Phase 2 Pdf Transmission Control Protocol Port Computer Networking

Transmission Control Protocol In Computer Networks 1 1 Pdf Phase 2 free download as pdf file (.pdf), text file (.txt) or read online for free. phase 2 of penetration testing involves scanning and enumeration of the target network. This document specifies the transmission control protocol (tcp). tcp is an important transport layer protocol in the internet protocol stack, and it has continuously evolved over decades of use and growth of the internet.
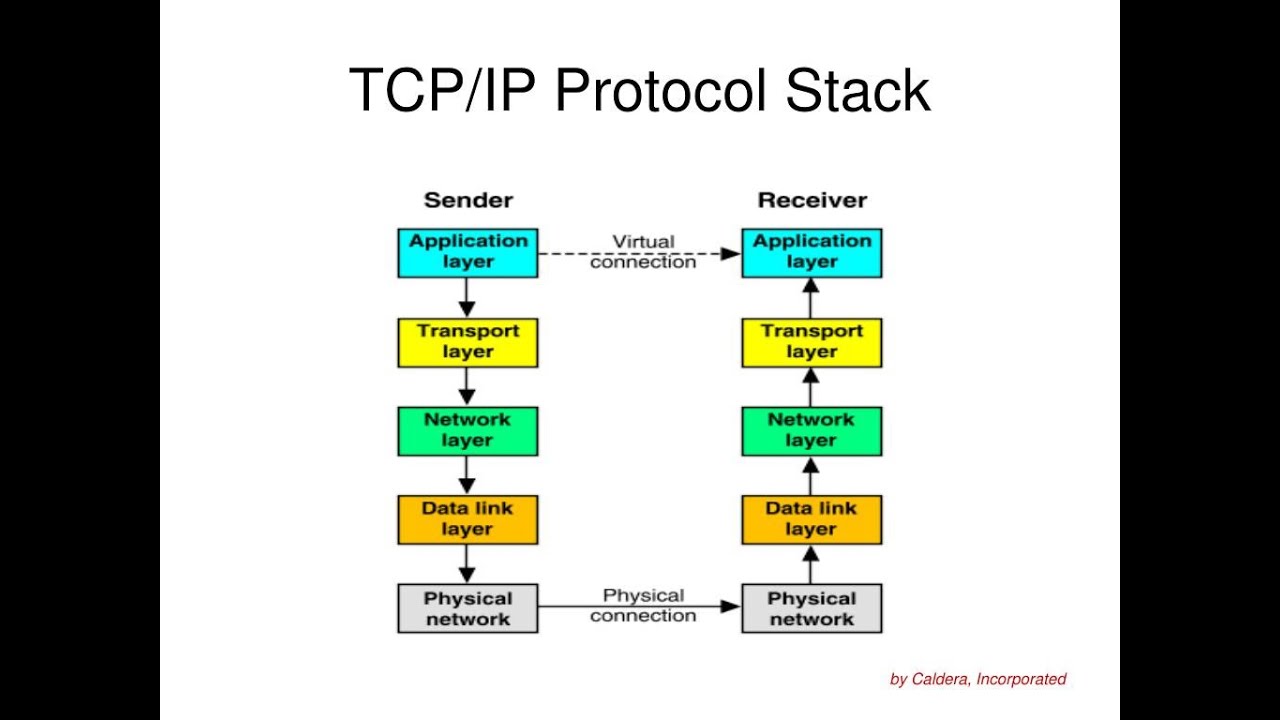
Internet Protocol Transmission Control Protocol At Gary Delariva Blog End to end flow control is not enough! independent senders can each have flow control with their receivers, but together can still inject large number of packets in the network. Tcp is connection oriented and full duplex. the maximum segment size (mss)is set during connection establishment. reliability is achieved using acknowledgments, round trip delay estimations and data retransmission. tcp uses a variable window mechanism for flow control. Tcp uses flow control to maximize throughput and avoid packet loss. congestion control mechanisms allow tcp to react and recover from network congestion. tsaps are identified by 16bit port numbers. 65536 port numbers are available (0 65535, but 0 is never used). At that time, most students were not users of computer networks and it was useful to explain computer networks by building the corresponding protocols from the simplest, in the physical layer, up to the application layer.

09 Networking Pdf Network Socket Transmission Control Protocol Tcp uses flow control to maximize throughput and avoid packet loss. congestion control mechanisms allow tcp to react and recover from network congestion. tsaps are identified by 16bit port numbers. 65536 port numbers are available (0 65535, but 0 is never used). At that time, most students were not users of computer networks and it was useful to explain computer networks by building the corresponding protocols from the simplest, in the physical layer, up to the application layer. To establish connection tcp uses three way handshake. client sends initial syn segment with syn set and an initial sequence number (isn). if server has process listening at target port it will usually accept connection. The transmission control protocol (tcp) is one of the main protocols of the internet protocol suite, providing reliable, ordered, and error checked delivery of a stream of octets (bytes) between applications running on hosts communicating via an ip network. When sender’s retransmit timer expires, two indistinguishable cases (why?): in latter case, duplicate data packet reaches receiver! how to prevent receiver from passing duplicates to application? how many tombstones must receiver store? also should cover layer 3 source and destination!. Cs4450 computer networks: architecture and protocols lecture 20 reliable transport and tcp.

Transmission Control Protocol To establish connection tcp uses three way handshake. client sends initial syn segment with syn set and an initial sequence number (isn). if server has process listening at target port it will usually accept connection. The transmission control protocol (tcp) is one of the main protocols of the internet protocol suite, providing reliable, ordered, and error checked delivery of a stream of octets (bytes) between applications running on hosts communicating via an ip network. When sender’s retransmit timer expires, two indistinguishable cases (why?): in latter case, duplicate data packet reaches receiver! how to prevent receiver from passing duplicates to application? how many tombstones must receiver store? also should cover layer 3 source and destination!. Cs4450 computer networks: architecture and protocols lecture 20 reliable transport and tcp.

Computer Networks Module 2 Final Pdf Error Detection And Correction When sender’s retransmit timer expires, two indistinguishable cases (why?): in latter case, duplicate data packet reaches receiver! how to prevent receiver from passing duplicates to application? how many tombstones must receiver store? also should cover layer 3 source and destination!. Cs4450 computer networks: architecture and protocols lecture 20 reliable transport and tcp.
Comments are closed.