Phishing Vs Spoofing Mobilebd

Spoofing Vs Phishing Differences Between Spoofing And Phishing Spoofing and phishing are two types of attacks that can be used to extract sensitive information from users. both use fraudulent email messages to trick users into divulging personal information or downloading malware, but they differ in how they operate. Phishing and spoofing attacks are similar, but they are two distinct cybersecurity threats. understanding the difference between phishing and spoofing and the dangers they pose can boost your cybersecurity awareness and help you protect your business.
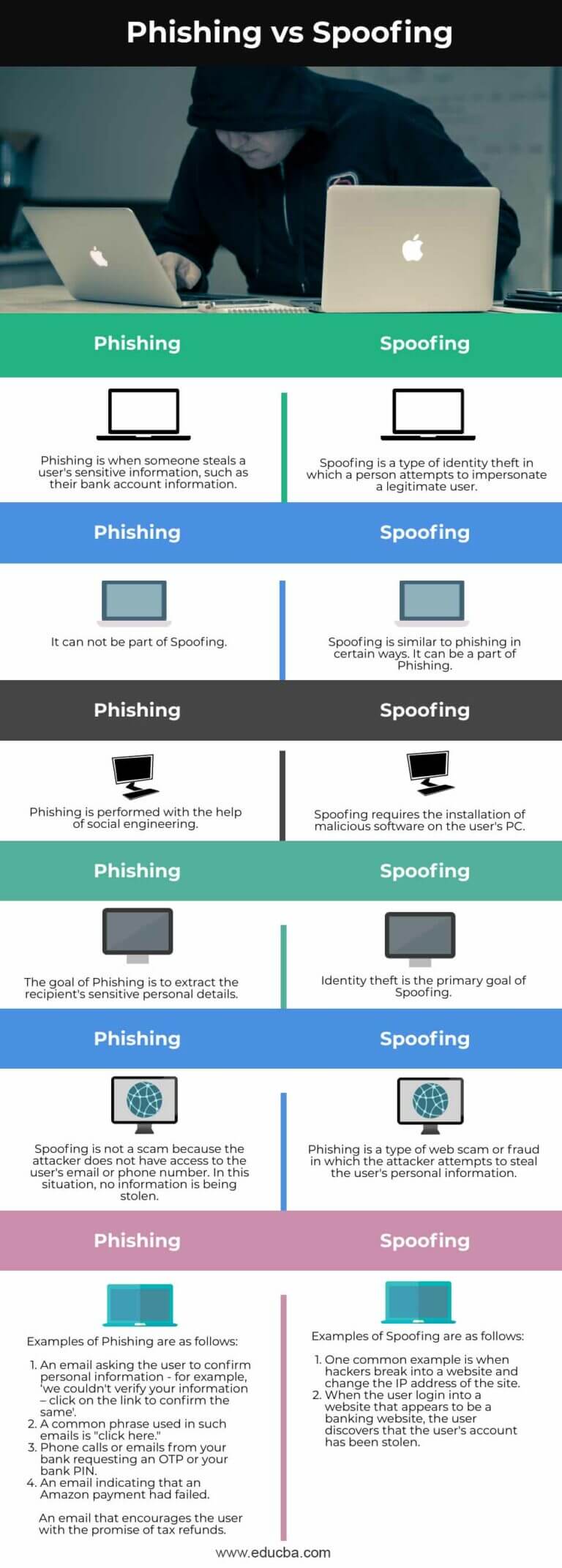
Phishing Vs Spoofing Learn The Key Differences And Comparisons It is important to comprehend the difference between spoofing and phishing so that one can avoid the two at any given point. in this article, we will also look at the definition of each term, how they perform, and compare among them. The threat landscape is evolving, and it’s becoming incredibly concerning. this guide will cover everything you need to know about spoofing vs. phishing. we will discuss the risks of phishing and spoofing. you will also learn how to prevent them and what you can do to stay protected. Learn the key differences between phishing and spoofing attacks. understand how each works, their real world risks, and how to protect your business today. Spoofing and phishing are dangerous and prevalent forms of social engineering attacks that exploit both technical and psychological vulnerabilities. in cyber security training, it’s emphasized that spoofing focuses on impersonation, while phishing targets the victim’s response through deception.

Phishing Vs Spoofing Learn The Key Differences And Comparisons Learn the key differences between phishing and spoofing attacks. understand how each works, their real world risks, and how to protect your business today. Spoofing and phishing are dangerous and prevalent forms of social engineering attacks that exploit both technical and psychological vulnerabilities. in cyber security training, it’s emphasized that spoofing focuses on impersonation, while phishing targets the victim’s response through deception. Learn the difference between spoofing and phishing attacks and discover simple steps to protect yourself and your data online. Spoofing and phishing are distinct techniques but are often used in conjunction. for example, a phishing email might contain a link that directs the recipient to a spoofed website designed to steal login credentials. Spoofing and phishing are cyberattacks designed to steal sensitive data. learn the key differences, how each one works, and how to spot and avoid them. Understanding the difference between phishing and spoofing is essential because each requires a different type of defense. this guide breaks down how both attacks work, where they overlap, how to spot them, and what your organization needs to do to defend against both.
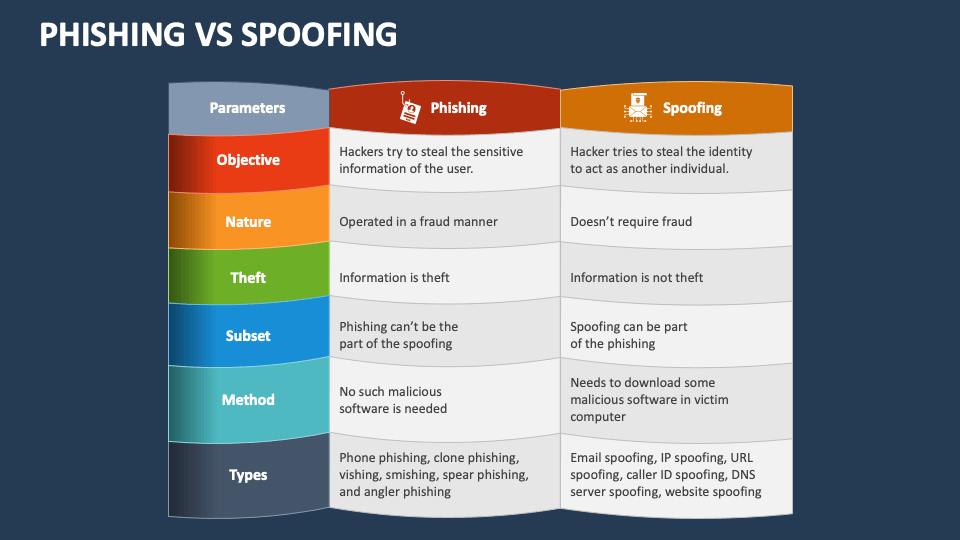
Phishing Vs Spoofing Powerpoint And Google Slides Template Ppt Slides Learn the difference between spoofing and phishing attacks and discover simple steps to protect yourself and your data online. Spoofing and phishing are distinct techniques but are often used in conjunction. for example, a phishing email might contain a link that directs the recipient to a spoofed website designed to steal login credentials. Spoofing and phishing are cyberattacks designed to steal sensitive data. learn the key differences, how each one works, and how to spot and avoid them. Understanding the difference between phishing and spoofing is essential because each requires a different type of defense. this guide breaks down how both attacks work, where they overlap, how to spot them, and what your organization needs to do to defend against both.
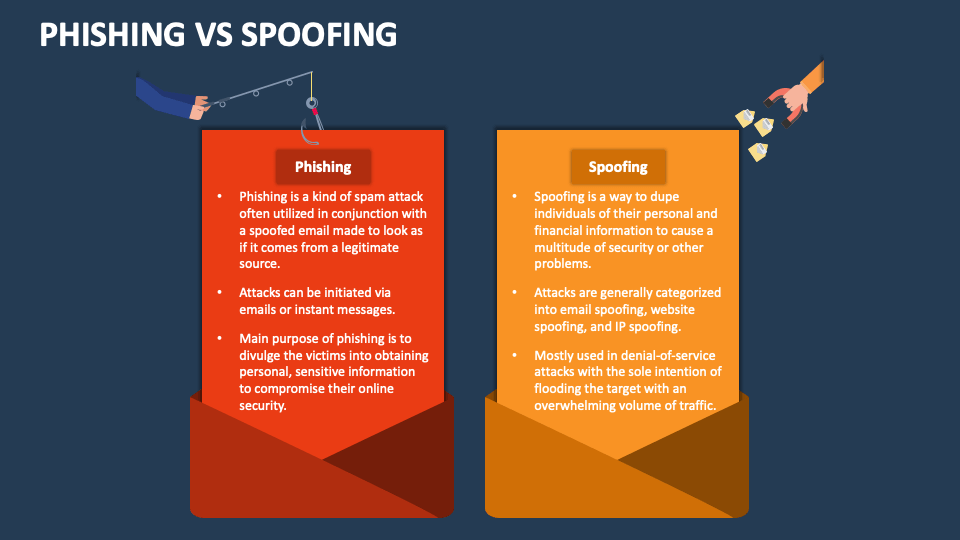
Phishing Vs Spoofing Powerpoint And Google Slides Template Ppt Slides Spoofing and phishing are cyberattacks designed to steal sensitive data. learn the key differences, how each one works, and how to spot and avoid them. Understanding the difference between phishing and spoofing is essential because each requires a different type of defense. this guide breaks down how both attacks work, where they overlap, how to spot them, and what your organization needs to do to defend against both.

Phishing Vs Spoofing Mobilebd
Comments are closed.