Phishing Targeted Attacks Breach Secure Now

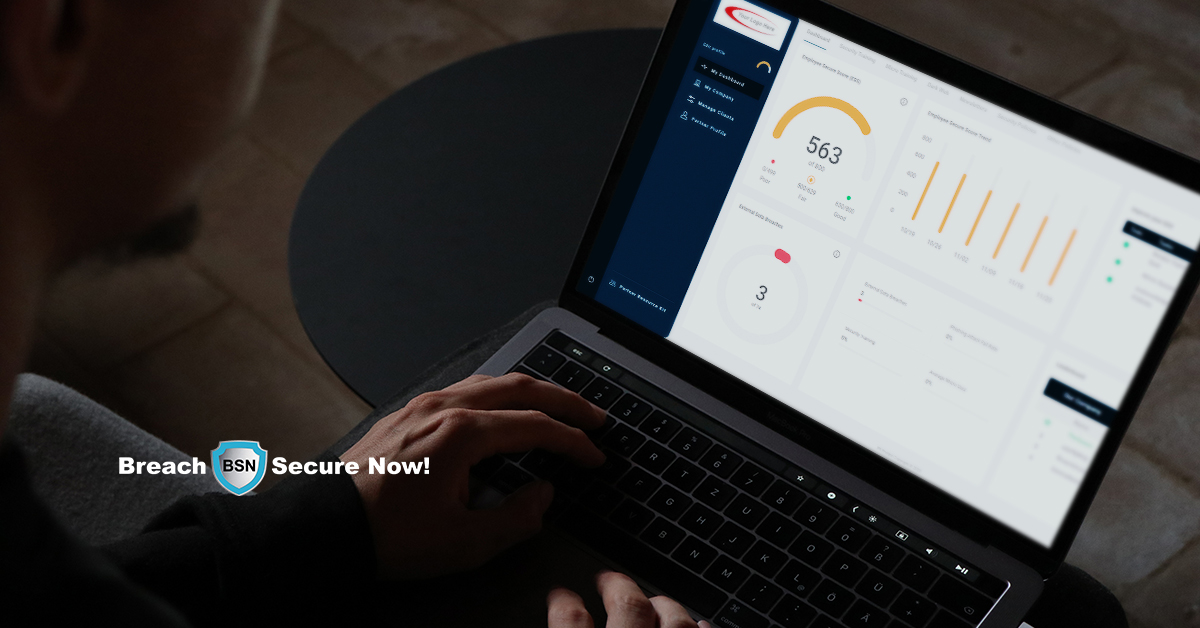
Phishing Targeted Attacks Breach Secure Now Breach secure now offers training tools that are varied to address the different ways that we all learn. ongoing training that includes video modules, graphics that provide visual reminders on social media or in print, and integrated phishing tools are all part of our approach. Keep your employees aware and informed of the risks of email phishing and other email attacks with our breach secure now security awareness training.
Phishing Breach Secure Now If you, or someone you know, suspects that you have been targeted or compromised by a russian gru cyber intrusion, nsa recommends reporting the activity to your local fbi field office, filing a complaint with the internet crime complaint center (ic3), or otherwise following your organization’s incident reporting requirements. Cyber news check out top news and articles about cyber security, malware attack updates and more at cyware . our machine learning based curation engine brings you the top and relevant cyber security content. read more!. Signature based and reputation based detection provides a solid email security foundation — but, on its own, it’s no longer enough to hold back the tide of phishing attacks targeting organizations. Criminals often use phishing to steal credentials, access business accounts or install ransomware that locks systems and demands payment. according to the fbi’s 2024 internet crime report, phishing topped the list of the five most reported cybercrimes, with 193,407 complaints.
Combat Phishing With Breach Secure Now S Training Solutions Signature based and reputation based detection provides a solid email security foundation — but, on its own, it’s no longer enough to hold back the tide of phishing attacks targeting organizations. Criminals often use phishing to steal credentials, access business accounts or install ransomware that locks systems and demands payment. according to the fbi’s 2024 internet crime report, phishing topped the list of the five most reported cybercrimes, with 193,407 complaints. By choosing breach secure now, organizations gain access to expertly designed training programs that are continuously updated to reflect the latest threats and best practices. Once the user accepts the teams invite, the attacker provides a sharepoint link containing malicious payloads, which could lead to critical security breaches. recent trends in social engineering attacks highlight this adaptability, with attackers varying their tactics based on the target. Explore the latest news, real world incidents, expert analysis, and trends in phishing attack — only on the hacker news, the leading cybersecurity and it news platform. This report dives deep into exclusive 2025 phishing data, industry by industry breach breakdowns, and actual attack case studies. you’ll see exactly how threat actors have adapted—and more importantly, what defensive strategies are actively working right now.

How To Avoid Phishing Emails On Day 19 Breach Secure Now Posted On By choosing breach secure now, organizations gain access to expertly designed training programs that are continuously updated to reflect the latest threats and best practices. Once the user accepts the teams invite, the attacker provides a sharepoint link containing malicious payloads, which could lead to critical security breaches. recent trends in social engineering attacks highlight this adaptability, with attackers varying their tactics based on the target. Explore the latest news, real world incidents, expert analysis, and trends in phishing attack — only on the hacker news, the leading cybersecurity and it news platform. This report dives deep into exclusive 2025 phishing data, industry by industry breach breakdowns, and actual attack case studies. you’ll see exactly how threat actors have adapted—and more importantly, what defensive strategies are actively working right now.

Phishing Scams Msp Cybersecurity Itsolutions Cybertraining Explore the latest news, real world incidents, expert analysis, and trends in phishing attack — only on the hacker news, the leading cybersecurity and it news platform. This report dives deep into exclusive 2025 phishing data, industry by industry breach breakdowns, and actual attack case studies. you’ll see exactly how threat actors have adapted—and more importantly, what defensive strategies are actively working right now.
Iot Security Services Association Learn More About Breach Secure Now
Comments are closed.