Pdf Secure Api Design Principles
Secure Api Design Principles This paper examines the key principles of secure api design, discusses best practices, and presents case studies of successful implementations. the paper also addresses common challenges, potential pitfalls, and future trends in api security. This paper examines the key principles of secure api design, discusses best practices, and presents case studies of successful implementations. the paper also addresses common challenges, potential pitfalls, and future trends in api security.

Api Security Fundamentals Pdf Computer Security Security This project adopted a systematic, design oriented methodology to develop and evaluate secure api design and authentication strategies for distributed microservices systems. These help your api developers design to code quality and security standards, integrate testing mechanisms into your development pipelines, and make sure that your apis have up to date documentation. These holes are not always due to negligence. developing secure apis isn’t as simple as it might seem, as the api provider must often strike a balance between ease of use and security. The foundational ideas of apis, their vital role in the digital ecosystem, and best practices for creating and executing reliable, scalable, and secure apis are all covered in detail in this.

Pdf Secure Api Design Principles These holes are not always due to negligence. developing secure apis isn’t as simple as it might seem, as the api provider must often strike a balance between ease of use and security. The foundational ideas of apis, their vital role in the digital ecosystem, and best practices for creating and executing reliable, scalable, and secure apis are all covered in detail in this. To proactively reduce the risk of such attacks, it is important to have a thorough understanding of the types of attacks that can target an api and assess their potential impact. this will aid in the implementation of appropriate security controls to keep the api secure. When building or integrating apis, you must also consider how functionality might be misused or abused. identifying, triaging, mitigating, and remediating vulnerabilities in your own custom apis is different from patching vulnerabilities in vendor supplied software. Api design patterns provides a comprehensive guide to reusable patterns for building web apis, starting with foundational design principles and progressing to specific patterns for various api scenarios. Suffice it to say, apis are everywhere and will only gain momentum in the coming years–and they must be protected. for this reason, we’ll examine api attacks and aspects of defense in depth when thinking through organizational api security.
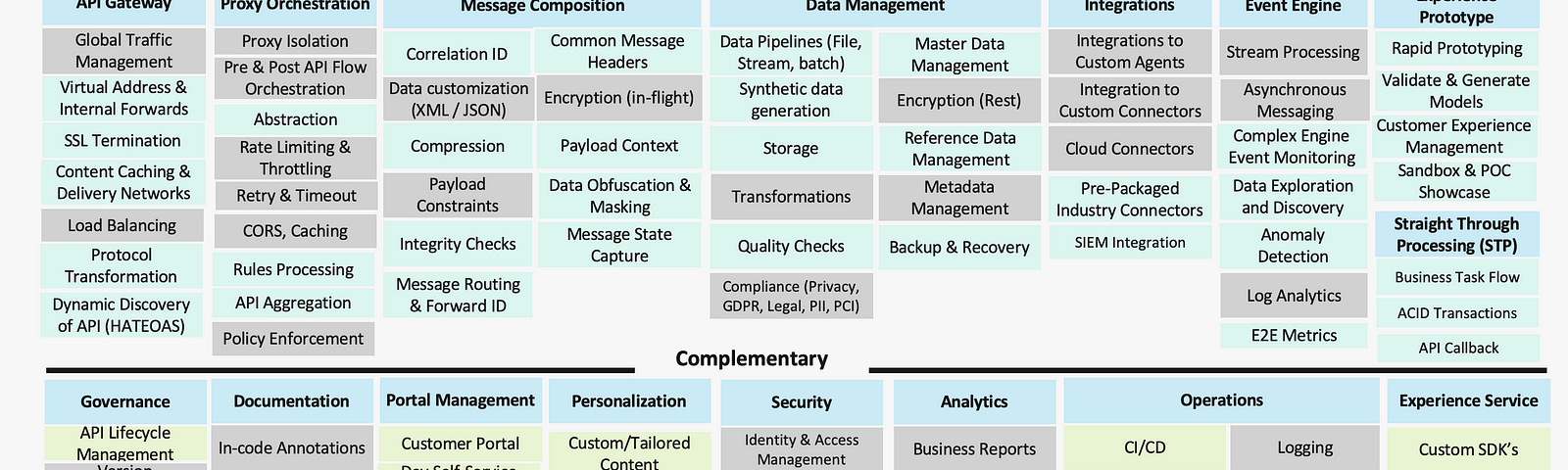
Api Design Principles And Best Practices Medium To proactively reduce the risk of such attacks, it is important to have a thorough understanding of the types of attacks that can target an api and assess their potential impact. this will aid in the implementation of appropriate security controls to keep the api secure. When building or integrating apis, you must also consider how functionality might be misused or abused. identifying, triaging, mitigating, and remediating vulnerabilities in your own custom apis is different from patching vulnerabilities in vendor supplied software. Api design patterns provides a comprehensive guide to reusable patterns for building web apis, starting with foundational design principles and progressing to specific patterns for various api scenarios. Suffice it to say, apis are everywhere and will only gain momentum in the coming years–and they must be protected. for this reason, we’ll examine api attacks and aspects of defense in depth when thinking through organizational api security.
Comments are closed.