Perm Pair Android Malware Detection Using Permission Pairs

Detecting Android Malware Via Permission Pairs Pdf Malware In this paper, we proposed an innovative detection model, named permpair, that constructs and compares the graphs for malware and normal samples by extracting the permission pairs from the manifest file of an application. In this paper, we proposed an innovative detection model, named permpair, that constructs and compares the graphs for malware and normal samples by extracting the permission pairs from.

Android Malware Detection Techniques Download Scientific Diagram In this paper, we proposed an innovative detection model, named permpair, that constructs and compares the graphs for malware and normal samples by extracting the permission pairs from the manifest file of an application. In this paper, we proposed an innovative detection model, named permpair , that constructs and compares the graphs for malware and normal samples by extracting the permission pairs from the manifest file of an application. Permpair: android malware detection using permission pairs. ieee transactions on information forensics and security, 15:1968 1982, 2020. [doi] abstract is missing. Arora et al. have contributed by developing a framework that analyzes permission pairs to detect malware, proposing algorithms for graph construction, merging, and comparison, and demonstrating improved detection rates compared to existing mobile security solutions.
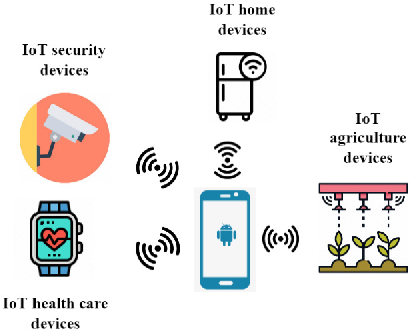
Figure 1 From Iot Based Android Malware Detection Using Graph Neural Permpair: android malware detection using permission pairs. ieee transactions on information forensics and security, 15:1968 1982, 2020. [doi] abstract is missing. Arora et al. have contributed by developing a framework that analyzes permission pairs to detect malware, proposing algorithms for graph construction, merging, and comparison, and demonstrating improved detection rates compared to existing mobile security solutions. Android malware android security malware detection permissions pair graph smartphone security references this publication has 45 references indexed in scilit:. In this paper, we proposed an innovative detection model, named permpair, that constructs and compares the graphs for malware and normal samples by extracting the permission pairs from the manifest file of an application. Article “permpair: android malware detection using permission pairs” detailed information of the j global is a service based on the concept of linking, expanding, and sparking, linking science and technology information which hitherto stood alone to support the generation of ideas. In this study, we propose a novel hybrid approach to detect android malware, wherein static features in conjunction with dynamic features of smart phone applications are employed.

The Proposed Android Malware Detection System Download Scientific Diagram Android malware android security malware detection permissions pair graph smartphone security references this publication has 45 references indexed in scilit:. In this paper, we proposed an innovative detection model, named permpair, that constructs and compares the graphs for malware and normal samples by extracting the permission pairs from the manifest file of an application. Article “permpair: android malware detection using permission pairs” detailed information of the j global is a service based on the concept of linking, expanding, and sparking, linking science and technology information which hitherto stood alone to support the generation of ideas. In this study, we propose a novel hybrid approach to detect android malware, wherein static features in conjunction with dynamic features of smart phone applications are employed.
Comments are closed.