Phishing Attack Flow Figure 1
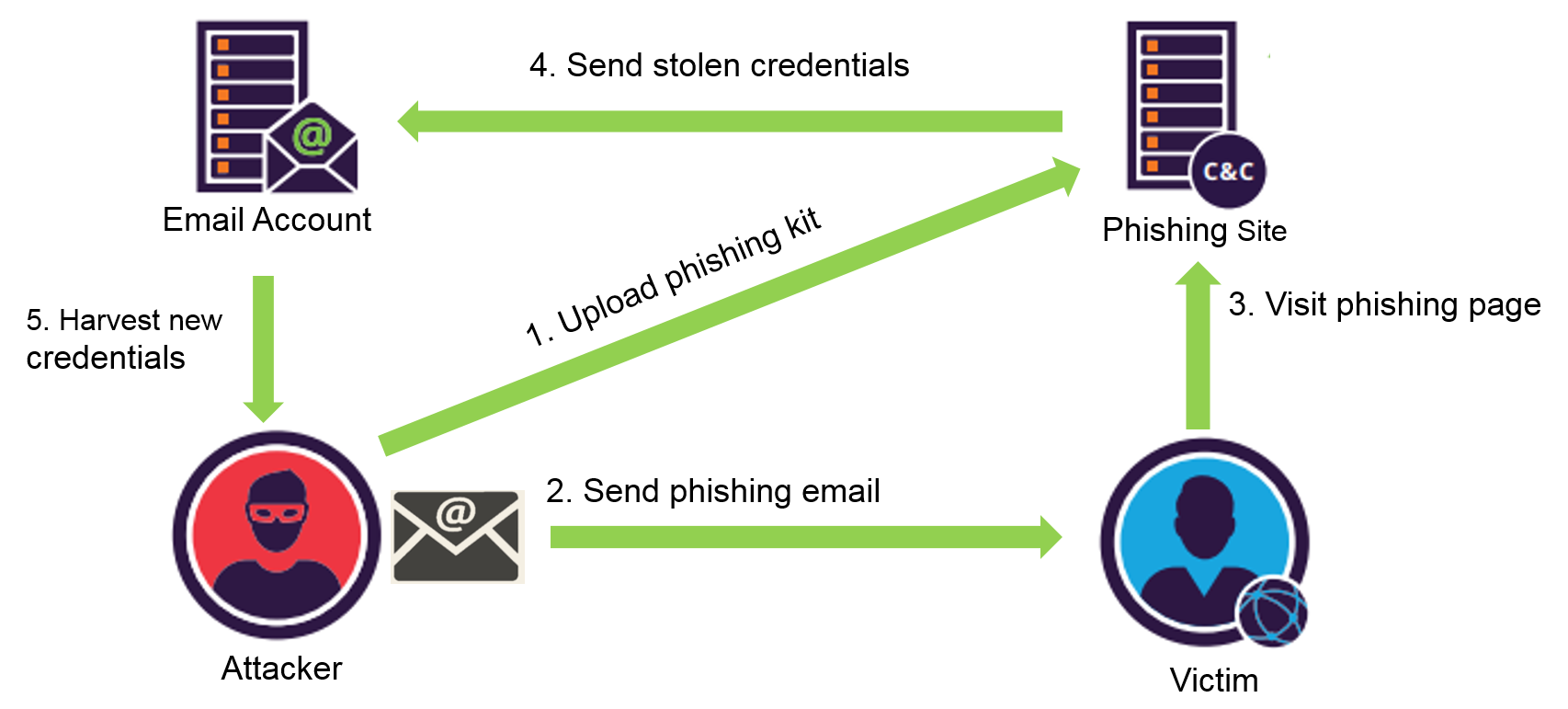
Phishing Attack Flow Figure 1 Figure 1 depicts the general process flow for a phishing attack that contains four phases; these phases are elaborated in proposed phishing anatomy. Included figures: phishing attack workflow (figure 1), and mockup comparison of real vs fake instagram login (figure 2). these images are illustrative; for publication quality figures, replace mockups with high fidelity screenshots and redaction as needed.

Flow Of A Phishing Attack Source Arxiv Org Download Scientific Diagram Figure 1 depicts the general process flow for a phishing attack that contains four phases; these phases are elaborated in proposed phishing anatomy. however, as shown in figure 1, in most attacks, the phishing process is initiated by gathering information about the target. The phishing incident response playbook contains all 7 steps defined by the nist incident response process. You can easily edit this template using creately. you can export it in multiple formats like jpeg, png and svg and easily add it to word documents, powerpoint (ppt) presentations, excel or any other documents. you can export it as a pdf for high quality printouts. Phishing is a form of social engineering in which a cyber threat actor poses as a trustworthy colleague, acquaintance, or organization to lure a victim into providing sensitive information or network access. the lures can come in the form of an email, text message, or even a phone call.

Phishing Information Flow 7 Download Scientific Diagram You can easily edit this template using creately. you can export it in multiple formats like jpeg, png and svg and easily add it to word documents, powerpoint (ppt) presentations, excel or any other documents. you can export it as a pdf for high quality printouts. Phishing is a form of social engineering in which a cyber threat actor poses as a trustworthy colleague, acquaintance, or organization to lure a victim into providing sensitive information or network access. the lures can come in the form of an email, text message, or even a phone call. This paper proposes an anti phishing approach for iot systems in fog networks that leverages machine learning algorithms, including a fusion with deep learning techniques. This slide demonstrates the working flow of a phishing attack. the purpose of this slide is to outline the various phases of phishing scams such as campaign crafted, payloads, impersonation, execution, ransomware and encrypts on target. Phishing emails trick you into giving away personal information. use our flowchart to check whether you’re being phished. In this chapter, we first describe our high level methodology to track the information flow in each step in figure 2.1, and then introduce the measurement tool designed by us.

Phishing Attack Life Cycle Download Scientific Diagram This paper proposes an anti phishing approach for iot systems in fog networks that leverages machine learning algorithms, including a fusion with deep learning techniques. This slide demonstrates the working flow of a phishing attack. the purpose of this slide is to outline the various phases of phishing scams such as campaign crafted, payloads, impersonation, execution, ransomware and encrypts on target. Phishing emails trick you into giving away personal information. use our flowchart to check whether you’re being phished. In this chapter, we first describe our high level methodology to track the information flow in each step in figure 2.1, and then introduce the measurement tool designed by us.

Anatomy Of Phishing Attack Figure 6 Reliaquest Phishing emails trick you into giving away personal information. use our flowchart to check whether you’re being phished. In this chapter, we first describe our high level methodology to track the information flow in each step in figure 2.1, and then introduce the measurement tool designed by us.

Sequence Of Stages Of A Phishing Attack Download Scientific Diagram
Comments are closed.