Phishing Comptia Security Sy0 701 2 2
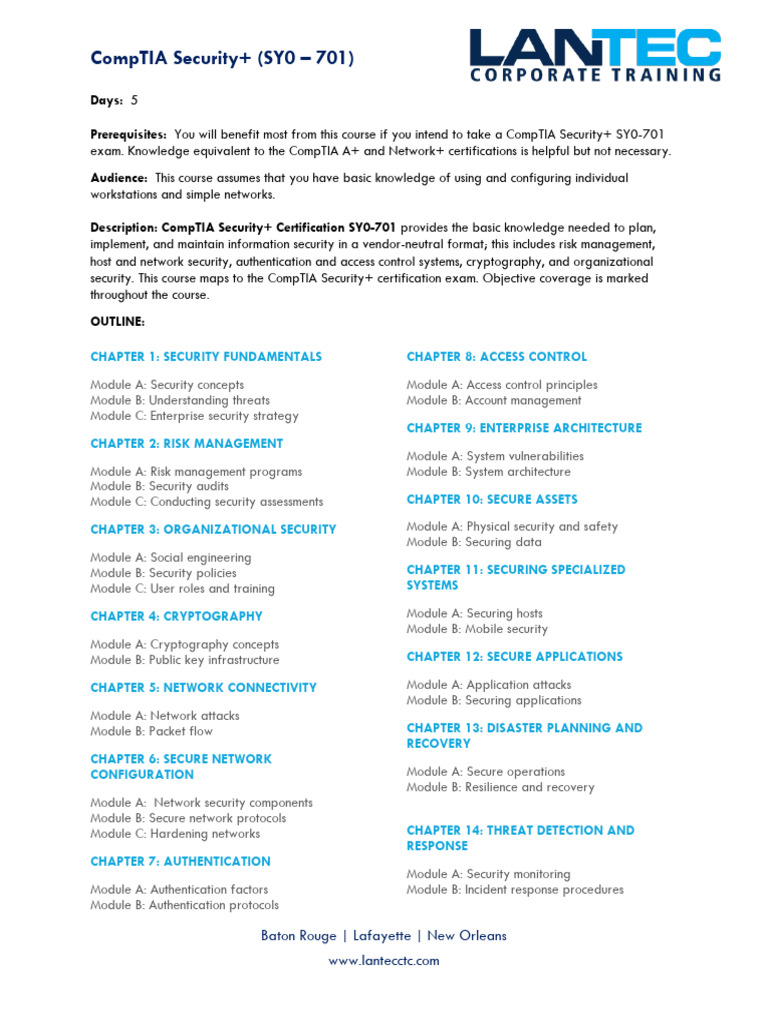
Comptia Security Sy0 701 Pdf Information Security Computer Phishing continues to be a popular method of network infiltration. in this video, you'll learn about different phishing techniques, and i'll demonstrate a real world example from my email inbox. Spot advanced phishing tactics and network infiltration techniques in comptia security sy0 701. learn real world prevention with professor messer.

Comptia Security Sy0 701 Pdf Information Security Computer Study with quizlet and memorize flashcards containing terms like what is phishing?, what are common methods used in phishing attacks?, what type of information do phishing attacks typically seek? and more. 022 phishing – comptia security sy0 701 – 2.2 quiz for 12th grade students. find other quizzes for computers and more on wayground for free!. Can't find it? generate it with atlas. study, write, and solve faster with the most accurate ai for school. Phishing is a term we use to describe social engineering that uses a number of different communications methods to make you think that something is real, when in fact, it really isn't.

Comptia Security Sy0 701 Book 480 585 Pdf Can't find it? generate it with atlas. study, write, and solve faster with the most accurate ai for school. Phishing is a term we use to describe social engineering that uses a number of different communications methods to make you think that something is real, when in fact, it really isn't. Chat with "phishing comptia security sy0 701 2.2" by professor messer. 📌 tl;dr phishing uses deceptive communication methods like email, text, and pho. There’s the fake check scam, the phone verification code scam, and many others. i would highly recommend you become familiar with these types of scams and phishing techniques. you may be the person who’s able to stop your friends or family from falling victim to one of these scams. Comptia security exam insights. the document contains a series of exam questions and answers related to cybersecurity topics, including threat actors, data transformation algorithms, social engineering attacks, and firewall acl configurations. 1.2 hardware security module (hsm) a hardware security module (hsm) is a physical device used to generate, store, and manage cryptographic keys. hsms provide a high level of security for cryptographic operations by ensuring keys are never exposed in an unprotected form.
Github Arslns Comptia Security Sy0 701 Get Ready To Excel In Comptia Chat with "phishing comptia security sy0 701 2.2" by professor messer. 📌 tl;dr phishing uses deceptive communication methods like email, text, and pho. There’s the fake check scam, the phone verification code scam, and many others. i would highly recommend you become familiar with these types of scams and phishing techniques. you may be the person who’s able to stop your friends or family from falling victim to one of these scams. Comptia security exam insights. the document contains a series of exam questions and answers related to cybersecurity topics, including threat actors, data transformation algorithms, social engineering attacks, and firewall acl configurations. 1.2 hardware security module (hsm) a hardware security module (hsm) is a physical device used to generate, store, and manage cryptographic keys. hsms provide a high level of security for cryptographic operations by ensuring keys are never exposed in an unprotected form.

Vets2pm Cyber Comptia Security Sy0 701 Course Vets2pm Premier Comptia security exam insights. the document contains a series of exam questions and answers related to cybersecurity topics, including threat actors, data transformation algorithms, social engineering attacks, and firewall acl configurations. 1.2 hardware security module (hsm) a hardware security module (hsm) is a physical device used to generate, store, and manage cryptographic keys. hsms provide a high level of security for cryptographic operations by ensuring keys are never exposed in an unprotected form.
Comments are closed.