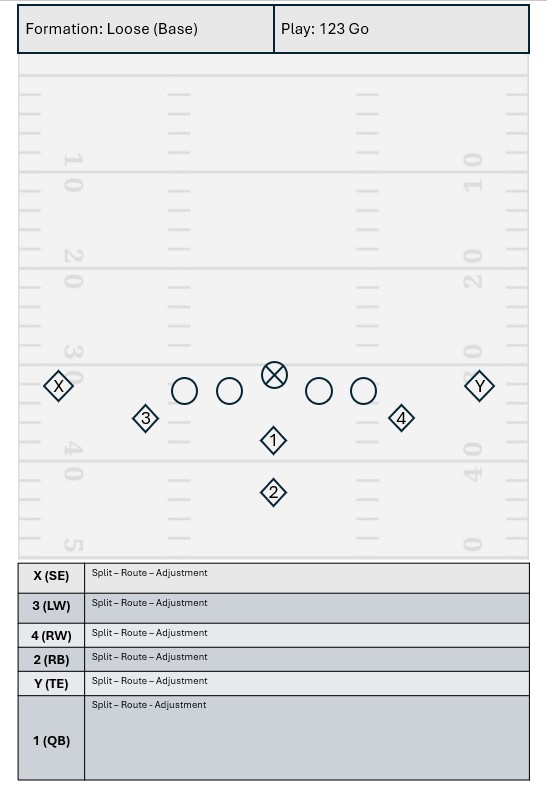
Playbook Template Sample Screenshot By Coach G Coachtube Loading…. Its purpose is two fold: (1) you may create long running bots that simulate virtual red team members, hacking side by side with you, (2) you may also use it to extend and modify the cobalt strike client to your needs [ cobaltstrike aggressor script index ]. Playbook 1 free download as pdf file (.pdf), text file (.txt) or read online for free. This playbook describes the process fceb agencies should follow for confirmed malicious cyber activity for which a major incident has been declared or not yet been reasonably ruled out.

Playbook 2018 Pdf Version 1 Pdf Playbook 1 free download as pdf file (.pdf), text file (.txt) or read online for free. This playbook describes the process fceb agencies should follow for confirmed malicious cyber activity for which a major incident has been declared or not yet been reasonably ruled out.
Playbook
Comments are closed.