Pdf Partially Homomorphic Encryption

Homomorphic Encryption Pdf Cryptography Encryption Pdf | this monograph describes and implements partially homomorphic encryption functions using a unified notation. This monograph describes partially homomorphic encryption functions using a unified notation. it is a systematic examination of the main known algorithms.
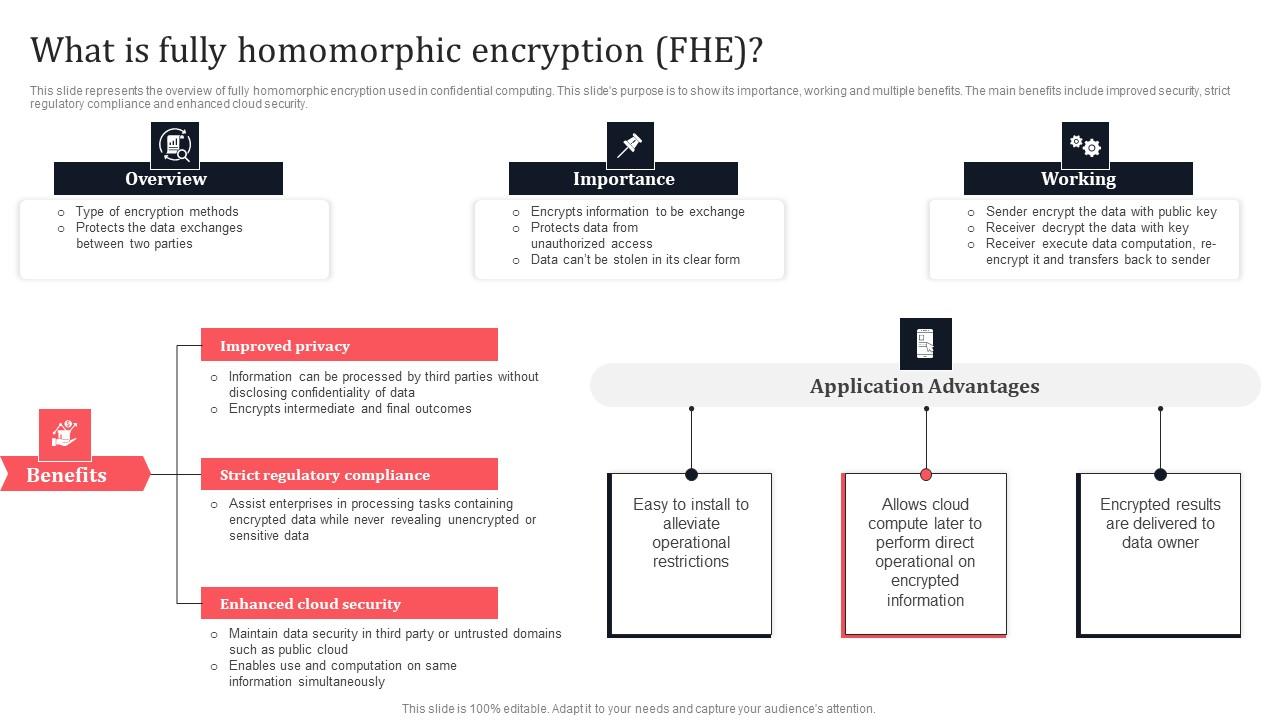
What Is Fully Homomorphic Encryption Fhe Secure Multi Party Graphics Pdf We proposed two homomorphic encryption schemes with reasonable computation and communication costs, and discussed security of our schemes in terms of cipher only attacks. This study presents a comparative evaluation of three representative homomorphic encryption paradigms: partially, somewhat, and fully homomorphic encryption. the implementations are based on the gmp library, microsoft seal, and openfhe. In this paper, we analyze four methods of partially homomorphic encryption among homomorphic encryption meth ods. we compare and analyze the key size and ciphertext size of four partially homomorphic encryptions, paillier, elgamal, ashe, and symmetria. In such case, only the encrypted version of the data is given to the untrusted computer to process. the computer will perform computations on this encrypted data, without knowledge of the original plaintext.

Pdf Privacy Preserving Set Based Estimation Using Partially In this paper, we analyze four methods of partially homomorphic encryption among homomorphic encryption meth ods. we compare and analyze the key size and ciphertext size of four partially homomorphic encryptions, paillier, elgamal, ashe, and symmetria. In such case, only the encrypted version of the data is given to the untrusted computer to process. the computer will perform computations on this encrypted data, without knowledge of the original plaintext. In this paper, we analyze four methods of partially homomorphic encryption among homomorphic encryption methods. we compare and analyze the key size and ciphertext size of four partially homomorphic encryptions, paillier, elgamal, ashe, and symmetria. Partially homomorphic encryption (with regard to multiplicative operations) is the foundation for rsa encryption, which is commonly used in establishing secure connections through ssl tls. Two symmetric partially homomorphic encryption schemes. after some security analyses, we show that the multiplicative homomorphic en cryption scheme and the additive homomorphic encryption scheme can achieve perfect secrecy, i.e., given any ciphertext, the cryptanalyst who does not know the secret. Considering the overwhelming presence of computers with limited resources, the presence of the internet and the ultimate practical need for use of cloud and its resources, in this paper we explored.

Homomorphic Encryption Outsourcing Computation In this paper, we analyze four methods of partially homomorphic encryption among homomorphic encryption methods. we compare and analyze the key size and ciphertext size of four partially homomorphic encryptions, paillier, elgamal, ashe, and symmetria. Partially homomorphic encryption (with regard to multiplicative operations) is the foundation for rsa encryption, which is commonly used in establishing secure connections through ssl tls. Two symmetric partially homomorphic encryption schemes. after some security analyses, we show that the multiplicative homomorphic en cryption scheme and the additive homomorphic encryption scheme can achieve perfect secrecy, i.e., given any ciphertext, the cryptanalyst who does not know the secret. Considering the overwhelming presence of computers with limited resources, the presence of the internet and the ultimate practical need for use of cloud and its resources, in this paper we explored.
Comments are closed.