Pdf Wireless Sensor Network Security Visualization
Wireless Sensor Network Security Studycase 1 Pdf Wireless Sensor In this paper, we explore the issues and concerns surrounding the application of visual analysis for wireless sensor network security purposes. Prior to analyzing the features the visual analytics domain brings to network security, we schematize the architecture of a generic wireless sensor network security visualization system (see fig. 2).
Wireless Sensor Network Visualization At Jason Rocha Blog In this paper, we explore the issues and concerns surrounding the application of visual analysis for wireless sensor network security purposes. this paper focuses on several distinct advantages information visualization and visual analytics can offer in the security domain. In this paper, we explore the issues and concerns surrounding the application of visual analysis for wireless sensor network security purposes. this paper focuses on several distinct advantages information visualization and visual analytics can offer in the security domain. Wireless sensor networks (wsns) face significant security vulnerabilities due to resource constraints and dense deployments. the analysis categorizes attacks such as denial of service, sybil, and sinkhole, impacting network integrity. Security concepts of wsns. b. basic characteristics in this subsection, we will cover an overview of the essential characteristics required to ensure the security in wsns, which include: data integrity: data integrity aims to ensure that all the original data attributes generated in the sensing node are maintained during the routing to t.

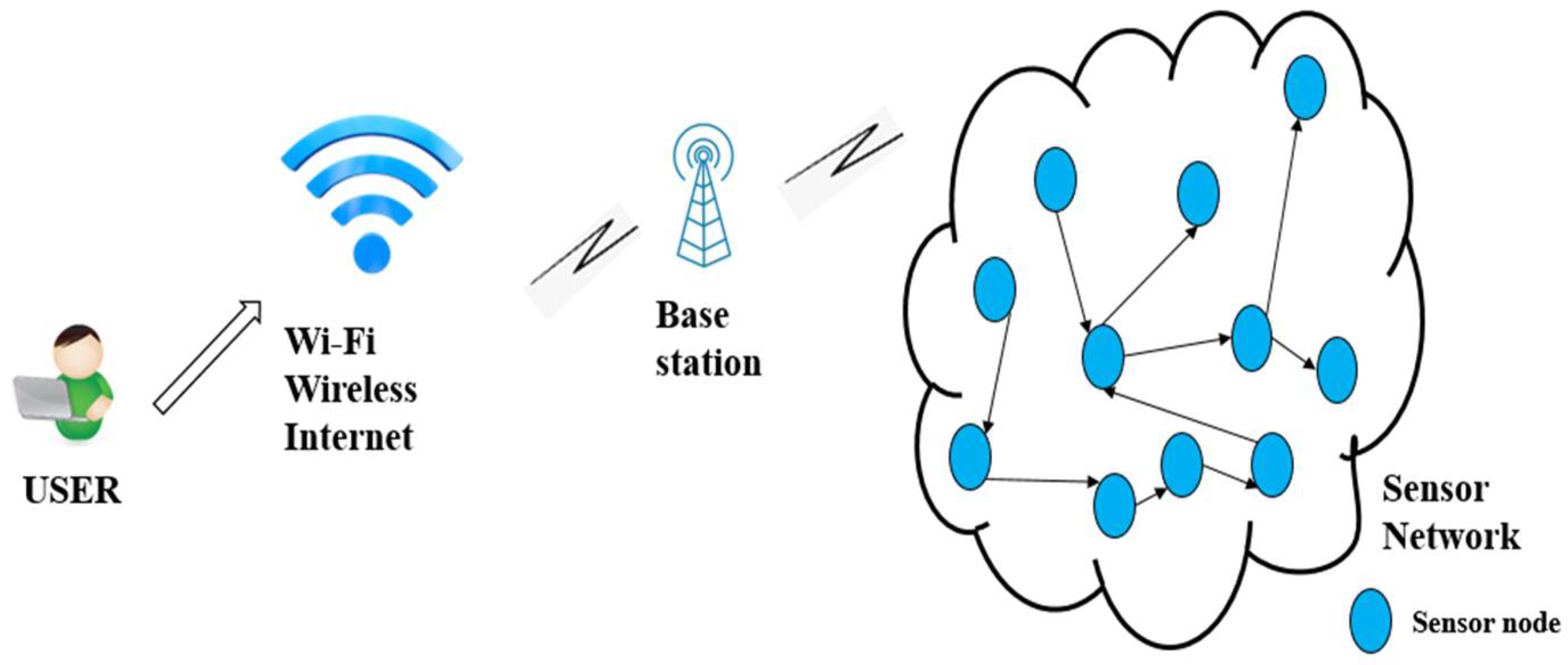
Pdf The Integration Analysis And Visualization Of Sensor Data From Wireless sensor networks (wsns) face significant security vulnerabilities due to resource constraints and dense deployments. the analysis categorizes attacks such as denial of service, sybil, and sinkhole, impacting network integrity. Security concepts of wsns. b. basic characteristics in this subsection, we will cover an overview of the essential characteristics required to ensure the security in wsns, which include: data integrity: data integrity aims to ensure that all the original data attributes generated in the sensing node are maintained during the routing to t. Sensor networks refer to a heterogeneous system combining tiny sensors and actuators with general purpose computing elements. these networks will consist of hundreds or thousands of self organizing, low power, low cost wireless nodes deployed to monitor and affect the environment [1]. The wsn ds dataset for wireless sensor networks (wsn) includes attributes of nodes and labels identifying denial of service (dos) attacks like blackhole, scheduling, grayhole, flooding, and normal behavior. In conclusion, this study presents an intrusion prevention architecture tailored for wireless sensor networks (wsns), aiming to ensure secure routing in mobile internet of things (iot) networks. In fig.1, we present a wsn architecture consisting of sensors. each node acts as a router and as a user terminal at the same time. it receives data transmitted by the other nodes and transmits the queued information to a given destination. all sensors of wsn send data to the base station.

Xai For Wireless Sensor Network Security Pdf Wireless Sensor Sensor networks refer to a heterogeneous system combining tiny sensors and actuators with general purpose computing elements. these networks will consist of hundreds or thousands of self organizing, low power, low cost wireless nodes deployed to monitor and affect the environment [1]. The wsn ds dataset for wireless sensor networks (wsn) includes attributes of nodes and labels identifying denial of service (dos) attacks like blackhole, scheduling, grayhole, flooding, and normal behavior. In conclusion, this study presents an intrusion prevention architecture tailored for wireless sensor networks (wsns), aiming to ensure secure routing in mobile internet of things (iot) networks. In fig.1, we present a wsn architecture consisting of sensors. each node acts as a router and as a user terminal at the same time. it receives data transmitted by the other nodes and transmits the queued information to a given destination. all sensors of wsn send data to the base station.
Comments are closed.