Pdf On Modeling Eavesdropping Attacks In Wireless Networks

Wireless Attacks Pdf Information And Communications Technology Pdf | on aug 1, 2016, hong ning dai and others published on eavesdropping attacks in wireless networks | find, read and cite all the research you need on researchgate. In this paper, we propose an analytical framework to model the eavesdropping attacks in wireless networks with consideration of both channel conditions and antenna models.

Pdf Eavesdropping Attacks In Wireless Ad Hoc Networks Under A Shadow In this paper, we originally received in revised form 24 october 2014 propose an analytical framework to quantify the effective area and the probability of the eavesdropping accepted 31 october 2014 attacks. We propose an analytical framework to investigate the eavesdropping attacks, taking account into various channel conditions and antenna models. This paper concerns the eavesdropping attacks from the eavesdroppers’ perspective, which is new since most of current studies consider the problem from the good nodes’ perspective. In this paper, we propose a general analytical framework to quantify the eavesdropping probability in wireless networks with consideration of various factors, such as node density and impacts of channel conditions. we validate the accuracy of our proposed model by conducting extensive simulations.

Pdf Eavesdropping In Bluetooth Networks This paper concerns the eavesdropping attacks from the eavesdroppers’ perspective, which is new since most of current studies consider the problem from the good nodes’ perspective. In this paper, we propose a general analytical framework to quantify the eavesdropping probability in wireless networks with consideration of various factors, such as node density and impacts of channel conditions. we validate the accuracy of our proposed model by conducting extensive simulations. We briefly described and simulated two types of advanced attacks, i.e. antenna randomization attack and noise cancellation attack. while other advanced attacks remain possible, current mmwave hardware is not flexible enough to implement these attacks. This paper discusses eavesdropper attack strategies for 802.11ad mmwave systems and provides the rst analytical model to characterize the success possibility of eavesdropping in both opportunistic stationary attacks and active nomadic attacks. Active eavesdropping detection is a physical layer security based method that can diferentiate wireless signals between wireless devices through feature classification. Abstract we formalize a model for node capture attacks in which an adversary collects information about the network via eavesdropping on the wireless medium and captures nodes based on the learned information.
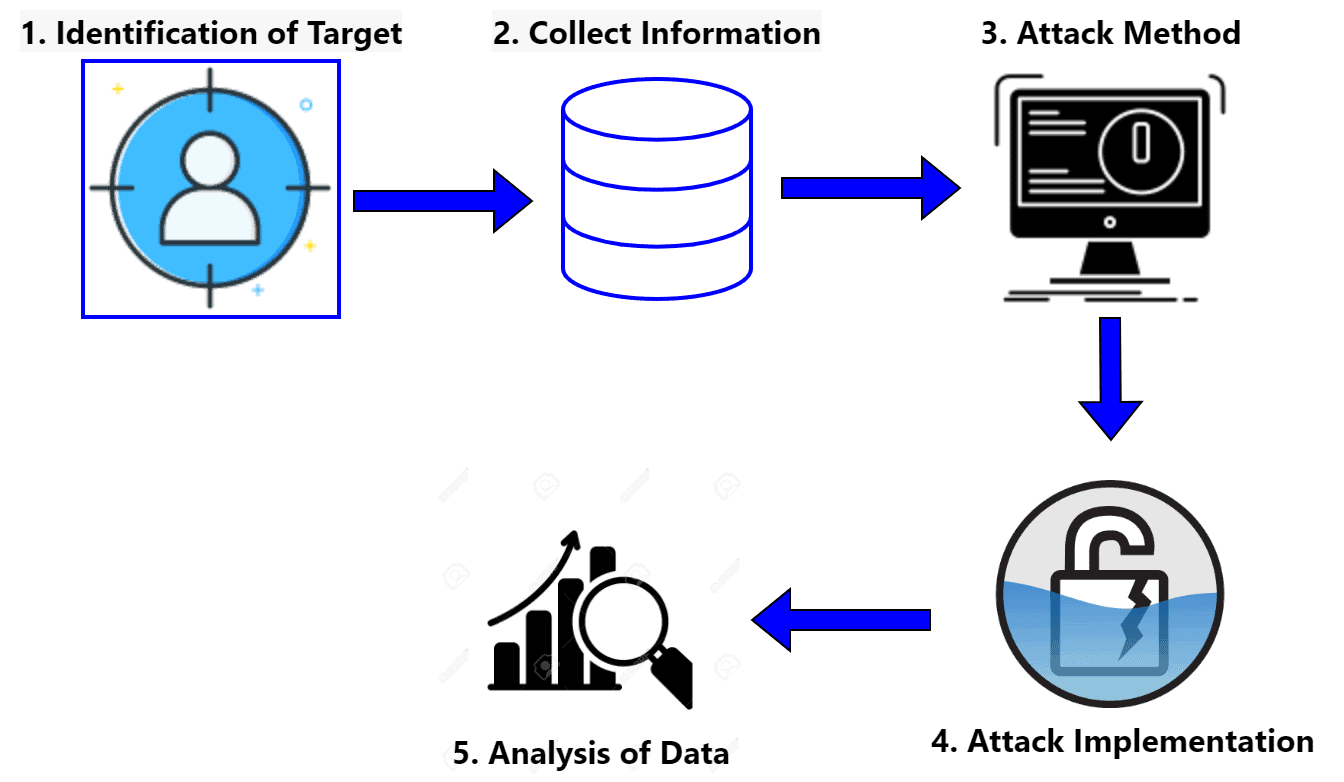
What Is An Eavesdropping Attack Baeldung On Computer Science We briefly described and simulated two types of advanced attacks, i.e. antenna randomization attack and noise cancellation attack. while other advanced attacks remain possible, current mmwave hardware is not flexible enough to implement these attacks. This paper discusses eavesdropper attack strategies for 802.11ad mmwave systems and provides the rst analytical model to characterize the success possibility of eavesdropping in both opportunistic stationary attacks and active nomadic attacks. Active eavesdropping detection is a physical layer security based method that can diferentiate wireless signals between wireless devices through feature classification. Abstract we formalize a model for node capture attacks in which an adversary collects information about the network via eavesdropping on the wireless medium and captures nodes based on the learned information.
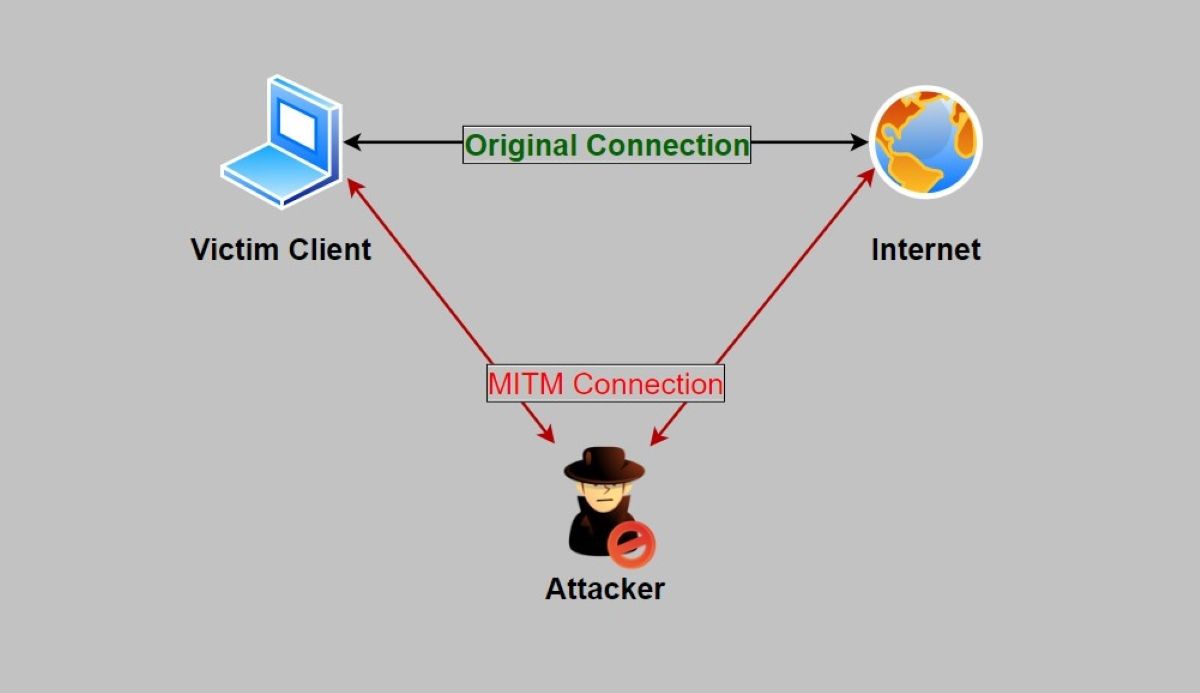
Eavesdropping Attack Understanding Eavesdropping Attacks In Network Active eavesdropping detection is a physical layer security based method that can diferentiate wireless signals between wireless devices through feature classification. Abstract we formalize a model for node capture attacks in which an adversary collects information about the network via eavesdropping on the wireless medium and captures nodes based on the learned information.

Pdf Attacks Detection In 6g Wireless Networks Using Machine Learning
Comments are closed.