Pdf Zero Trust Network Security Model

Zero Trust Cyber Security Model Pdf Security Computer Security The zero trust security model has become a new way of thinking about cybersecurity that challenges old ways of thinking about security that are built on perimeters. Zero trust provides a collection of concepts and ideas designed to minimize uncertainty in enforcing accurate, least privilege per request access decisions in information systems and services in the face of a network viewed as compromised.

Embracing A Zero Trust Security Model Pdf Computer Security Security This research paper offers a comprehensive overview of zero trust security models, exploring their historical context, fundamental principles, implementation strategies, and real world applications. Within this piece, we look at how to use zero trust security models and how well they work in real life situations. the goal is to show the pros and cons of implementing zero trust and how it affects safety by looking at case studies and real world tests. Zero trust fundamentals; what is a zero trust network?;. But today, as data footprints have expanded to sit off premises in the cloud, or across hybrid networks, the zero trust security model has evolved to address a more holistic set of attack vectors.

What Is Zero Trust Ultimate Guide To The Network Security Model Pdf Zero trust fundamentals; what is a zero trust network?;. But today, as data footprints have expanded to sit off premises in the cloud, or across hybrid networks, the zero trust security model has evolved to address a more holistic set of attack vectors. This insightful guide introduces the zero trust model, advocating for the treatment of all hosts as potential threats and recognizing the entire network as vulnerable. It explains the key pillars of zero trust security while also covering the zero trust frameworks developed by nist, dod, cisa, and other organizations, making it a valuable resource for anyone seeking to understand how to implement the zero trust security model. This document contains an abstract definition of zero trust architecture (zta) and gives general deployment models and use cases where zero trust could improve an enterprise’s overall information technology security posture. We look at zero trust as a comprehensive and transformative model that replaces implicit trust with explicit and continuous monitoring and verification based on the risk factors and the threat landscape, regardless of user location or used device.

Zero Trust Security Models Overview Pdf This insightful guide introduces the zero trust model, advocating for the treatment of all hosts as potential threats and recognizing the entire network as vulnerable. It explains the key pillars of zero trust security while also covering the zero trust frameworks developed by nist, dod, cisa, and other organizations, making it a valuable resource for anyone seeking to understand how to implement the zero trust security model. This document contains an abstract definition of zero trust architecture (zta) and gives general deployment models and use cases where zero trust could improve an enterprise’s overall information technology security posture. We look at zero trust as a comprehensive and transformative model that replaces implicit trust with explicit and continuous monitoring and verification based on the risk factors and the threat landscape, regardless of user location or used device.
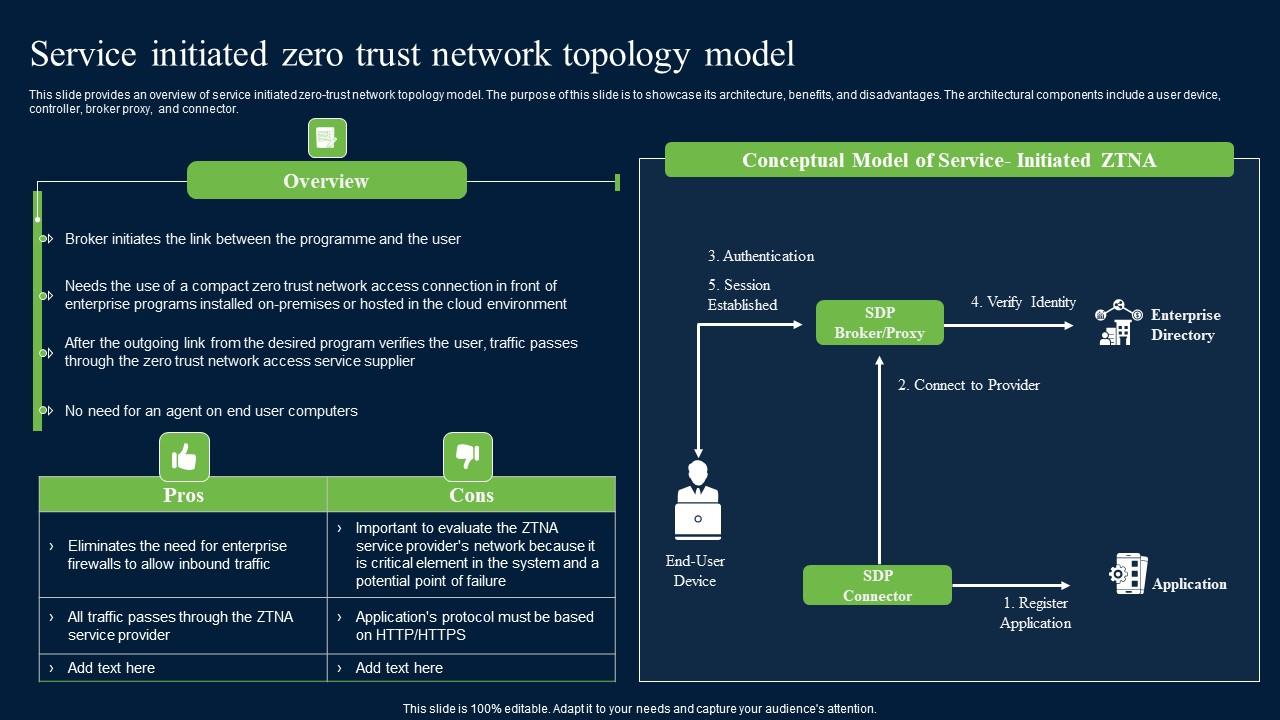
Service Initiated Zero Trust Network Topology Model Zero Trust Network Secu This document contains an abstract definition of zero trust architecture (zta) and gives general deployment models and use cases where zero trust could improve an enterprise’s overall information technology security posture. We look at zero trust as a comprehensive and transformative model that replaces implicit trust with explicit and continuous monitoring and verification based on the risk factors and the threat landscape, regardless of user location or used device.
Comments are closed.