Pdf Visual Cryptography For Image Privacy Protection Using Diverse

Pdf Visual Cryptography For Image Privacy Protection Using Diverse Steganography, watermarking, or visual cryptography is a tool for securing data communication using images or visual objects. some combined models use these techniques, as well as some traditional cryptographic algorithms, to strengthen the security and privacy of information. The proposed system is used to maintain privacy of images by creating shares of the image using visual cryptography and securely storing the shares in different databases in the form of qr code.

Pdf A Copyright Protection Scheme For Digital Images Using Visual This work explores the possibility of using visual cryptography for imparting privacy to biometric data such as fingerprint images, iris codes, and face images. Visual cryptography for image privacy protection using diverse image mediamodhe nishigandha p, pawar priti d, sawant vaibhav l, prof. sinare p.dbe. student, dept. of computer engineering s.c.s.o.e, rahuri factory, maharashtra, indiaasst. In extended visual cryptography (evc), the share images are constructed to contain meaningful cover images, thereby providing opportunities for integrating visual cryptography and biometric security techniques. we use the concept of visual cryptography in order to provide security for the images. Diverse visual cryptography schemes were developed based on different factors like pixel expansion, meaningless or meaningful shares, contrast, security, type of secret image (either binary or colour) and the number of secret images encrypted.

Pdf Protecting Documents Using Visual Cryptography In extended visual cryptography (evc), the share images are constructed to contain meaningful cover images, thereby providing opportunities for integrating visual cryptography and biometric security techniques. we use the concept of visual cryptography in order to provide security for the images. Diverse visual cryptography schemes were developed based on different factors like pixel expansion, meaningless or meaningful shares, contrast, security, type of secret image (either binary or colour) and the number of secret images encrypted. Abstract visual cryptography is a powerful method for securely sharing and protecting visual data by splitting an im age into multiple shares. individual shares do not re veal any information, but when combined, they allow for the reconstruction of the original image. Explore the visual cryptography to preserve the privacy of biometric data by decomposing original image into two images in such a way that the original image can be revealed only when both images are simultaneously available. The proposed system is used to maintain privacy of images by creating shares of the image using visual cryptography and securely storing the shares in different databases in the form of qr code. By combing neural networks and variant visual secret sharing, the quality of the reconstructed secret image and disguise images are visually the same as the original images.
Pdf Visual Cryptography Using Kn Sharing Algorithm For Colour Images Abstract visual cryptography is a powerful method for securely sharing and protecting visual data by splitting an im age into multiple shares. individual shares do not re veal any information, but when combined, they allow for the reconstruction of the original image. Explore the visual cryptography to preserve the privacy of biometric data by decomposing original image into two images in such a way that the original image can be revealed only when both images are simultaneously available. The proposed system is used to maintain privacy of images by creating shares of the image using visual cryptography and securely storing the shares in different databases in the form of qr code. By combing neural networks and variant visual secret sharing, the quality of the reconstructed secret image and disguise images are visually the same as the original images.

Pdf Enhanced Watermarking Technique For Color Images Using Visual The proposed system is used to maintain privacy of images by creating shares of the image using visual cryptography and securely storing the shares in different databases in the form of qr code. By combing neural networks and variant visual secret sharing, the quality of the reconstructed secret image and disguise images are visually the same as the original images.
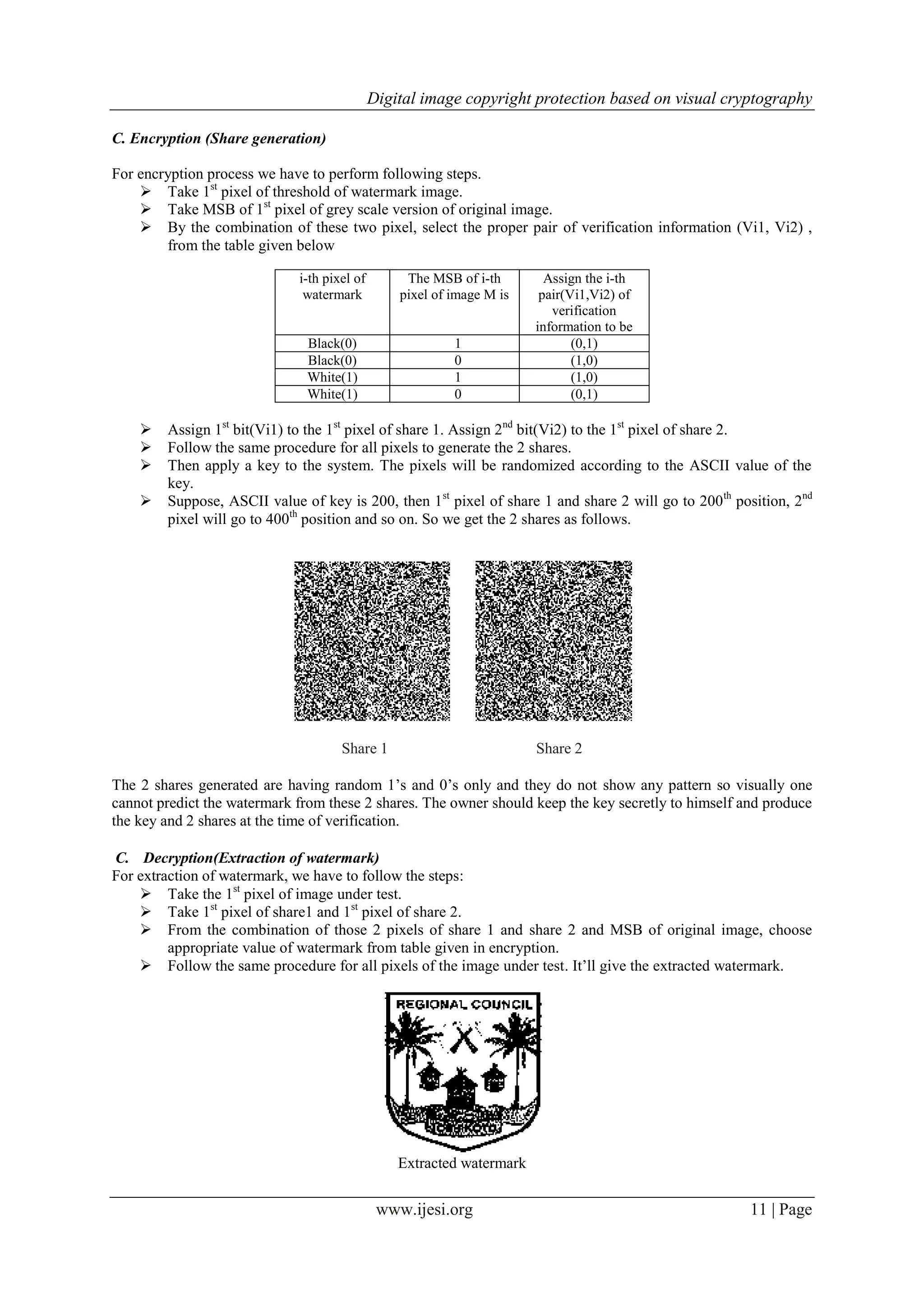
Digital Image Copyright Protection Based On Visual Cryptography Pdf
Comments are closed.