Pdf Securing The Data In The Cloud Using Two Fish Algorithm

Pdf Securing The Data In The Cloud Using Two Fish Algorithm The arrangement in this paper exploits encryption of information to be transferred to cloud utilizing two fish algorithm. So this paper introduces an answer in which security is centered on ensuring the client information paying little mind to the cloud specialist co op that holds it. the arrangement in this paper exploits encryption of information to be transferred to cloud utilizing two fish algorithm.

Implementation Of Two Fish Algorithm Download Scientific Diagram There are many encryption algorithms to provide confidentiality for our data over cloud. in this paper, we propose twofish encryption algorithm, which protects the privacy of individual data. N opts for cloud storage to make data storage and retrieval easier, simple and more secure. the proposed model stores patients report in a cloud database by implementing two fish alg rithm, a block cipher for storing data by encryption and retrieving the same by decryption. the symmetric encryption algorithm two fish is. Hybrid cryptography using ecc and twofish enhances cloud data security significantly. the proposed model integrates symmetric and asymmetric encryption for efficient data protection. ecc offers comparable security with smaller key sizes than rsa, enhancing performance. The arrangement in this paper exploits encryption of information to be transferred to cloud utilizing two fish algorithm.
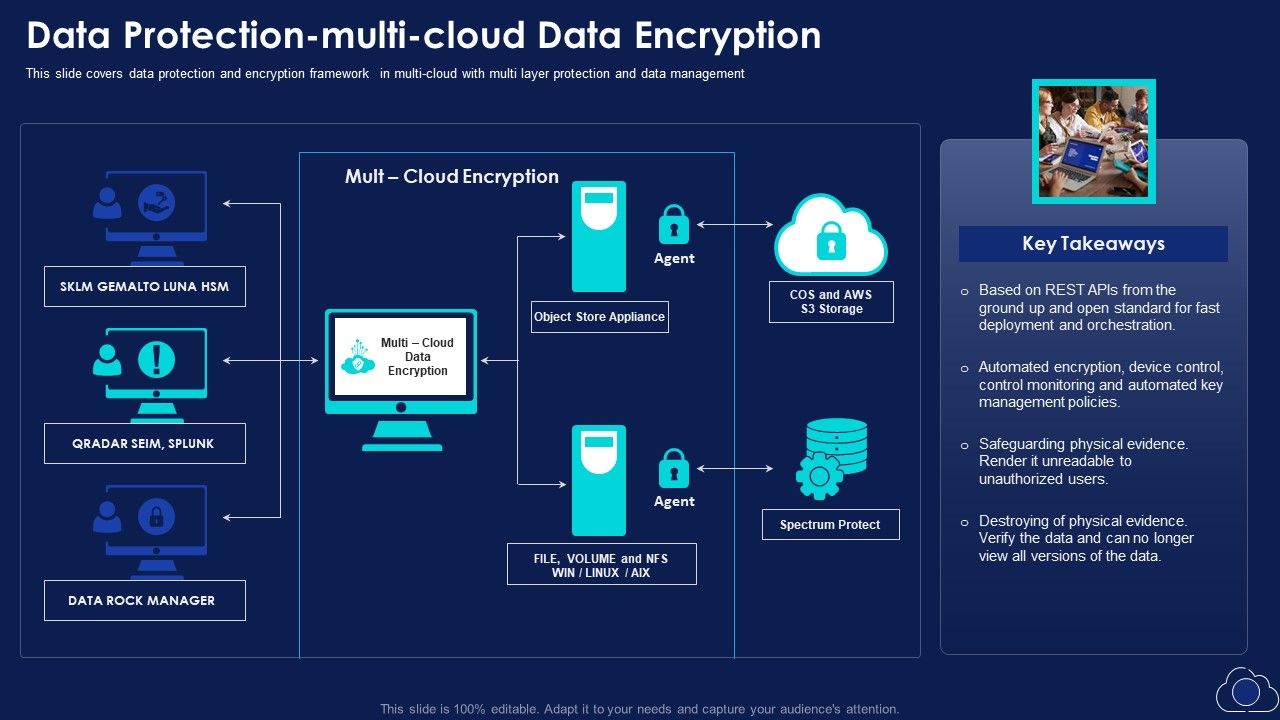
Data Protection Multi Cloud Data Encryption Introduction Pdf Hybrid cryptography using ecc and twofish enhances cloud data security significantly. the proposed model integrates symmetric and asymmetric encryption for efficient data protection. ecc offers comparable security with smaller key sizes than rsa, enhancing performance. The arrangement in this paper exploits encryption of information to be transferred to cloud utilizing two fish algorithm. So this paper introduces an answer in which security is centered on ensuring the client information paying little mind to the cloud specialist co op that holds it. the arrangement in this paper exploits encryption of information to be transferred to cloud utilizing two fish algorithm. Fish algorithm endeavors to affirm customer and to scramble data in the cloud. this prop sed plot contains 2 stages which are key era stage and data transmission stage. to address these. To resolve this, we are successful to present a fresh hybrid method to attain extraordinary data safety and privacy. in this paper, we are examining rsa and twofish to appliance a hybrid procedure. Storing of encrypted data and retrieving of decrypted data is done by implementing two fish algorithms [50]. transaction bodies in medical block chain are pati nts, clinical institutions and third party participants like public users, insurance companies, researchers. medical records are generated in the medical institutions.

Pdf Efficient Iot Based Cloud Computing Framework For Secure Data So this paper introduces an answer in which security is centered on ensuring the client information paying little mind to the cloud specialist co op that holds it. the arrangement in this paper exploits encryption of information to be transferred to cloud utilizing two fish algorithm. Fish algorithm endeavors to affirm customer and to scramble data in the cloud. this prop sed plot contains 2 stages which are key era stage and data transmission stage. to address these. To resolve this, we are successful to present a fresh hybrid method to attain extraordinary data safety and privacy. in this paper, we are examining rsa and twofish to appliance a hybrid procedure. Storing of encrypted data and retrieving of decrypted data is done by implementing two fish algorithms [50]. transaction bodies in medical block chain are pati nts, clinical institutions and third party participants like public users, insurance companies, researchers. medical records are generated in the medical institutions.
Comments are closed.