Pdf Vulnerability Assessment Methods In Cloud Computing

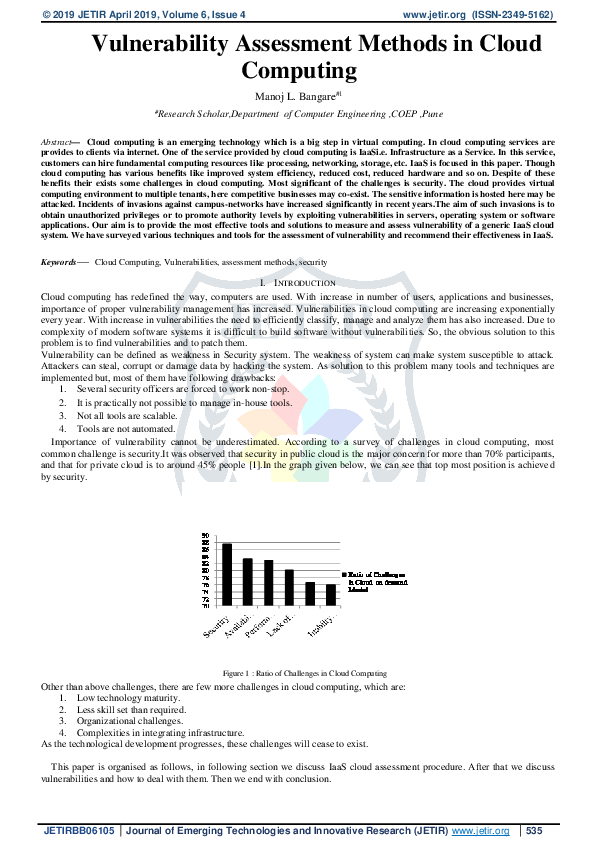
Vulnerability Assessment Methods Pdf Vulnerability Risk Our aim is to provide the most effective tools and solutions to measure and assess vulnerability of a generic iaas cloud system. Our aim is to provide the most effective tools and solutions to measure and assess vulnerability of a generic iaas cloud system. we have surveyed various techniques and tools for the assessment of vulnerability and recommend their effectiveness in iaas.

Vulnerability Assessment Pdf Vulnerability Computing Threat Our aim is to provide the most effective tools and solutions to measure and assess vulnerability of a generic iaas cloud system. we have surveyed various techniques and tools for the assessment of vulnerability and recommend their effectiveness in iaas. To achieve a dynamic vulnerability assessment for cloud computing, we propose three modules such as: system classifiers, indexer, and vulnerability class index. Module 4 cloud security free download as pdf file (.pdf), text file (.txt) or view presentation slides online. As more and more users, applications and businesses move to cloud it becomes very important to have proper vulnerability management in cloud. in this paper we present a vulnerability management framework for cloud computing.

Vulnerability Assessment Pdf Module 4 cloud security free download as pdf file (.pdf), text file (.txt) or view presentation slides online. As more and more users, applications and businesses move to cloud it becomes very important to have proper vulnerability management in cloud. in this paper we present a vulnerability management framework for cloud computing. Our aim is to provide the most effective tools and solutions to measure and assess vulnerability of a generic iaas cloud system. we have surveyed various techniques and tools for the assessment of vulnerability and recommend their effectiveness in iaas. The major role of proposed assessment framework is to generate or produce the compact vulnerability assessment report for the cloud system. for reach ing out to the desired output, several components and modules have been devised. Vulnerability assessment and penetration testing (vapt) is a critical methodology for identifying, evaluating, and mitigating security risks in cloud hosted web applications. The main objective of this study is to conduct a comprehensive analysis of cyber risks in cloud computing, including classifying threats, vulnerabilities, impacts, and countermeasures.
Pdf Vulnerability Assessment Methods In Cloud Computing Our aim is to provide the most effective tools and solutions to measure and assess vulnerability of a generic iaas cloud system. we have surveyed various techniques and tools for the assessment of vulnerability and recommend their effectiveness in iaas. The major role of proposed assessment framework is to generate or produce the compact vulnerability assessment report for the cloud system. for reach ing out to the desired output, several components and modules have been devised. Vulnerability assessment and penetration testing (vapt) is a critical methodology for identifying, evaluating, and mitigating security risks in cloud hosted web applications. The main objective of this study is to conduct a comprehensive analysis of cyber risks in cloud computing, including classifying threats, vulnerabilities, impacts, and countermeasures.
Comments are closed.