Pdf Malicious Url Detection Based On Associative Classification
Malicious Url Detection Pdf Malware Phishing In this paper, we use the classification based on association (cba) algorithm to detect malicious urls by utilizing both url and webpage content features. In this paper, a data mining approach known as classification based on association (cba) to detect malicious urls using url and webpage content features is presented.

Pdf Malicious Url Detection Based On Associative Classification In this paper, a data mining approach known as classification based on association (cba) to detect malicious urls using url and webpage content features is presented. the cba. A data mining approach known as classification based on association (cba) to detect malicious urls using url and webpage content features is presented and shows that cba gives comparable performance against benchmark classification algorithms. Treating the problem as a multi class classification challenge, raw urls are categorized into different types, including benign or safe urls, phishing urls, malware urls, and defacement urls using various machine learning algorithms. The results demonstrated the possibility of using associative classification in real application to detect phishing. however, they did deploy their model for real world application and problemsolving.
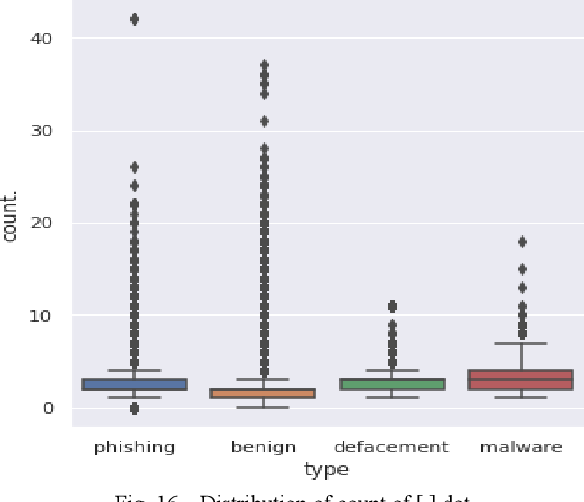
Figure 16 From Malicious Url Detection And Classification Analysis Treating the problem as a multi class classification challenge, raw urls are categorized into different types, including benign or safe urls, phishing urls, malware urls, and defacement urls using various machine learning algorithms. The results demonstrated the possibility of using associative classification in real application to detect phishing. however, they did deploy their model for real world application and problemsolving. Article “malicious url detection based on associative classification” detailed information of the j global is a service based on the concept of linking, expanding, and sparking, linking science and technology information which hitherto stood alone to support the generation of ideas. Cybercriminals use malicious urls as distribution channels to propagate malware over the web. attackers exploit vulnerabilities in browsers to install malware to have access to the victim’s computer remotely. This paper presents a comprehensive review of malicious url detection technologies, systematically analyzing methods from traditional blacklisting to advanced deep learning ap proaches (e.g. transformer, gnns, and llms).
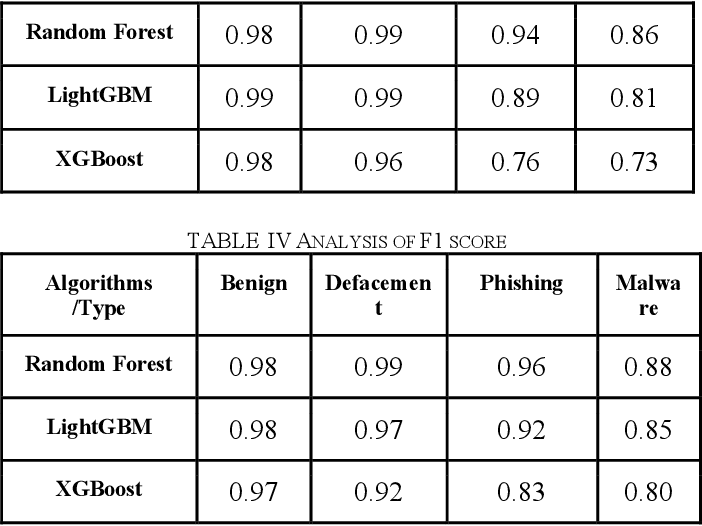
Table Iv From Malicious Url Detection And Classification Analysis Using Article “malicious url detection based on associative classification” detailed information of the j global is a service based on the concept of linking, expanding, and sparking, linking science and technology information which hitherto stood alone to support the generation of ideas. Cybercriminals use malicious urls as distribution channels to propagate malware over the web. attackers exploit vulnerabilities in browsers to install malware to have access to the victim’s computer remotely. This paper presents a comprehensive review of malicious url detection technologies, systematically analyzing methods from traditional blacklisting to advanced deep learning ap proaches (e.g. transformer, gnns, and llms).
Comments are closed.