Pdf Secure Bootloader Design Using Post Quantum Cryptography

High Speed Design Of Post Quantum Cryptography With Optimized Hashing This paper presents the design and implementation of a secure bootloader leveraging post quantum cryptographic (pqc) algorithms to ensure the integrity and authenticity of firmware. Background as an operating system. the computing device may initiate execu tion of the operating system using a bootloader that performs various security measures (e.g., cryptography) to ensure that stages of the bootloader have not been tampered.

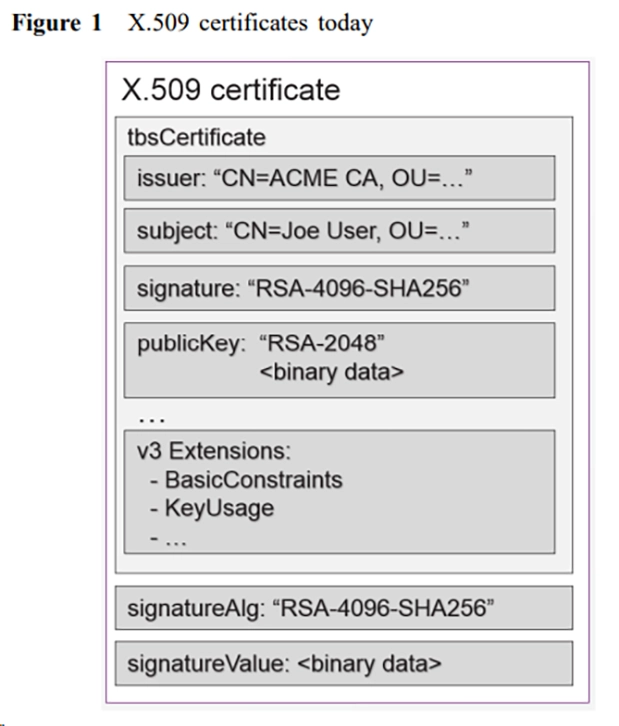
Post Quantum Cryptography Pdf Dirzon Fig. 1 is a block diagram illustrating an example computing device configured to implement secure boot using post quantum cryptography in accordance with one or more aspects of the. Our proposed implementation aims to achieve secure bootloader functionality without relying on proprietary security extensions. Post quantum secure boot july 2024 free download as pdf file (.pdf), text file (.txt) or read online for free. In this section, we discuss the existing literature on post quantum certificate generation, and implementation of post quantum signature schemes in secure boot applications.

Pdf Secure Bootloader Design Using Post Quantum Cryptography Post quantum secure boot july 2024 free download as pdf file (.pdf), text file (.txt) or read online for free. In this section, we discuss the existing literature on post quantum certificate generation, and implementation of post quantum signature schemes in secure boot applications. This paper presents the first post quantum secure boot solution, implemented fully as hardware for reasons of security and performance. in particular, this work uses the extended merkle signature scheme (xmss), a hash based scheme that has been specified as an ietf rfc. For that reason, migration towards post quantum cryptography (pqc) is necessary. this paper investigates the practical impact of migrating the secure boot flow on a vehicle network processor (s32g274a) towards pqc. To enable secure boot (a contemporary view) use established cryptographic algorithms. adopt new quantum threat mitigation schemes. deploy hybrid cryptographic protection! use verified, validated implementations of ip cores. go for hardware based solution. While there are many considerations for transitioning from classical cryptographic algorithms to pqc algorithms, this paper offers initial insights into which pqc algorithms may be useful for secure boot in automotive real time systems.
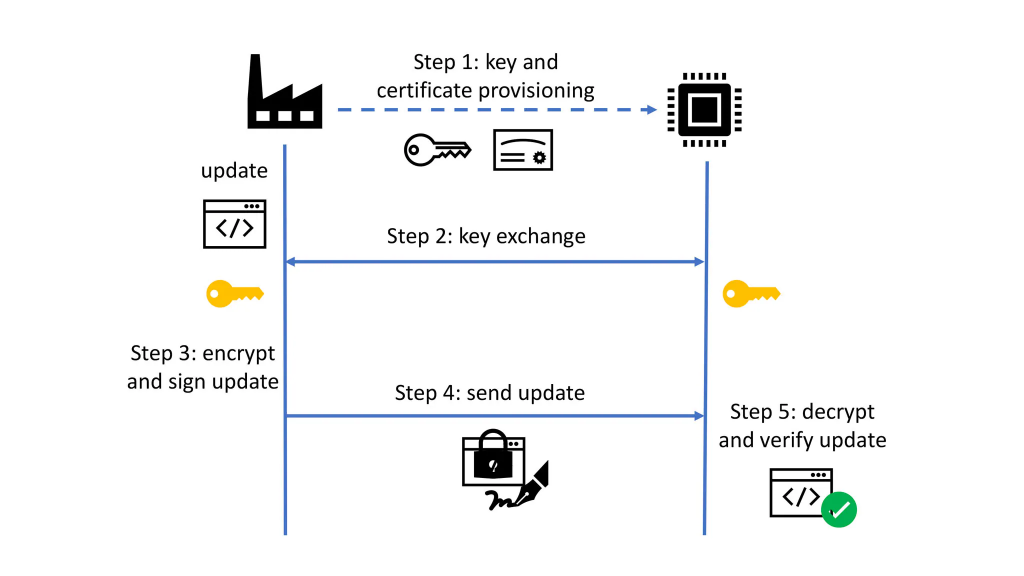
Quantum Cryptography Vs Post Quantum Cryptography Major Difference This paper presents the first post quantum secure boot solution, implemented fully as hardware for reasons of security and performance. in particular, this work uses the extended merkle signature scheme (xmss), a hash based scheme that has been specified as an ietf rfc. For that reason, migration towards post quantum cryptography (pqc) is necessary. this paper investigates the practical impact of migrating the secure boot flow on a vehicle network processor (s32g274a) towards pqc. To enable secure boot (a contemporary view) use established cryptographic algorithms. adopt new quantum threat mitigation schemes. deploy hybrid cryptographic protection! use verified, validated implementations of ip cores. go for hardware based solution. While there are many considerations for transitioning from classical cryptographic algorithms to pqc algorithms, this paper offers initial insights into which pqc algorithms may be useful for secure boot in automotive real time systems.

Post Quantum Cryptography Pqc To enable secure boot (a contemporary view) use established cryptographic algorithms. adopt new quantum threat mitigation schemes. deploy hybrid cryptographic protection! use verified, validated implementations of ip cores. go for hardware based solution. While there are many considerations for transitioning from classical cryptographic algorithms to pqc algorithms, this paper offers initial insights into which pqc algorithms may be useful for secure boot in automotive real time systems.
Primer On Post Quantum Cryptography Pqc Halock
Comments are closed.