Pdf Insider Threat Detection Using Graph Based Approaches

Ieee Warder Online Insider Threat Detection System Using We present the use of graph based approaches to discovering anomalous instances of structural patterns in data that represent insider threat activity. the approaches presented search for. Abstract. we present the use of graph based approaches to discovering anomalous instances of structural patterns in data that represent insider threat activity. the approaches presented search for activities that appear to match normal transactions, but in fact are structurally different. we show the usefulness of applying graph theoretic.

A Graph Based Framework For Malicious Insider Threat Detection Deepai In order to address this issue, this effort involves performing further research and development on the existing graph based anomaly detection (gbad) system. gbad discovers anomalous instances of structural patterns in data that represent entities, relationships and actions. In order to study the design and effectiveness of graph based insider threat detection, in this paper, we conduct a systematic and comprehensive survey of existing related research. In this paper, we introduce the community anomaly detection system (cads), an unsupervised learning framework to detect insider threats based on the access logs of collaborative environments. We propose a novel approach that combines explicit and implicit graph structures for insider threat detection. this integration leverages the strengths of both graph types, capturing both direct, observable interactions and refined, optimised relationships derived from feature similarities.

Insider Threat Detection Powerpoint Templates Slides And Graphics In this paper, we introduce the community anomaly detection system (cads), an unsupervised learning framework to detect insider threats based on the access logs of collaborative environments. We propose a novel approach that combines explicit and implicit graph structures for insider threat detection. this integration leverages the strengths of both graph types, capturing both direct, observable interactions and refined, optimised relationships derived from feature similarities. This review paper examines various graph based approaches applied to cybersecurity, including intrusion detection, malware analysis, and insider threat detection. The document discusses a graph based approach for detecting insider threats by identifying anomalous structural patterns in data that resemble normal transactions but are structurally different. In order to offer more solutions in insider threat detection re garding feature engineering, and considering that an employee’s workload would most likely show pattern according to calendar day, we first propose a daily activity based feature engineering approach. The authors show the usefulness of applying graph theoretic approaches to discovering suspicious insider activity in domains such as social network communications, business processes, and cybercrime.
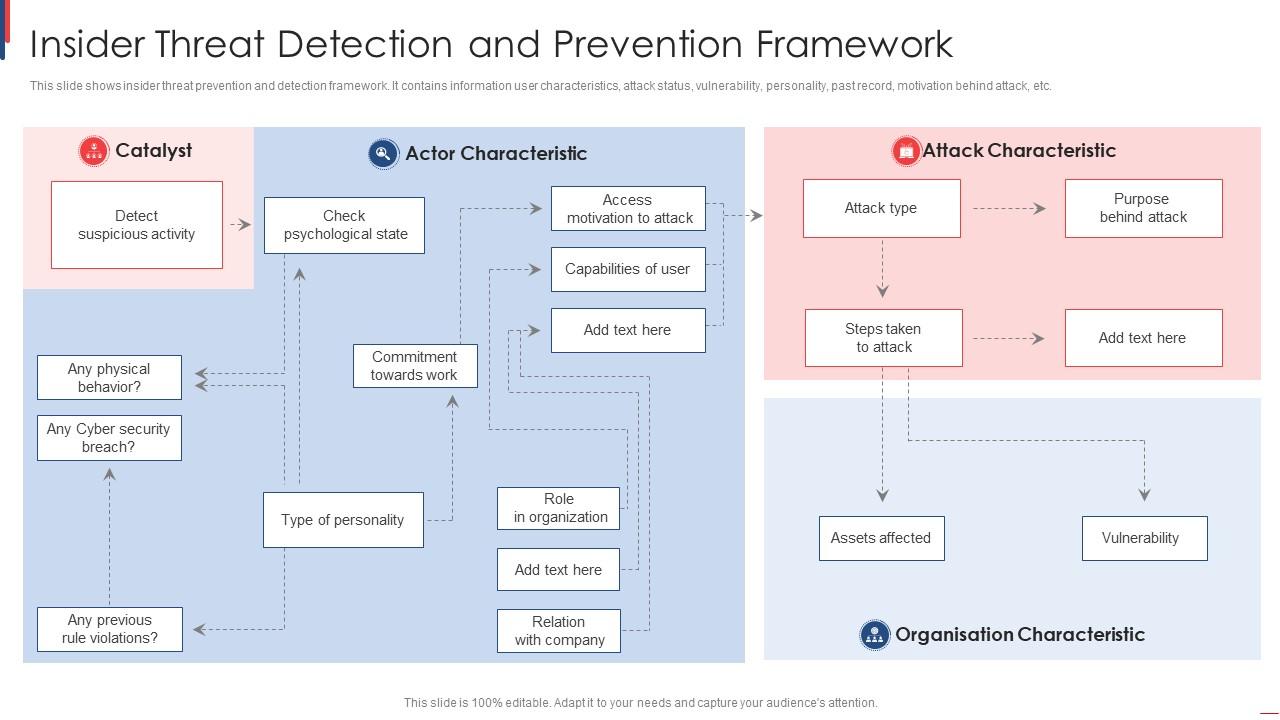
Insider Threat Detection And Prevention Framework Ppt Presentation This review paper examines various graph based approaches applied to cybersecurity, including intrusion detection, malware analysis, and insider threat detection. The document discusses a graph based approach for detecting insider threats by identifying anomalous structural patterns in data that resemble normal transactions but are structurally different. In order to offer more solutions in insider threat detection re garding feature engineering, and considering that an employee’s workload would most likely show pattern according to calendar day, we first propose a daily activity based feature engineering approach. The authors show the usefulness of applying graph theoretic approaches to discovering suspicious insider activity in domains such as social network communications, business processes, and cybercrime.
Pdf Automated Insider Threat Detection System Using User And Role In order to offer more solutions in insider threat detection re garding feature engineering, and considering that an employee’s workload would most likely show pattern according to calendar day, we first propose a daily activity based feature engineering approach. The authors show the usefulness of applying graph theoretic approaches to discovering suspicious insider activity in domains such as social network communications, business processes, and cybercrime.

Insider Threat Detection With Ml Techniques Pdf Machine Learning
Comments are closed.