Php Extract Function Flaw Allows Hackers To Execute Arbitrary Code

Cursor S Autorun Lets Hackers Execute Arbitrary Code Cso Online A newly disclosed vulnerability in php’s widely used extract () function has put all major php versions—5.x, 7.x, and 8.x—at risk of severe security breaches, including arbitrary native. A critical vulnerability in php’s extract () function enables attackers to trigger memory corruption that can lead to arbitrary native code execution across multiple php versions.
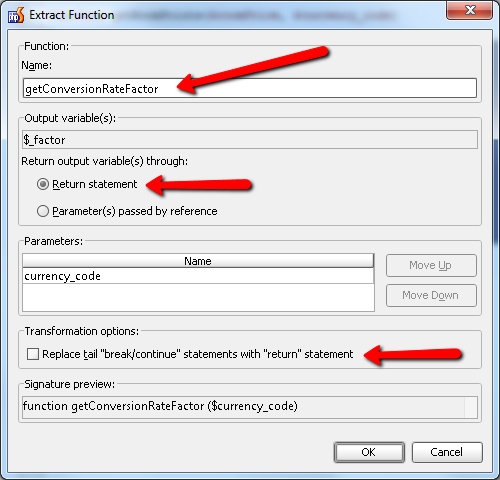
Extract Function Method Refactoring For Php The Webide Blog A vulnerability in php’s extract() function allows attackers to trigger a double free in version 5.x or a user after free in versions 7.x, 8.x, which in turn allows arbitrary code execution (native code). A newly disclosed vulnerability in php’s widely used extract () function has put all major php versions—5.x, 7.x, and 8.x—at risk of severe security breaches, including arbitrary native code execution. The vulnerability, involving the extract() function, can be exploited to compromise the interpreter’s memory, enabling attackers to execute native code. this article dives into the technical details of the flaw, its potential for exploitation, and the steps developers can take to mitigate the threat. This function imports variables from an array into the current symbol table, which can be manipulated to create a dangerous memory condition.
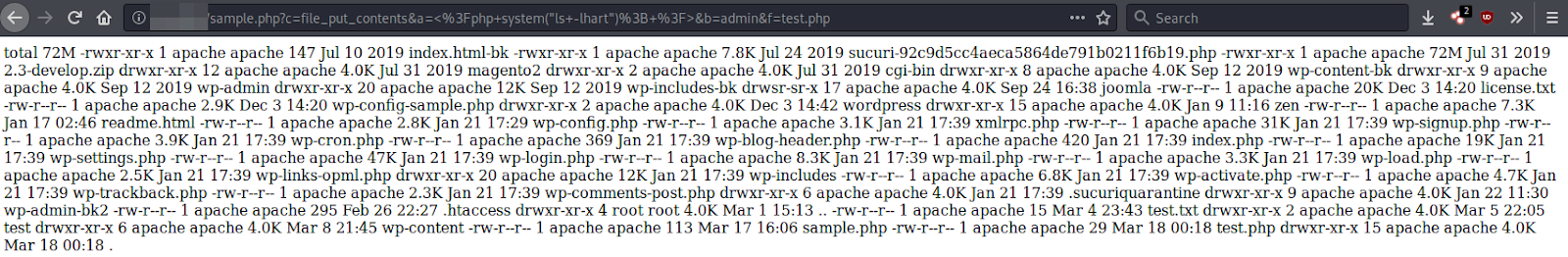
Extract Function Backdoor Variant The vulnerability, involving the extract() function, can be exploited to compromise the interpreter’s memory, enabling attackers to execute native code. this article dives into the technical details of the flaw, its potential for exploitation, and the steps developers can take to mitigate the threat. This function imports variables from an array into the current symbol table, which can be manipulated to create a dangerous memory condition. A newly disclosed vulnerability in php’s popular extract () function poses a serious threat to web servers, potentially allowing remote attackers to execute arbitrary code by. A critical vulnerability in php’s extract () function has been uncovered, enabling attackers to execute arbitrary code by exploiting memory corruption flaws. A critical vulnerability in php’s extract () function enables attackers to trigger memory corruption that can lead to arbitrary native code execution across multiple php versions. A critical vulnerability in php’s extract () function has been uncovered, enabling attackers to execute arbitrary code by exploiting memory corruption flaws.

Php Backdoors Hidden With Clever Use Of Extract Function A newly disclosed vulnerability in php’s popular extract () function poses a serious threat to web servers, potentially allowing remote attackers to execute arbitrary code by. A critical vulnerability in php’s extract () function has been uncovered, enabling attackers to execute arbitrary code by exploiting memory corruption flaws. A critical vulnerability in php’s extract () function enables attackers to trigger memory corruption that can lead to arbitrary native code execution across multiple php versions. A critical vulnerability in php’s extract () function has been uncovered, enabling attackers to execute arbitrary code by exploiting memory corruption flaws.
Comments are closed.