Phishing Fordefence Forensics Cyber Security

What Is Cybersecurity Forensics Amr Digital Forensics At fordefence, our phishing tests are designed to secure your systems against fraudulent schemes where cyber attackers use fake emails and websites to deceive users and steal personal information. Phishing is a growing form of cybercrime that poses a serious threat to information security in the digital world. this article aims to analyze the latest trends in phishing attacks and.
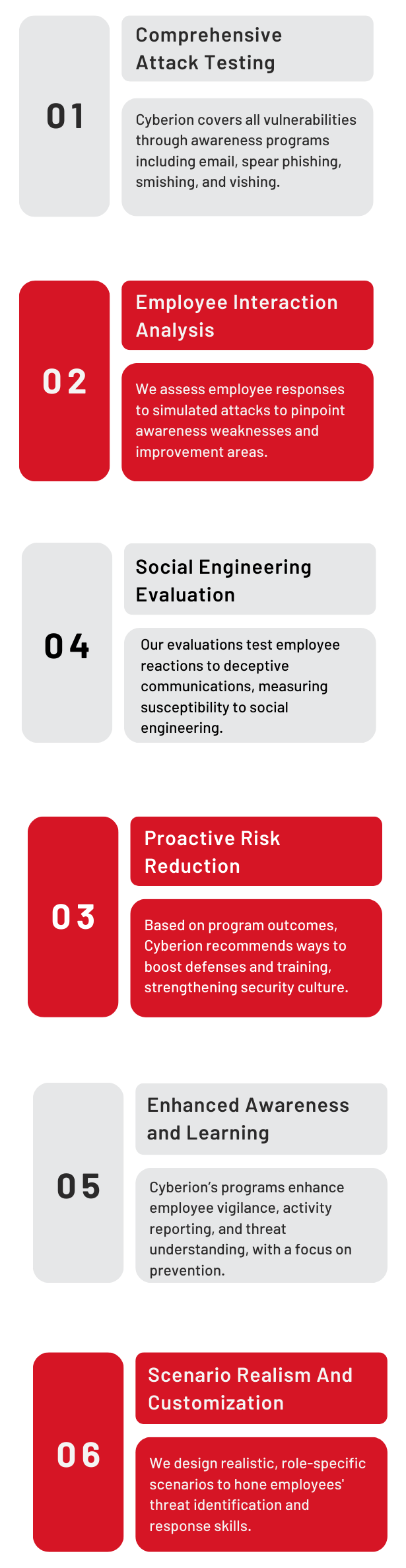
Cyberion Labs Phishing attacks continue to pose a significant threat to cybersecurity, with perpetrators becoming increasingly sophisticated in crafting convincing fraudulent methods. this article examines the forensic analysis process used to effectively investigate phishing attacks. Discover the types, process, and best practices of cybersecurity forensics to effectively investigate and mitigate security incidents. For the general audience interested in cyber security, the paper highlights the current trends concerning phishing and summarizes the state of the art of mitigation strategies. Advanced email security systems now employ artificial intelligence to analyze email patterns and identify suspicious behavior in real time. unlike traditional signature based detection, ai powered solutions can recognize subtle indicators of phishing attempts even from previously unknown sources.

What Is Phishing In Cyber Security Types Risks Prevention Tips For the general audience interested in cyber security, the paper highlights the current trends concerning phishing and summarizes the state of the art of mitigation strategies. Advanced email security systems now employ artificial intelligence to analyze email patterns and identify suspicious behavior in real time. unlike traditional signature based detection, ai powered solutions can recognize subtle indicators of phishing attempts even from previously unknown sources. Phishing is a form of social engineering that uses deceptive emails or messages to trick recipients into clicking on malicious links or providing sensitive information. these attacks prey on human psychology, exploiting emotions like fear, urgency, and curiosity. This guide, tailored for the role of a security forensics analyst, explores how business intelligence and data analytics can be integrated into the investigative process to uncover the root causes of phishing attacks while ensuring quick remediation and improved future defenses. This guide outlines phishing techniques commonly used by malicious actors and provides guidance for network defenders and software manufacturers. Phishing remains a significant cybersecurity threat, targeting individuals and organizations to access confidential data. as techniques evolve, innovative protective measures are essential. this paper offers a detailed overview of phishing defense strategies, focusing on both technological solutions and human centered approaches.
Comments are closed.