Pdf Threat Modelling Tools Analysis 101

Threat Modelling Pdf Threat Computer Vulnerability Computing Threat modeling can be used as part of security risk analysis to systematically iterate over possible threat scenarios. the motivation for this research came from the constantly growing need. What is threat modeling? "threat modeling is the process of using hypothetical scenarios, system diagrams, and testing to help secure systems and data." [1].

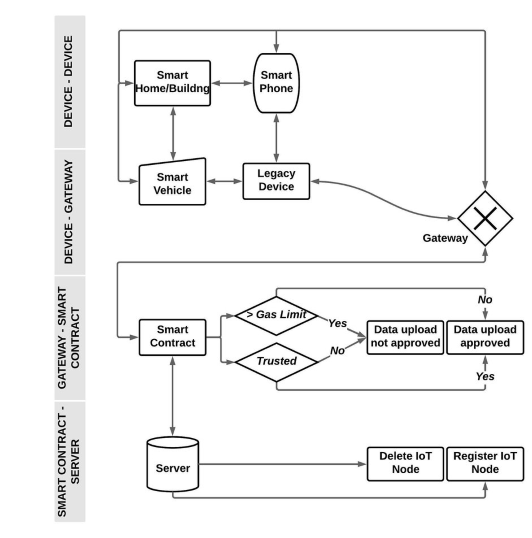
Threat Modeling 101 Png How can a change in software result in either or fewer threats? identify external dependencies – os, web server, network, define security assumptions – what can you expect with regard to security; will the db encrypt columns? is there a key manager? what are the limitations you are working with. Threat modeling is the process of finding threats to a system, evaluating the risk associated with each threat, selecting mitigations to counteract each threat. In this paper, we propose a set of criteria for evaluating threat modeling tools. we conceptu ally classify current threat modeling tools, and discuss their properties and design implications. Threat modelling is a form of risk assessment that models aspects of the attack and defence sides of a particular logical entity, such as a piece of data, an application, a host, a system, or an environment.

Threat Modelling Methodology And Process 1 Pdf Security Computer In this paper, we propose a set of criteria for evaluating threat modeling tools. we conceptu ally classify current threat modeling tools, and discuss their properties and design implications. Threat modelling is a form of risk assessment that models aspects of the attack and defence sides of a particular logical entity, such as a piece of data, an application, a host, a system, or an environment. Sequently revised in feb 2021). the document provided guidance to critical information infrastructure owners (ciios) on performing a proper cybersecurity risk assessment, and briefly covered steps for threat modelling. Threat modeling can be used as part of security risk analysis to systematically iterate over possible threat scenarios. the motivation for this research came from the constantly growing need. Abstract this paper presents a comprehensive guide to implementing threat modeling in cybersecurity. threat modeling involves identifying, analyzing, and assessing potential threats to a computer system, network, or organization's digital assets. The analysis offers insights into both operational and design time threat modeling, emphasizing the importance of understanding threats, their vectors, and methods of mitigation to enhance security postures.
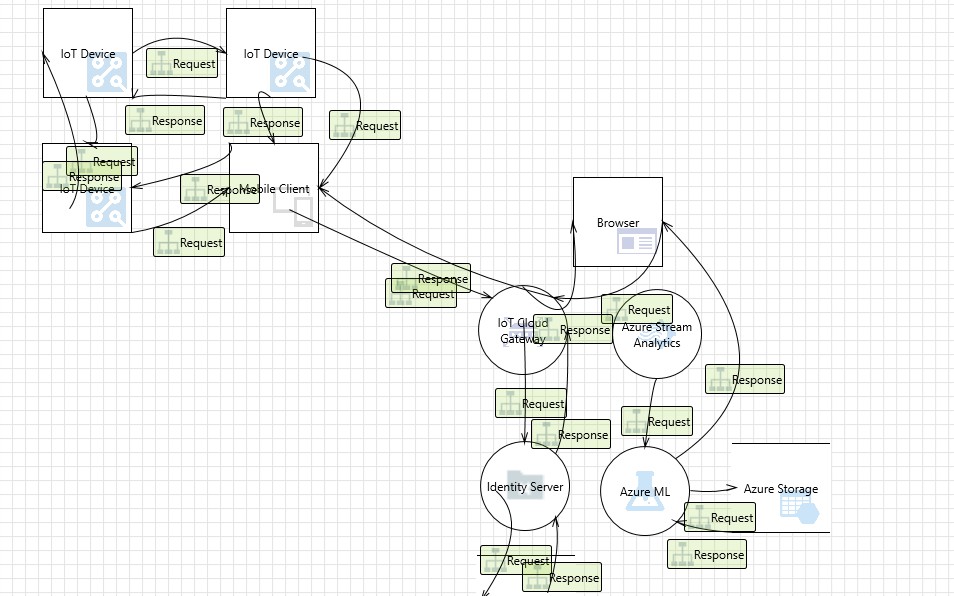
Threat Modelling Tools Analysis 101 Dzone Sequently revised in feb 2021). the document provided guidance to critical information infrastructure owners (ciios) on performing a proper cybersecurity risk assessment, and briefly covered steps for threat modelling. Threat modeling can be used as part of security risk analysis to systematically iterate over possible threat scenarios. the motivation for this research came from the constantly growing need. Abstract this paper presents a comprehensive guide to implementing threat modeling in cybersecurity. threat modeling involves identifying, analyzing, and assessing potential threats to a computer system, network, or organization's digital assets. The analysis offers insights into both operational and design time threat modeling, emphasizing the importance of understanding threats, their vectors, and methods of mitigation to enhance security postures.

Strike Threat Modeling 101 Pdf Abstract this paper presents a comprehensive guide to implementing threat modeling in cybersecurity. threat modeling involves identifying, analyzing, and assessing potential threats to a computer system, network, or organization's digital assets. The analysis offers insights into both operational and design time threat modeling, emphasizing the importance of understanding threats, their vectors, and methods of mitigation to enhance security postures.
Threat Modelling Tools Analysis 101
Comments are closed.