Pdf Side Channel Attack
Mitigating A Token Length Side Channel Attack In Our Ai Products In this paper we have evaluated the current memory level side channel attacks and countermeasures, mainly focusing on the timing attacks against cloud and embedded frameworks available in the. In this lecture, we will explore the history, examples, and countermeasures of side channel attacks. in 1945, at the end of world war ii, the soviet union gave a great seal as a gift to a us ambassador. this seal was placed in the ambassador's residence, and it contained a passive listening device.
Mitigating A Token Length Side Channel Attack In Our Ai Products Abstract side channel attacks are easy to implement whilst powerful attacks against cryptographic implementations, and their targets range from primitives, protocols, modules, and devices to even systems. these attacks pose a serious threat to the security of cryptographic modules. First introduced by kocher, these types of attacks are referred to as side channel attacks (scas). these attacks pose a very serious threat to embedded systems with cryptographic algorithms. Outline what are side channel attacks (scas)? which adversary models are suitable for scas? which types of attacks exists? how do these attacks work precisely?. Spectre and meltdown carry out cache attacks against speculatively loaded data so that an unprivileged attacker process can read kernel memory, break aslr, etc.
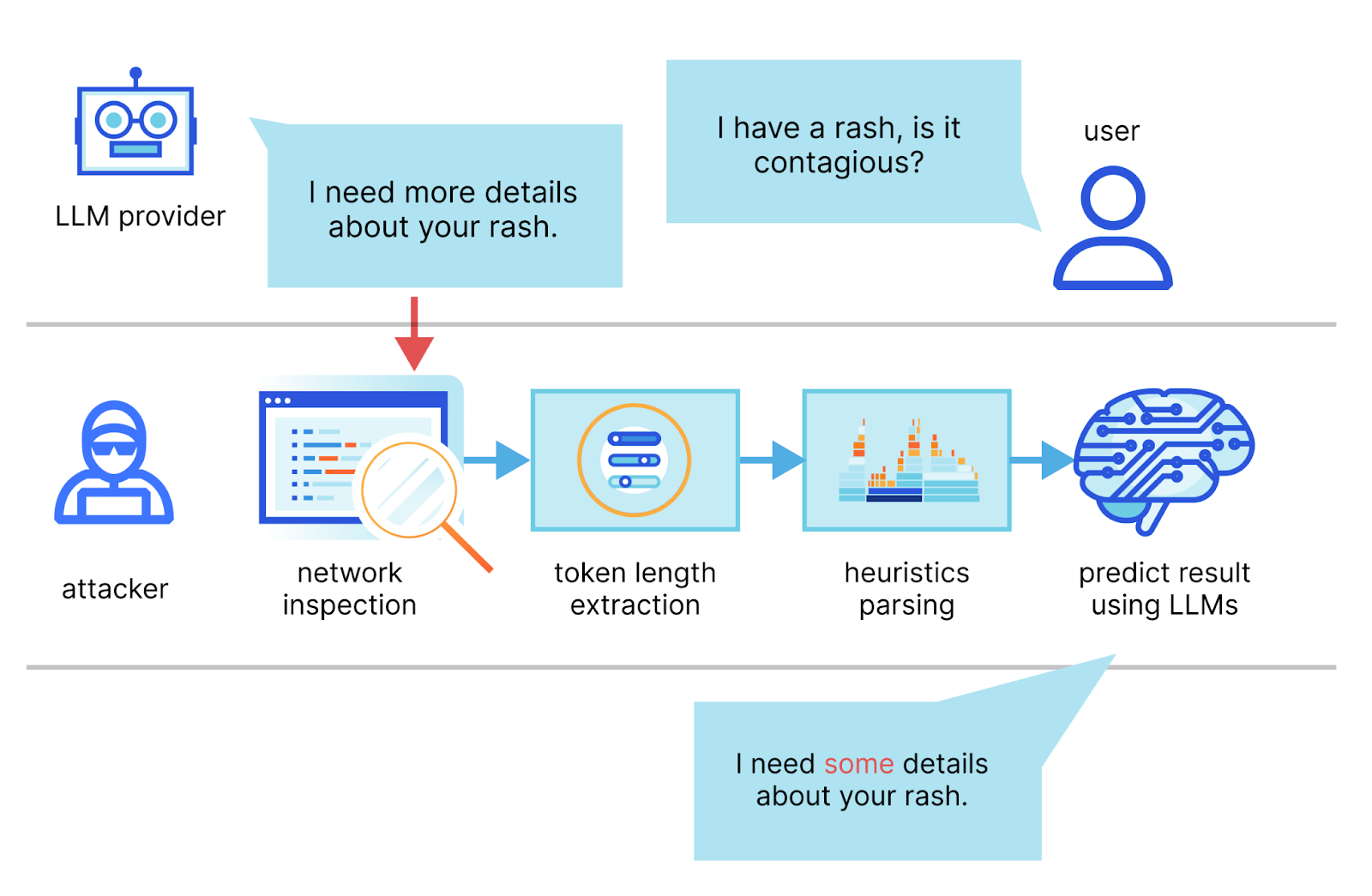
Mitigating A Token Length Side Channel Attack In Our Ai Products Outline what are side channel attacks (scas)? which adversary models are suitable for scas? which types of attacks exists? how do these attacks work precisely?. Spectre and meltdown carry out cache attacks against speculatively loaded data so that an unprivileged attacker process can read kernel memory, break aslr, etc. We introduce usual protections, and show their limits, both by discussing the most powerful attack or by showing evaluation methods. the material of this talk consists in a formalization work carried out by the co authors of this talk. In cryptography, a side channel attack is an attack based on information gained from the physical implementation of a cryptosystem, rather than brute force or theoretical weaknesses in the algorithms (compare cryptanalysis). We provide a brief, accessible introduction to side channel attacks, a grow ing subarea of computer security. we explain the key underlying ideas, give. a chronological overview of selected classical attacks, and characterize side channel attacks along several axes. An optical projection side channel paradigm that confronts two core instabilities, which achieves fidelity beyond competing neural approaches while retaining resilience to illumination perturbations is introduced. noncontact exfiltration of electronic screen content poses a security challenge, with side channel incursions as the principal vector. we introduce an optical projection side channel.

Mitigating A Token Length Side Channel Attack In Our Ai Products We introduce usual protections, and show their limits, both by discussing the most powerful attack or by showing evaluation methods. the material of this talk consists in a formalization work carried out by the co authors of this talk. In cryptography, a side channel attack is an attack based on information gained from the physical implementation of a cryptosystem, rather than brute force or theoretical weaknesses in the algorithms (compare cryptanalysis). We provide a brief, accessible introduction to side channel attacks, a grow ing subarea of computer security. we explain the key underlying ideas, give. a chronological overview of selected classical attacks, and characterize side channel attacks along several axes. An optical projection side channel paradigm that confronts two core instabilities, which achieves fidelity beyond competing neural approaches while retaining resilience to illumination perturbations is introduced. noncontact exfiltration of electronic screen content poses a security challenge, with side channel incursions as the principal vector. we introduce an optical projection side channel.
Comments are closed.