Phishing And Spoofing Attacks

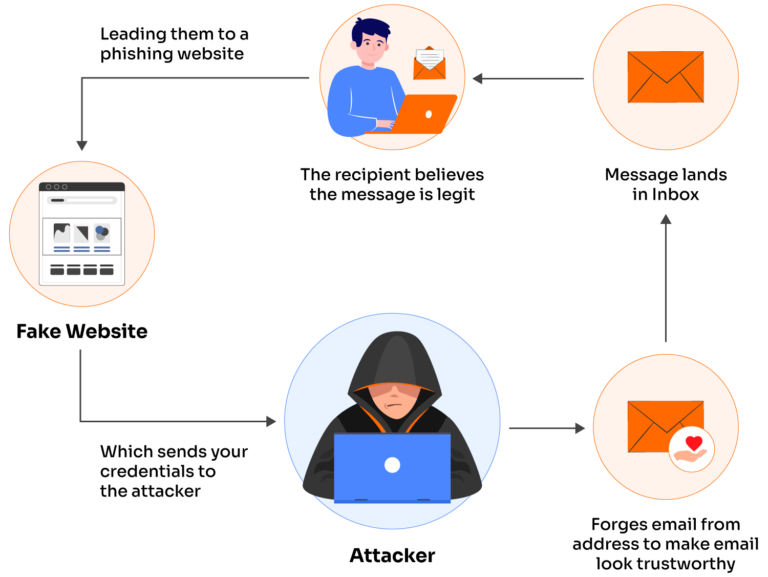
How Is Email Spoofing Used In Phishing Attacks It Service And Spoofing attacks resemble identity theft while phishing attacks attempt to steal sensitive information. notably, a phishing attempt may begin with a spoofing attack. Spoofing and phishing are key parts of business email compromise scams. spoofing is when someone disguises an email address, sender name, phone number, or website url—often just by changing.

Spoofing Attacks Vs Phishing Scams Mrghost Spoofing can be used to gain access to the victim's login credentials, while phishing can be used to steal credit card details, passwords, and other sensitive information. technically simple: both spoofing and phishing attacks can be executed with basic technical skills. Understand the key differences between spoofing vs phishing, their risks, examples, and how to protect against these cyber threats. Almost any type of cyberattack can start with spoofing or phishing, so knowing how to spot these tactics is a critical safety net your organization needs to have. this blog breaks down the key differences between spoofing and phishing in the wild. In this blog, we explain how threat actors are exploiting these routing scenarios and provide observations from related attacks. we provide specific examples—including technical analysis of phishing messages, spoof protections, and email headers—to help identify this attack vector.
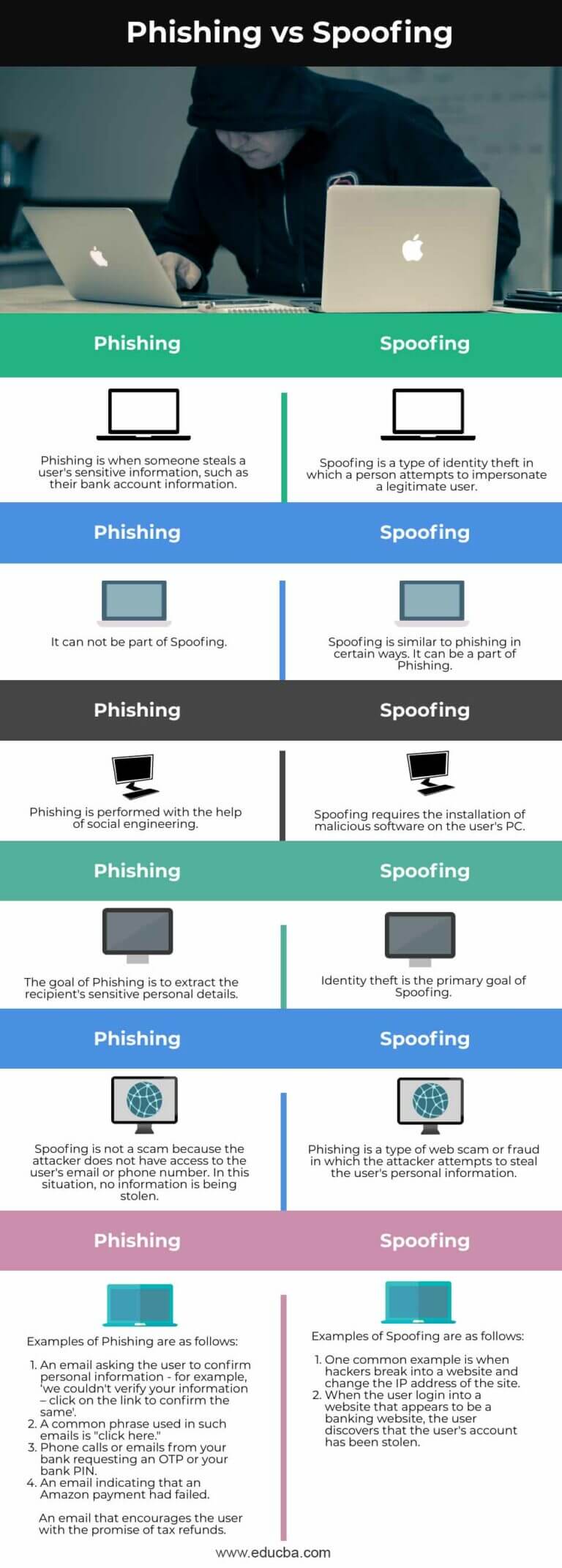
Phishing Vs Spoofing Learn The Key Differences And Comparisons Almost any type of cyberattack can start with spoofing or phishing, so knowing how to spot these tactics is a critical safety net your organization needs to have. this blog breaks down the key differences between spoofing and phishing in the wild. In this blog, we explain how threat actors are exploiting these routing scenarios and provide observations from related attacks. we provide specific examples—including technical analysis of phishing messages, spoof protections, and email headers—to help identify this attack vector. Learn what the differences are between spoofing and phishing, two types of attacks that are among the most common cyberattacks organizations face. What are the differences between phishing and spoofing? learn how to identify and protect against these common cybersecurity threats. Discover spoofing attacks with types, examples, risks and prevention methods to help you stay safe from phishing, fraud and data theft. Spoofing and phishing are dangerous and prevalent forms of social engineering attacks that exploit both technical and psychological vulnerabilities. in cyber security training, it’s emphasized that spoofing focuses on impersonation, while phishing targets the victim’s response through deception.
Phishing Vs Spoofing What S The Difference Valimail Learn what the differences are between spoofing and phishing, two types of attacks that are among the most common cyberattacks organizations face. What are the differences between phishing and spoofing? learn how to identify and protect against these common cybersecurity threats. Discover spoofing attacks with types, examples, risks and prevention methods to help you stay safe from phishing, fraud and data theft. Spoofing and phishing are dangerous and prevalent forms of social engineering attacks that exploit both technical and psychological vulnerabilities. in cyber security training, it’s emphasized that spoofing focuses on impersonation, while phishing targets the victim’s response through deception.

Phishing Vs Spoofing And How To Avoid It Bank Of Commerce Discover spoofing attacks with types, examples, risks and prevention methods to help you stay safe from phishing, fraud and data theft. Spoofing and phishing are dangerous and prevalent forms of social engineering attacks that exploit both technical and psychological vulnerabilities. in cyber security training, it’s emphasized that spoofing focuses on impersonation, while phishing targets the victim’s response through deception.
Comments are closed.