Pdf Non Profiled Side Channel Attack Based On Deep Learning Using

Scadl A New Side Channel Attack Tool Using Deep Learning Ledger In this work, we propose a unique method to improve deep learning based side channel analysis by converting the measurements from raw trace of 1 dimension data based on float or byte data. Abstract. this paper formally analyzes two major non profiled deep learning based side channel attacks (dl scas): diferential deep learning analysis (ddla) by timon and collision dl sca by staib and moradi. these dl scas leverage supervised learning in non profiled scenarios.

Black Hat Talk A Hacker S Guide To Reducing Side Channel Attack In this work, we propose a unique method to improve deep learning based side channel analysis by converting the measurements from raw trace of 1 dimension data based on float or byte data into picture formatted trace that has information based on the data position. In this paper, we propose an sca evaluation technique using the multi output regression neural network, which can simultaneously estimate all key hypotheses in a single training process. consequently, the performance of non profiled dl based sca can improve significantly. We propose a new deep learning based sca in a non profiled scenario to solve these problems. our core idea is to extract feature of the leakage waveform using dnn. the adversary reveals the correct keys by conducting cluster analysis using the feature vectors extracted from power traces using dnn. This document presents a novel nonprofiled side channel attack technique utilizing multi output classification neural networks to enhance the speed and accuracy of key prediction in embedded systems.
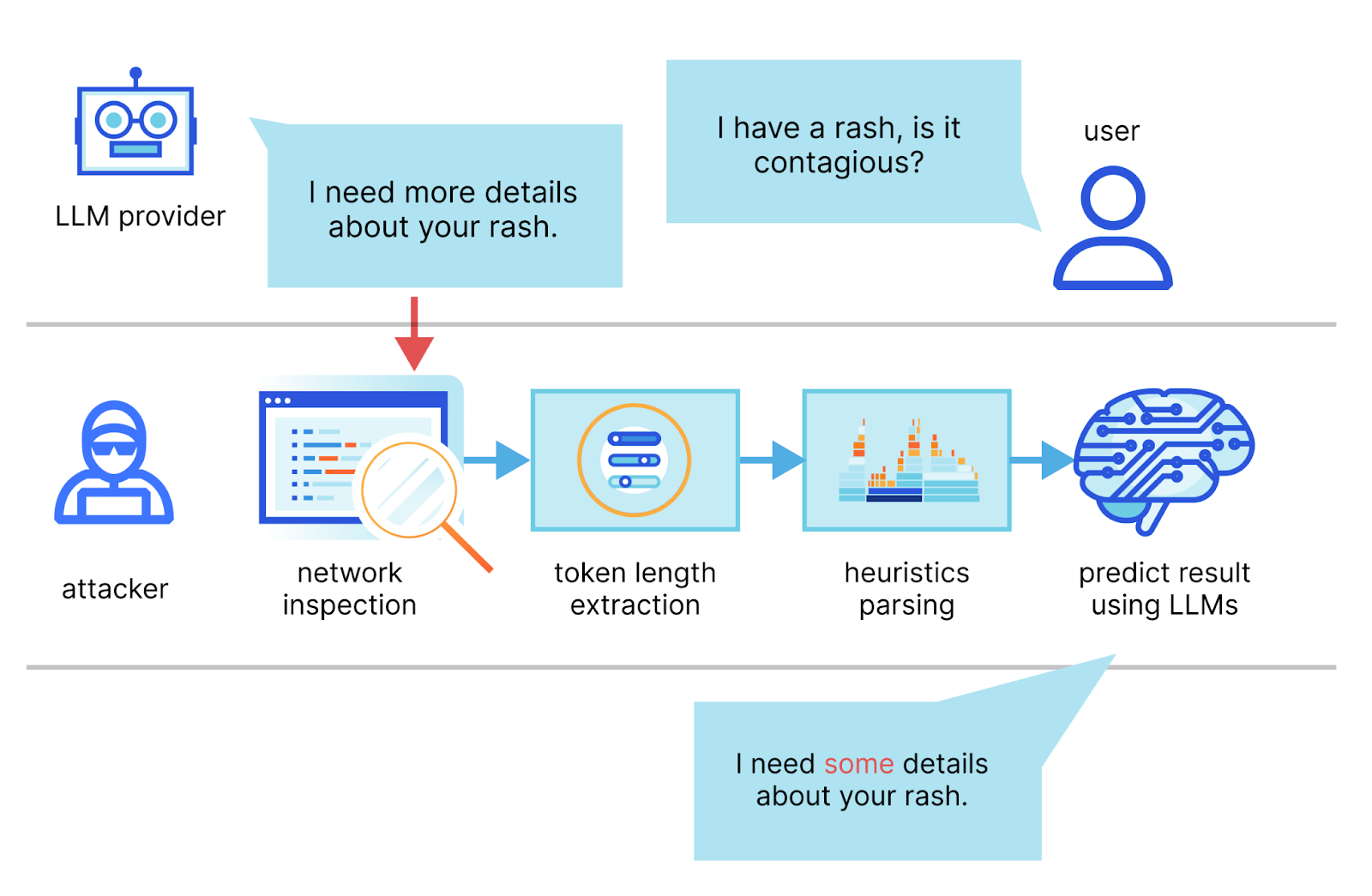
Mitigating A Token Length Side Channel Attack In Our Ai Products We propose a new deep learning based sca in a non profiled scenario to solve these problems. our core idea is to extract feature of the leakage waveform using dnn. the adversary reveals the correct keys by conducting cluster analysis using the feature vectors extracted from power traces using dnn. This document presents a novel nonprofiled side channel attack technique utilizing multi output classification neural networks to enhance the speed and accuracy of key prediction in embedded systems. In this study, we propose and investigate the use of deep learning (dl) techniques to enhance the effectiveness of non profiled scas through an optimized deep learning power analysis (dlpa) algorithm. Abstract side channel attacks (scas) using deep learning techniques have been mainly reported as profiled attacks, but in tches 2019, differential deep learning analysis (ddla) was proposed by timon as a non profiled attack. In our study, we investigate the structure of dnn models and attack points (poi: points of interests) for non profiled dl scas using the anssi sca database with a masking countermeasure. This work proposes a custom deep learning (dl) method to model the power trace that can effectively mitigate the risk of side channel attacks and enhance the overall security of software systems.
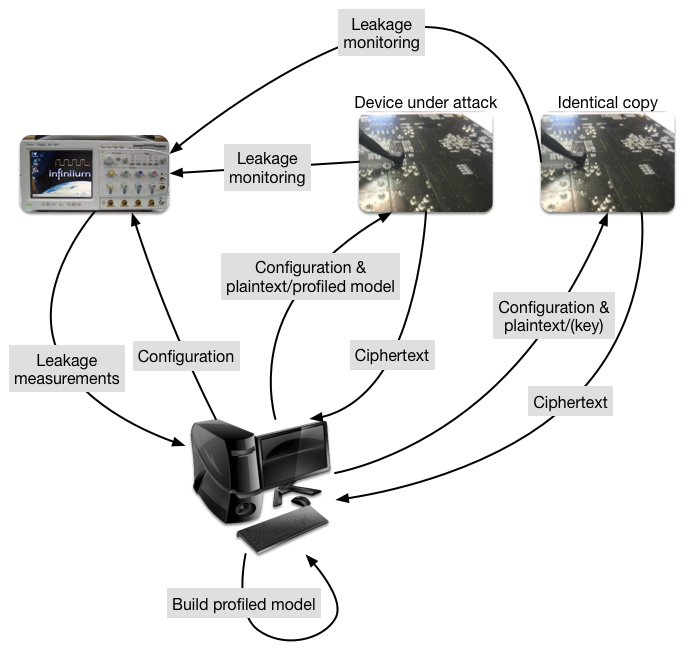
No Ai Did Not Break Post Quantum Cryptography In this study, we propose and investigate the use of deep learning (dl) techniques to enhance the effectiveness of non profiled scas through an optimized deep learning power analysis (dlpa) algorithm. Abstract side channel attacks (scas) using deep learning techniques have been mainly reported as profiled attacks, but in tches 2019, differential deep learning analysis (ddla) was proposed by timon as a non profiled attack. In our study, we investigate the structure of dnn models and attack points (poi: points of interests) for non profiled dl scas using the anssi sca database with a masking countermeasure. This work proposes a custom deep learning (dl) method to model the power trace that can effectively mitigate the risk of side channel attacks and enhance the overall security of software systems.

A Quantitative Analysis Of Non Profiled Side Channel Attacks Based On In our study, we investigate the structure of dnn models and attack points (poi: points of interests) for non profiled dl scas using the anssi sca database with a masking countermeasure. This work proposes a custom deep learning (dl) method to model the power trace that can effectively mitigate the risk of side channel attacks and enhance the overall security of software systems.
Comments are closed.