Php Function Hack Olicyber Web App Hacking Make A Wish
A Bunch Of Compromized Wordpress Sites Sans Isc Follow along with the video! once logged into the training.olicyber.it site, navigate to the following url: training.olicyber.it challenges#challenge. The regex .* i is effectively unbeatable against any string. the issue is not the regex itself, but the assumption that $ get ['richiesta'] is always a string. in php this is not guaranteed: a user can send arrays via the [] syntax in parameters.

Free Video Web App Hacking File Inclusion Attacks From Cyber Mentor Cybersecurity related educational videos with an emphasis on beginner skills and self directed training. There are many different sql functions and operations we can use to manipulate the syntax, and this example is just one of very many. below is a pseudo code example which contains a sql injection vulnerability. Whether you’re a programmer with an interest in bug bounties or a seasoned security professional, hacker101 has something to teach you. Hackthissite.org is a free, safe and legal training ground for hackers to test and expand their ethical hacking skills with challenges, ctfs, and more.

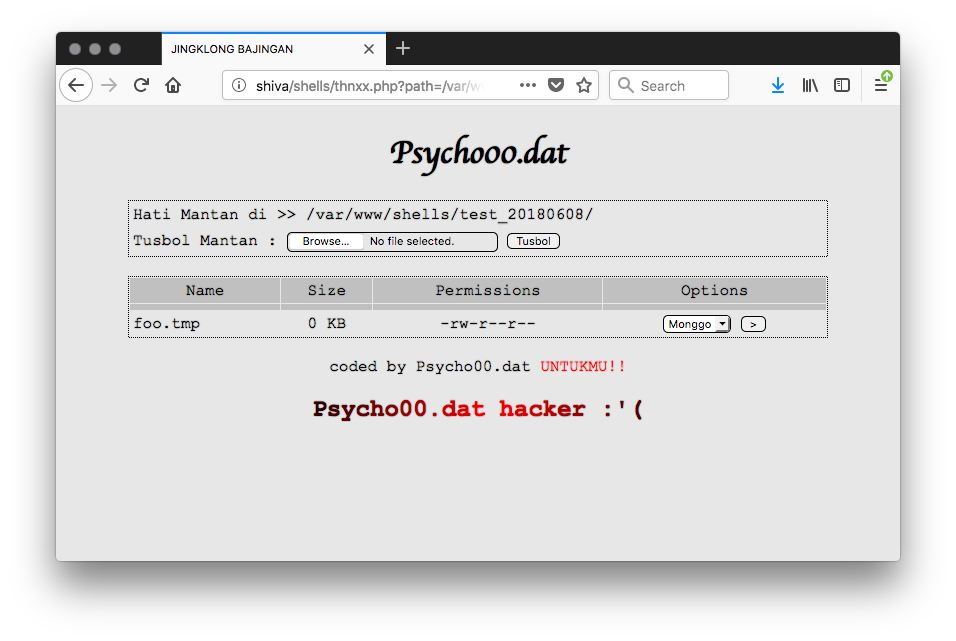
Free Video Web App Hacking File Upload Attacks From Cyber Mentor Whether you’re a programmer with an interest in bug bounties or a seasoned security professional, hacker101 has something to teach you. Hackthissite.org is a free, safe and legal training ground for hackers to test and expand their ethical hacking skills with challenges, ctfs, and more. Whether you’re a developer curious about security, a student exploring ethical hacking, or an experienced professional sharpening your bug bounty skills, hacker101 offers content for all levels. The exploit database exploits, shellcode, 0days, remote exploits, local exploits, web apps, vulnerability reports, security articles, tutorials and more. It’s an extremely simple web app that would allow people to anonymously share their wishes with others. unfortunately, right after the hacker attack, the security team has discovered that. Php has powerful functions that allow running code or shell commands. if user input is passed directly to these functions without validation, attackers can inject malicious commands and gain server access.
Comments are closed.