Pdf Texture Based Malware Family Classification
Malware Classification Based On Image Segmentation Motivated by the visual similarities of malware, this paper presents the malware family classification using some texture based features. Malware is one of the major threats on internet whose count is increasing rapidly every year in millions. most of the time similar malware files are modified fo.

A Malware Classification Method Based On Three Channel Visualization Abstract luster malware into families, based on different fea tures derived from dynamic review of the malware. while these approaches demonstrate promise, they are themselves su. This paper presents the malware family classification using some texture based features of hog, lbp, and gist as feature descriptor for svm classifier, and shows better results than existing malware classification approaches. The goal of this paper is to evaluate state of the art texture analysis techniques for malware classi cation in a real life, larger dataset, as well as to validate the claim of resilience against ob fuscation. Malware binaries are visualized as gray scale images, with the observation that for many malware families, the images belonging to the same family appear very similar in layout and texture. motivated by this visual similarity, a classification method using standard image features is proposed.

Pdf Texture Based Malware Family Classification The goal of this paper is to evaluate state of the art texture analysis techniques for malware classi cation in a real life, larger dataset, as well as to validate the claim of resilience against ob fuscation. Malware binaries are visualized as gray scale images, with the observation that for many malware families, the images belonging to the same family appear very similar in layout and texture. motivated by this visual similarity, a classification method using standard image features is proposed. Ork proposes a malware classification method using call graph instruction based rgb image model. training various well known cnn architectures on a multitude of image variations. Here we introduce a new semi supervised method, named malwaredna, that unifies the capability of malware detection and malware family classification into a single framework, while also addressing the shortcomings of novel malware family identification. Leveraging advanced neural network architectures like xception, it analyzes structural patterns in malware images to accurately identify and classify malware families. Through code mapping, texture partitioning, and texture extracting, we can study malware classification in a new feature space of image texture representation without decryption and disassembly.
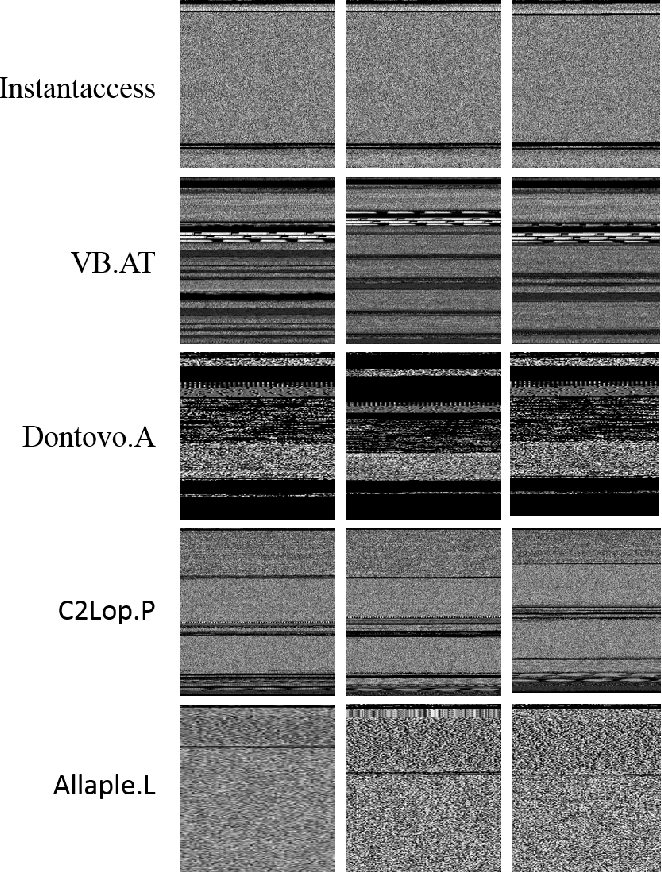
Figure 2 From Texture Based Malware Family Classification Semantic Ork proposes a malware classification method using call graph instruction based rgb image model. training various well known cnn architectures on a multitude of image variations. Here we introduce a new semi supervised method, named malwaredna, that unifies the capability of malware detection and malware family classification into a single framework, while also addressing the shortcomings of novel malware family identification. Leveraging advanced neural network architectures like xception, it analyzes structural patterns in malware images to accurately identify and classify malware families. Through code mapping, texture partitioning, and texture extracting, we can study malware classification in a new feature space of image texture representation without decryption and disassembly.
Steps For Malware Texture Classification Download Scientific Diagram Leveraging advanced neural network architectures like xception, it analyzes structural patterns in malware images to accurately identify and classify malware families. Through code mapping, texture partitioning, and texture extracting, we can study malware classification in a new feature space of image texture representation without decryption and disassembly.
Comments are closed.