Pentest Example Pdf Password Http Cookie

Pentest Example Download Free Pdf Password Http Cookie When you login the cookie that you receive has to be always the same. how to detect and attack: create 2 users with almost the same data (username, password, email ) and try to discover some pattern inside the given cookie. Pentest example free download as pdf file (.pdf), text file (.txt) or read online for free. this security testing report provides an executive summary of a pentest conducted on an unnamed system.
Cookie Pdf Http Cookie Art Will demonstrate how to create the “alert (1)” of pdf injection and how to improve it to inject javascript that can steal credentials and open a malicious link. Attackers can intercept sensitive information, such as usernames and passwords, and potentially use it for malicious purposes. this attack can also be used to launch other types of attacks, such as man in the middle attacks or ransomware attacks. We recommend always changing the default passwords to more secure and uncommon ones, that should be at least 8 characters long and contain a mixture of lowercase, uppercase letters, numbers and special characters. Description of finding: the testers observed the secure flag to be missing from the “token” cookie. if the secure flag is set on a cookie, then browsers will not submit the cookie in any requests that use an unencrypted http connection, thereby preventing the cookie from being trivially intercepted by an attacker monitoring network traffic.

Pentest Study Tips And Resources Pdf System Software Computing We recommend always changing the default passwords to more secure and uncommon ones, that should be at least 8 characters long and contain a mixture of lowercase, uppercase letters, numbers and special characters. Description of finding: the testers observed the secure flag to be missing from the “token” cookie. if the secure flag is set on a cookie, then browsers will not submit the cookie in any requests that use an unencrypted http connection, thereby preventing the cookie from being trivially intercepted by an attacker monitoring network traffic. The security headers are displayed in the http response and indicate the way the browser is suppose to operate in regards to the execution of the html. they are checked before the rest of the. This brute force attack uncovered a password of “nanotechnology1” for the admin user. we were able to leverage these credentials to successfully gain unauthorized access to the protected portion of the website (figure 6). please see appendix a for more information on the exploited vulnerability. The application’s use of cryptographically signed session cookies prevented tampering, and direct use of the cookie in the attacker’s browser failed, likely due to server side validation checks (e.g., ip address or user agent binding). therefore, it was necessary to steal a live session cookie from a legitimate, active admin ses sion. Using an open redirect vulnerability, it is possible to steal the application user's sensitive cookie. specifically, the access token and id token cookies. these two cookies will allow an attacker to interact with the application's graphql scheme as the victim. the following http request was observed while interacting with the application:.
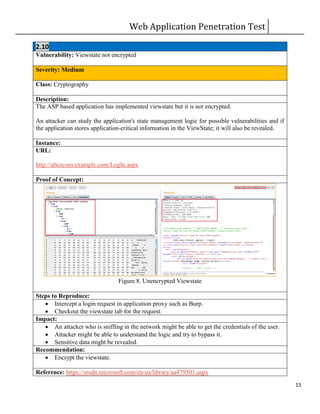
Web Pentest Sample Report Pdf The security headers are displayed in the http response and indicate the way the browser is suppose to operate in regards to the execution of the html. they are checked before the rest of the. This brute force attack uncovered a password of “nanotechnology1” for the admin user. we were able to leverage these credentials to successfully gain unauthorized access to the protected portion of the website (figure 6). please see appendix a for more information on the exploited vulnerability. The application’s use of cryptographically signed session cookies prevented tampering, and direct use of the cookie in the attacker’s browser failed, likely due to server side validation checks (e.g., ip address or user agent binding). therefore, it was necessary to steal a live session cookie from a legitimate, active admin ses sion. Using an open redirect vulnerability, it is possible to steal the application user's sensitive cookie. specifically, the access token and id token cookies. these two cookies will allow an attacker to interact with the application's graphql scheme as the victim. the following http request was observed while interacting with the application:.

Pentest Report Pdf Http Cookie Transport Layer Security The application’s use of cryptographically signed session cookies prevented tampering, and direct use of the cookie in the attacker’s browser failed, likely due to server side validation checks (e.g., ip address or user agent binding). therefore, it was necessary to steal a live session cookie from a legitimate, active admin ses sion. Using an open redirect vulnerability, it is possible to steal the application user's sensitive cookie. specifically, the access token and id token cookies. these two cookies will allow an attacker to interact with the application's graphql scheme as the victim. the following http request was observed while interacting with the application:.

Cookie Pdf Http Cookie
Comments are closed.