Phishing Website Examples
50 Phishing Email Examples Hook Security An exhaustive library of phishing websites, phishing links, phishing pages, and guidance outlining what phishing websites are. Before we look at some fresh examples of fake websites in the wild, let’s look at the types of fake websites and what you can do to protect your clients from them.
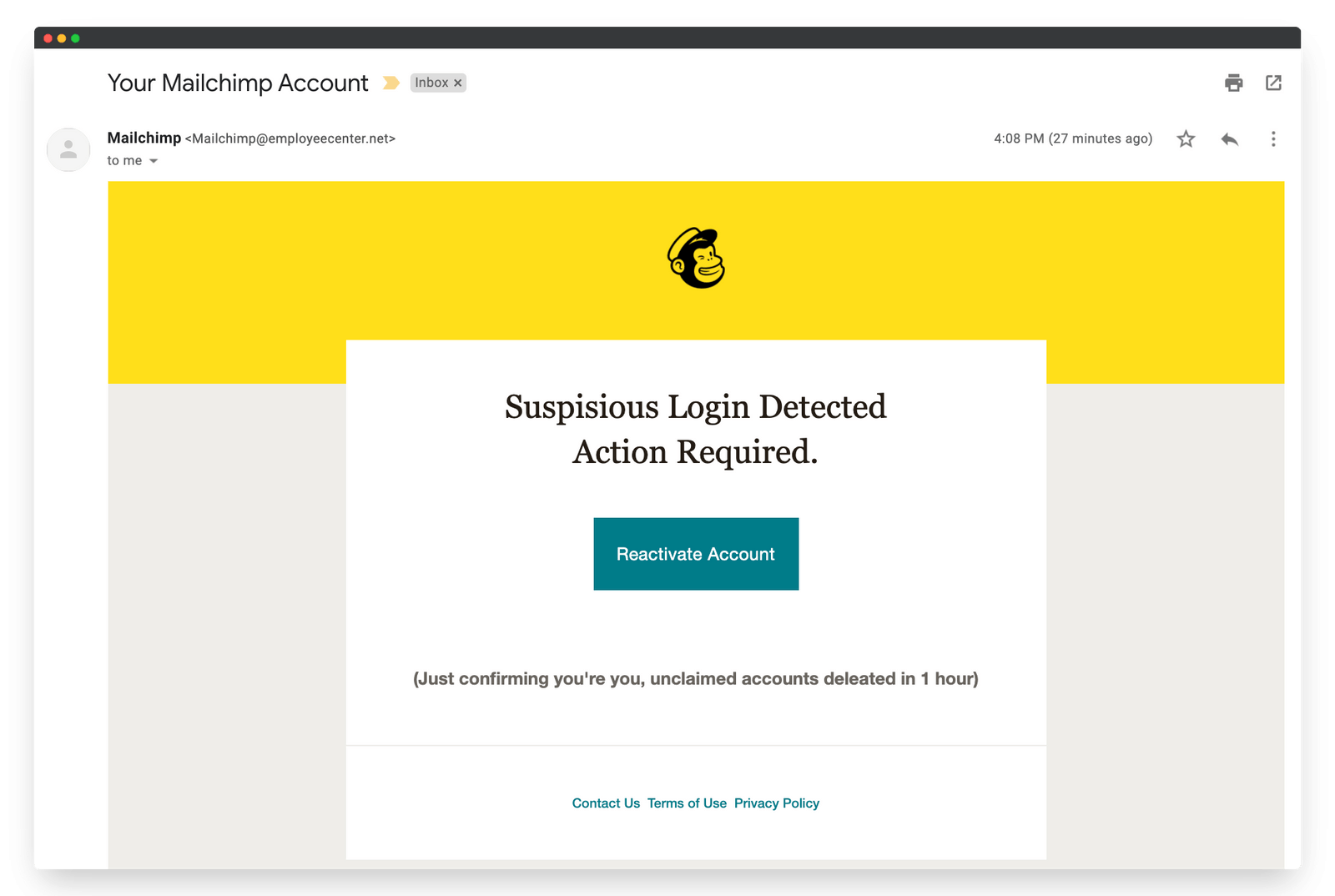
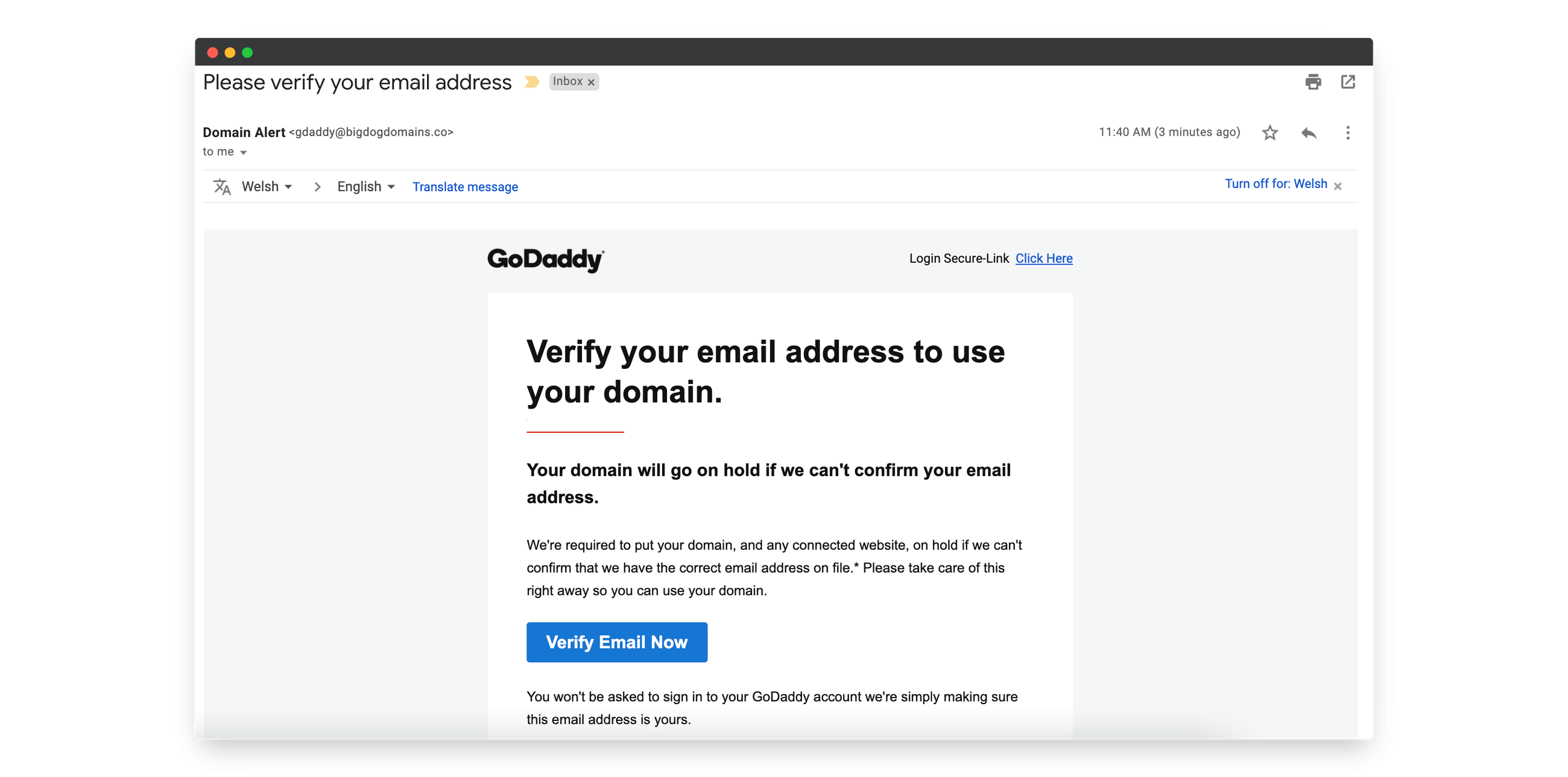
50 Phishing Email Examples Hook Security See real phishing examples and domain spoofing techniques. learn the tactics attackers use and how to spot fake emails before they steal your credentials. A phishing attack is a type of cybercrime where malicious actors send fraudulent communications, often disguised as legitimate messages, to trick individuals into revealing sensitive information or taking actions that compromise their security. they involve emails, text messages, or fake websites. What are the worst phishing examples of all time? in this article, we'll uncover the 11 worst phishing attacks ever, revealing the extent of this cyber menace. Discover the most common phishing attacks with real examples, shocking stats, and practical tips to protect yourself and your business from cyber scams.
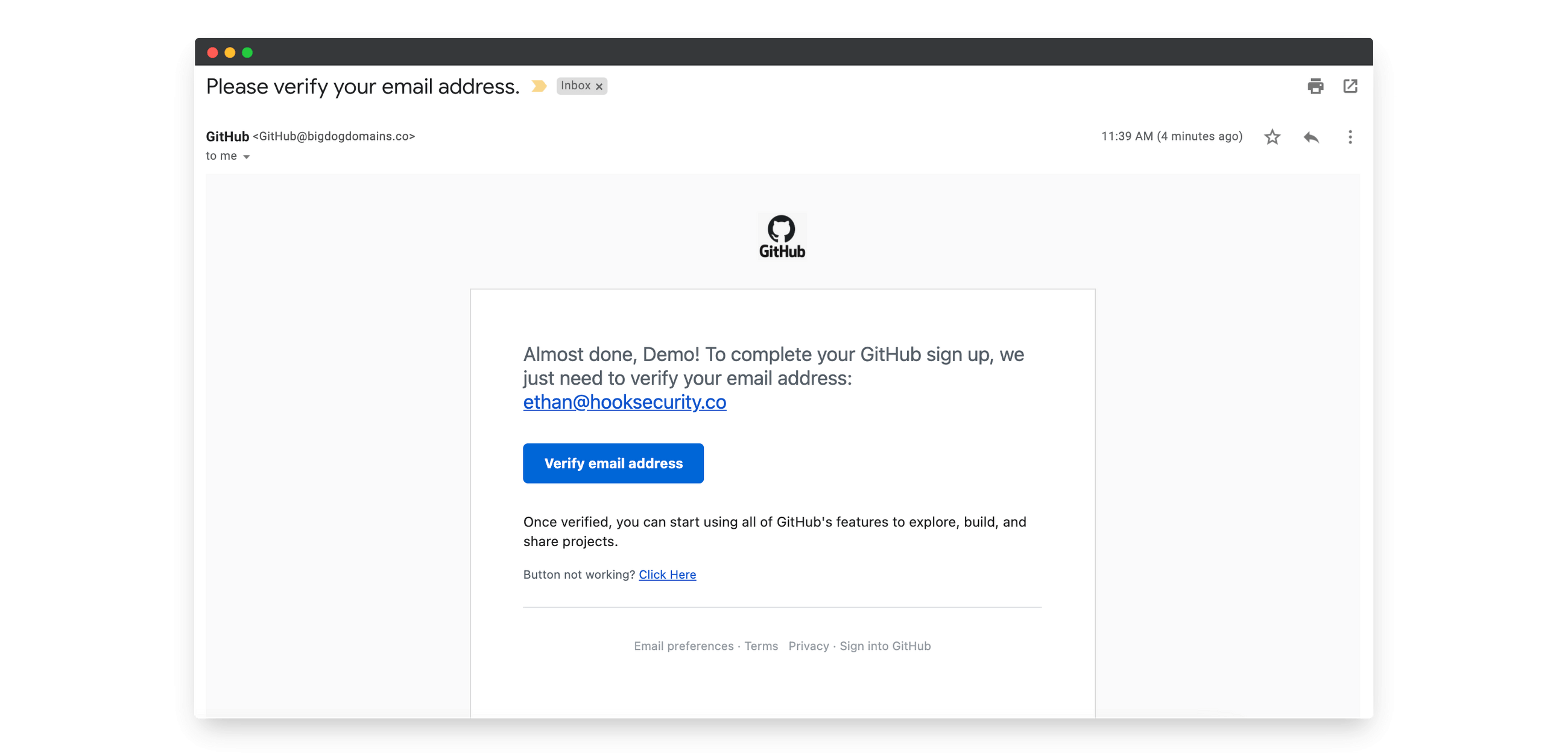
50 Phishing Email Examples Hook Security What are the worst phishing examples of all time? in this article, we'll uncover the 11 worst phishing attacks ever, revealing the extent of this cyber menace. Discover the most common phishing attacks with real examples, shocking stats, and practical tips to protect yourself and your business from cyber scams. A phishing message purporting to be from the international rescue committee regarding it maintenance has been circulating on campus. the message requests that the recipient upgrade their mailbox size by selecting a link that redirects to a malicious website. Url phishing tends to occur alongside brandjacking, where cybercriminals design their phishing webpage to mimic known and trusted websites. often, they try to look like popular social media services, official government domains, or banking websites. This guide walks through the most common and damaging phishing attack examples. you’ll see how these scams work, what they look like, and what to do when they land in your inbox. Discover real world phishing examples by attack type, industry, emotional trigger, and delivery vector. learn how to spot phishing attack types and protect your organization.
Comments are closed.