Pdf Ensure Data Security In Cloud Computing By Using Cryptography

About Cloud Cryptography Cloud Data Security Using Cryptography Mockup Pdf In this research paper, we are focusing on what encryption a client need before choosing a cloud provider, because good encryption will help you protect your data when you share it or use it,. In order to ensure confidentiality at every stage of processing, this article presents an innovative strategy that merges fully homomorphic encryption (fhe) and secure hash algorithm 3 (sha 3), offering robust protection against cyber threats. fhe and sha 3 offer a solution to this problem.
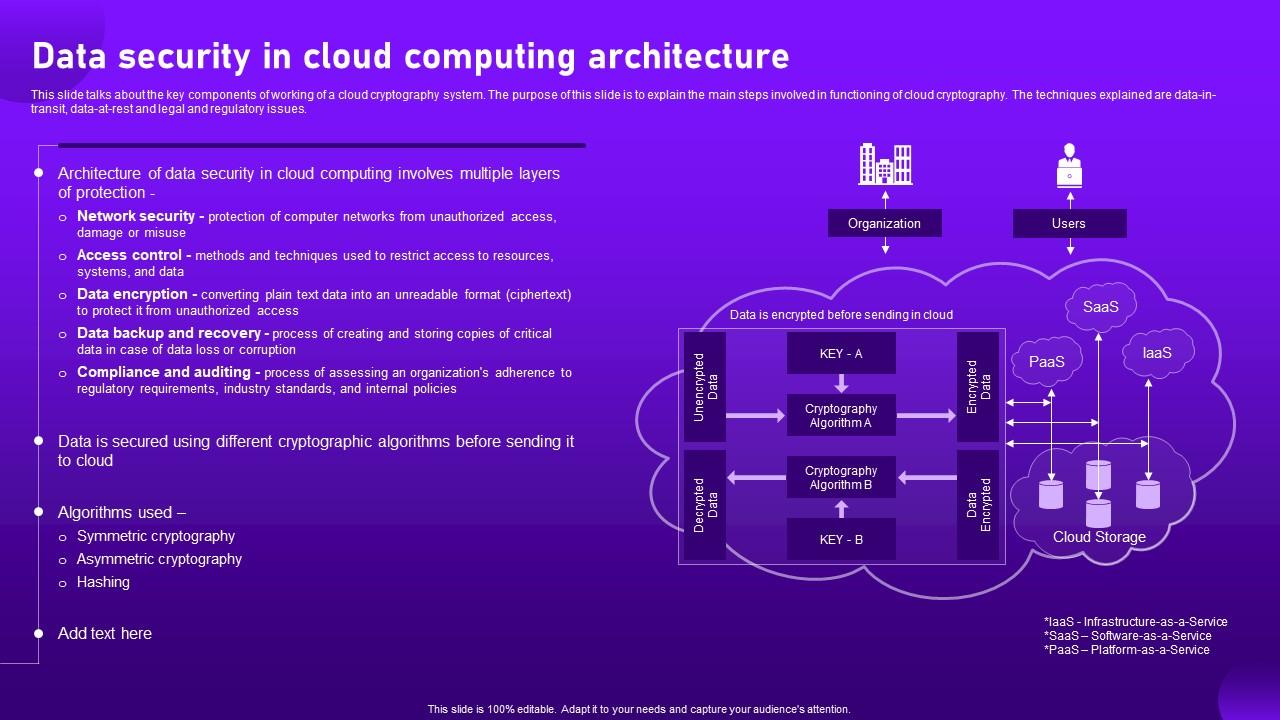
Data Security In Cloud Computing Architecture Cloud Cryptography Ppt This initiative seeks to foster dialogue among researchers and practitioners to address cryptography and data security challenges in cloud computing, with a focus on improving existing solutions and advancing the field. Cloud computing has revolutionized data storage, providing scalable and cost effective solutions. however, security concerns persist due to unauthorized access and data breaches. this paper presents a hybrid cryptographic system integrating aes and rsa encryption techniques for secure cloud storage. The essential necessity of such applications, where data are being exchanged or transmitted between the servers and their users, is the secure data storage on cloud environments. in this research, we use cloud based cryptography, one of the best methods for secure communication. This paper aims to create a data security model based on cryptography and steganography for data in cloud computing that seeks to reduce existing security and privacy concerns, such as data loss, data manipulation, and data theft.
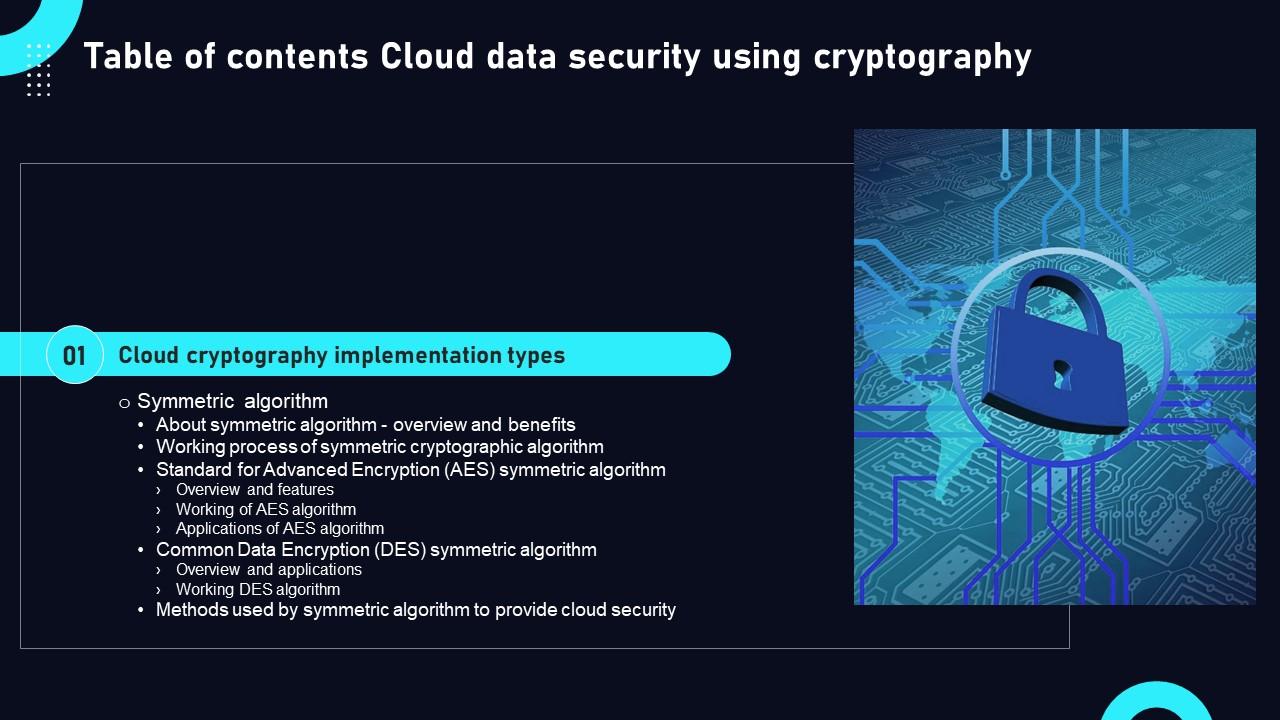
Cloud Data Security Using Cryptography Table Of Contents Inspiration Pdf The essential necessity of such applications, where data are being exchanged or transmitted between the servers and their users, is the secure data storage on cloud environments. in this research, we use cloud based cryptography, one of the best methods for secure communication. This paper aims to create a data security model based on cryptography and steganography for data in cloud computing that seeks to reduce existing security and privacy concerns, such as data loss, data manipulation, and data theft. In such a case, cryptography in cloud computing ensures reliability and integrity of online storage and transmission of data. this paper deals with some efficient functions and methodologies to ensure the data is ciphered and is kept protected. This study provided a recent review of cloud security issues, challenges, and threats to cloud adoption, and encryption algorithms that are used in cloud environments. a comparison was made between the most important encryption algorithms that can be used to provide greater cloud security. These technologies ensure that data remains confidential and secure, even when stored in third party cloud infrastructures. this white paper explores the challenges faced in cloud data protection and how cryptographic techniques provide solutions for securing data in these environments. This paper examines a variety of cryptographic methods used by major cloud providers. it proposes an alternative algorithm for encrypting data in transit from the user to the cloud in order to ensure data security and defend against man in the middle (mitm) attacks like sniffing.
Cloud Security Lecture 1 Pdf Cryptography Encryption In such a case, cryptography in cloud computing ensures reliability and integrity of online storage and transmission of data. this paper deals with some efficient functions and methodologies to ensure the data is ciphered and is kept protected. This study provided a recent review of cloud security issues, challenges, and threats to cloud adoption, and encryption algorithms that are used in cloud environments. a comparison was made between the most important encryption algorithms that can be used to provide greater cloud security. These technologies ensure that data remains confidential and secure, even when stored in third party cloud infrastructures. this white paper explores the challenges faced in cloud data protection and how cryptographic techniques provide solutions for securing data in these environments. This paper examines a variety of cryptographic methods used by major cloud providers. it proposes an alternative algorithm for encrypting data in transit from the user to the cloud in order to ensure data security and defend against man in the middle (mitm) attacks like sniffing.
Comments are closed.