Phishing Pole Devpost

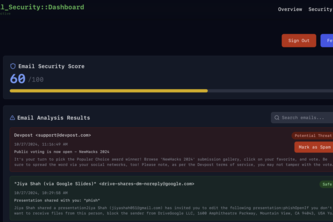
Phishing Pole Devpost Our app is built to recognize phishing scams that have been sent to the user. it's simple to use the user can ask the server whether a message or link is a potential phishing scam and it will provide a response indicating if the user should proceed with caution or delete the message altogether. User friendly ui: phishing pole has a clean and easy to use user interface that makes it simple for users to identify and protect themselves against phishing attacks.
Phishing Reel Devpost The core of phish hook is its simulation. we used ai to generate the voice scam calls and phishing emails that power every quiz and scenario, making sure the material mirrors what real attacks actually look and sound like rather than sanitized textbook examples. In the phishingrod project, our team harnessed linear algebra and ai synergy, fine tuning llms with lora for precise phishing detection. confronting large datasets and intricate cybersecurity challenges, we navigated technical complexities, emphasizing a meticulous, security first approach. Flag phishing emails using natural language processing to identify common phrases, keywords and deceptive tactics used by phishers. integrate with real time apis to receive the latest phishing urls, allowing for continuous model updates and improved detection accuracy. Phishing pot is a collection of real phishing samples collected via honey pots. the purpose of this repository is to provide a reliable database for researchers and developers of detection solutions.

Phishing Defender Devpost Flag phishing emails using natural language processing to identify common phrases, keywords and deceptive tactics used by phishers. integrate with real time apis to receive the latest phishing urls, allowing for continuous model updates and improved detection accuracy. Phishing pot is a collection of real phishing samples collected via honey pots. the purpose of this repository is to provide a reliable database for researchers and developers of detection solutions. This tool automates key components of a phishing campaign to demonstrate how attackers might operate. it highlights the importance of understanding phishing methods and strengthens awareness of social engineering threats. Discover the best phishing tools to protect your organization from cyber threats and strengthen your defenses against phishing attacks. See something suspicious? knight ai instantly analyses websites, emails, and social media for phishing and scams, flags the threat, explains why it's dangerous, and tells you exactly what to do. Phishing is a form of social engineering and a scam where attackers deceive people into revealing sensitive information [1] or installing malware such as viruses, worms, adware, or ransomware.
Comments are closed.